27 countries sign cybersecurity pledge with digs at China and Russia | Big tech loses $56 Billion after Trump speech | Sandberg outlines Silicon Valley's plan to fight online extremism


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
Twenty-seven countries have signed a joint agreement on what constitutes fair and foul play in cyberspace — with a nod toward condemning China and Russia. The statement, released on Monday at the United Nations ahead of the beginning of the UN General Assembly's General Debate, is largely a broadly written agreement that countries should follow international law. CNN
U.S. President Donald Trump’s address to the United Nations General Assembly helped knock $56 billion off the value of some of the biggest technology companies. Bloomberg
Some of Silicon Valley's biggest companies announced Monday that they're revamping an organization they established to fight online extremism in order to allow it to work more extensively with outside parties. The announcement, which came on the sidelines of the United Nations General Assembly in New York, comes six months after the suspect in the New Zealand mosque shooting streamed the massacre live on Facebook. CNN
ASPI ICPC

Australia's Cyber Strategy, version 2.0
ASPI ICPC
Back in 2016, Australia launched its first national cybersecurity strategy. The strategy covers a four-year period to 2020, and given the changes in the security environment, an update is now clearly warranted. To that end, the government has just launched a discussion paper to kick off the public consultation. The closing date for submissions on the discussion paper is 1 November.To complement the public submission process, ASPI’s International Cyber Policy Centre is initiating a public debate on what should be included in the next cybersecurity strategy. Contributions will be compiled into a report that we will deliver to the Department of Home Affairs to inform the strategy’s development.
China and Russia aren’t the same when it comes to information warfare
The Strategist
@JakeWallis_ASPI
A range of states are willing to exploit social media to achieve their goals by shaping geopolitical narratives, warping the media and information environment to their advantage, and fooling people into believing something they shouldn’t. But states can have very different approaches and goals. And if we look at two of the biggest players in this arena—Russia and China—their operations have very different strategic goals and typically use quite different tactics.
The Rohingya’s right of no return
The New York Times
@DSMathiesonHRW
Yet the BBC and the Australian Strategic Policy Institute have reported the widespread destruction of former Rohingya villages in Rakhine, challenging the Myanmar government’s claim that it is doing its part to ensure the refugees’ safe and dignified return. Satellite images confirm that an archipelago of confinement camps has been erected in the place of the villages — a gulag in the waiting, in which any Rohingya who did return would likely see their rights and freedoms even more restricted than before.
ASPI ICPC joints the Christchurch Call Advisory Network
Christchurch Call
The Christchurch Call Advisory Network membership has been drawn from interested civil society groups, who represent a range of perspectives, including human rights, freedom of expression, digital rights, counter-radicalization, victim support and public policy. Many of the Advisory Network members have been engaged on the Christchurch Call since its launch and are committed to continuing to share their expertise.
The World
27 countries sign cybersecurity pledge with digs at China and Russia
CNN
@kevincollier
Twenty-seven countries have signed a joint agreement on what constitutes fair and foul play in cyberspace — with a nod toward condemning China and Russia. The statement, released on Monday at the United Nations ahead of the beginning of the UN General Assembly's General Debate, is largely a broadly written agreement that countries should follow international law.
Big Tech Loses $56 Billion in Market Cap After Trump’s UN Speech
Bloomberg
@SarahPonczek
U.S. President Donald Trump’s address to the United Nations General Assembly helped knock $56 billion off the value of some of the biggest technology companies.
Australia
Australians are reporting cybercrime activities once every 10 minutes
ZDNet
@ashabeeeee
The new head of the Australian Cyber Security Centre has said financial loss from cybercrime down under is ticking through to the billions.
How to survive a cyber attack
The Sydney Morning Herald
@NinaHendy @yanzhuang25
John is one of thousands of Australians who have their identity stolen each year. Recent estimates by the Attorney-General’s Department indicate that identity crime costs more than $1.6 billion annually.
Huawei or the highway, Chinese academics warn
The Australian
@bennpackham
Chinese academics on a state-sponsored speaking tour say Australia won’t be taken out of Beijing’s diplomatic freezer until it relaxes its 5G ban on Chinese telco Huawei.
AustCyber launches Canberra Cyber Security Innovation Node
Technology Decisions
Canberra’s cybersecurity capabilities are set to move up a gear under a partnership between AustCyber and the Australian Capital Territory (ACT) Government.
Finance breaches highlight need for internal cyber vigilance
CSO
The recent data breaches at Capital One and National Australia Bank (NAB) reinforce the evidence that human error represents a serious threat to organisations in finance.
New research centre receives AU$62m to study children's digital lives
ZDNet
@achanthadavong
The ARC Centre of Excellence for the Digital Child will examine the digital lives of Australian children from birth to eight years old.
China
Privacy concerns over 500 MP cloud camera
Asia Times
Chinese scientists have developed an artificial intelligence-enabling 500 megapixel cloud camera system able to capture thousands of faces at a stadium in perfect detail and generate their facial data for the cloud while locating a particular target in an instant, Global Times reported. Most Chinese experts welcomed the camera system’s military, national defense and public security applications, although, so great is the camera’s capability, some expressed data safety and privacy concerns.
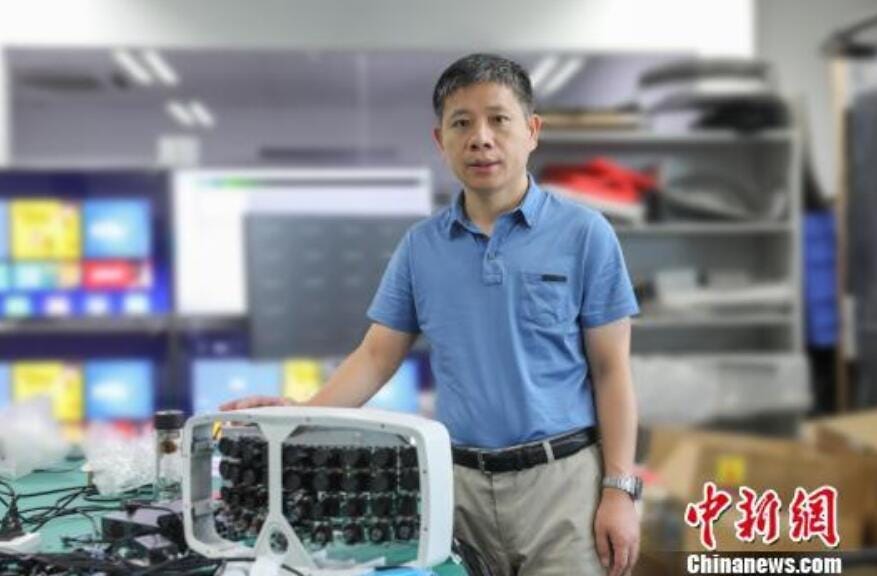
Fudan University Professor Zeng Xiaoyang with the 500 megapixel cloud camera system his team developed. (Source: Chinanews.com)
Are Chinese And Western Perspectives Incompatible In Our Post-Truth Times?
SupChina
If international study programs cannot resolve China’s panoply of abuses in Xinjiang (no one expects this), at the very least they can distance themselves from these. The selection of SenseTime’s CEO as the commencement speaker for Schwarzman’s graduation ceremony did exactly the opposite. This event again exposed competing realities between some Chinese and Western students. In his speech, the CEO described as “fake news” reports that SenseTime’s facial recognition software was used in Xinjiang. This was met by rapturous laughter from some Chinese students. It was met by muted fury from many Western students.
WhatsApp Fakes Hack Tibetan iPhones And Androids To Steal Facebook Data And More
Forbes
@iblametom
High-profile Tibetans have seen their Apple iPhones and Android devices targeted by hacks delivered in WhatsApp messages. All that was required for their device to have a permanent tracker installed on their mobile was a single click of the link within the WhatsApp text, researchers claimed. It’s being labeled the most sophisticated attack on Tibetans yet, after attempts were made to steal WhatsApp and Facebook chats as well as locations with some novel techniques.
Missing link: Tibetan groups targeted with 1-click mobile exploits
Citizenlab
@billmarczak
Between November 2018 and May 2019, senior members of Tibetan groups received malicious links in individually tailored WhatsApp text exchanges with operators posing as NGO workers, journalists, and other fake personas. The links led to code designed to exploit web browser vulnerabilities to install spyware on iOS and Android devices, and in some cases to OAuth phishing pages. This campaign was carried out by what appears to be a single operator that we call POISON CARP. This campaign is the first documented case of one-click mobile exploits used to target Tibetan groups, and reflects an escalation in the sophistication of digital espionage threats targeting the community.
Someone is doxing Hong Kong protesters and journalists — and China wants them to keep going
Buzzfeed
@rosalindzadams @janelytv
Days after an activist was doxed, thugs brutally attacked him outside his home. The site with information on him and more than 100 others is being spread by Chinese state media.
USA
Sheryl Sandberg outlines Silicon Valley's plan to fight online extremism
CNN
@donie
Some of Silicon Valley's biggest companies announced Monday that they're revamping an organization they established to fight online extremism in order to allow it to work more extensively with outside parties. The announcement, which came on the sidelines of the United Nations General Assembly in New York, comes six months after the suspect in the New Zealand mosque shooting streamed the massacre live on Facebook.
Facebook, Elections and Political Speech
Facebook Newsroom
@nick_clegg
Speaking at the Atlantic Festival in Washington DC today, I set out the measures that Facebook is taking to prevent outside interference in elections and Facebook’s attitude towards political speech on the platform. This is grounded in Facebook’s fundamental belief in free expression and respect for the democratic process, as well as the fact that, in mature democracies with a free press, political speech is already arguably the most scrutinized speech there is.
Chinese theft of trade secrets on the rise, the US Justice Department warns
CNBC
@NancyCNBC
As President Donald Trump puts pressure on Beijing to end unfair business practices, the Department of Justice has a warning for companies: Bolster your defenses. "More cases are being opened that implicate trade secret theft" — and more of them point to China, said U.S. Deputy Assistant Attorney General Adam Hickey. Since 2012, more than 80% of economic espionage cases brought by the department's National Security Division have implicated China. The frequency of cases has been rising in recent years, according to Hickey.
Company That Provides Tech to ICE Not Renewing Contract After Code-Deletion Protest
Vice
@josephfcox
A software firm called Chef that provides products to some of the biggest companies on the planet is not renewing its contract with U.S. Immigration and Customs Enforcement (ICE). The move comes after a former employee of the company deleted code that can be used with the software in protest over the company's work with ICE.
Facebook buys startup building neural monitoring armband
TechCrunch
@lucasmtny
Facebook is buying CTRL-labs, a NY-based startup building an armband that translates movement and the wearer’s neural impulses into digital input signals, a company spokesperson tells TechCrunch.
Air Force unveils information warfare outfit amid U.S. effort to go on offense in cyberspace
Cyberscoop
@shanvav
After months of planning, the U.S. Air Force announced it is creating a new information warfare body, an official step that aims to bolster the military’s digital warfare capabilities.
Google contractors officially vote to unionize
Vice
The contractors work at a company called HCL, which strongly encouraged its employees to vote against the union.
North Asia
Japanese govt seeks AI system for predicting cyber-attacks
Japan News
The government will undertake a research and development project to use artificial intelligence to automatically detect signs of cyber-attacks and evaluate their potential impact, The Yomiuri Shimbun has learned.
Southeast Asia
The Philippines to join the APEC Cross-Border Privacy Rules System
OpenGov Asia
The Philippines has formally joined the Cross-Border Privacy Rules (CBPR) System, according to a recent press release. This move is seen to expand the country’s trading opportunities within the Asia Pacific region by eliminating data-flow barriers when transacting with member economies of the Asia Pacific Economic Cooperation (APEC) through the adaption of common standards for data privacy.
South Asia
Won’t invest more if denied 5G permission, says Huawei
Times of India
Embattled Chinese telecom equipment provider Huawei has said that it is ready to invest in an export oriented 5G manufacturing facility in India, but any expansion would be contingent on the government’s nod for its participation in the latest telecom technology.
Europe
You have the right to be forgotten by Google - but only in Europe
Reuters
@FooYunChee
Google will not have to apply Europe’s “right to be forgotten” law globally, the continent’s top court ruled on Tuesday in a landmark case that has pitted personal privacy rights against freedom of speech.
Which European companies are working in Xinjiang
ChinaFile
@haasbenjamin
Foreign companies continue to conduct business in Xinjiang despite widespread evidence of human rights abuse. Some firms may even unwittingly benefit from the detentions. Supply chains for major clothing companies such as Adidas, H&M, and Esprit have become entangled with labor supplied by the camps, according to The Wall Street Journal. Other firms working in Xinjiang have drawn far less media attention. Siemens, which has a branch office in Urumqi and sells technology components across Xinjiang, has also partnered with China Electronics Technology Group Corporation (CETC), a state-owned military contractor, to work on automation, digitization, and networking. CETC developed a policing app used in Xinjiang and its algorithms have sent people to the detention camps, according to a Human Rights Watch report. Telefonica, a Spanish communications company, has partnered with China Unicom to deploy anonymized population-tracking software in the region. In the list below, I have identified 68 European companies with ties to Xinjiang.
Russia
Russia Tests Face, Voice Recognition Ahead of eSIM Integration
The Moscow Times
Russia is testing face- and voice-recognition technology to identify mobile device users as it moves toward approving eSIM technology which allows consumers to switch easily between carriers, the pro-Kremlin Izvestia newspaper has reported.
Political targets at risk as Fancy Bear returns with refreshed backdoor malware
ZDNet
@SecurityCharlie
A new Fancy Bear campaign has been discovered by ESET. Launched at victims on the usual hit-list -- including Ministries of Foreign Affairs and embassies across Europe and Asia -- and tracked in August, the group is making use of phishing emails tied with heavy malicious payloads as well as a new backdoor system.
Decoding the GRU indictment
Medium
The July 13, 2018 indictment of 12 GRU operatives provided extraordinary insight into how Fancy Bear operates. But it left several mysteries unresolved— and even injected a few new ones into the mix.
Americas
Lawyers predict extradition case for Huawei’s Meng Wanzhou could take up to a decade and set Charter precedent
The Star
@mdgmedia @Tessavikander
Lawyers specializing in extradition predict the case of embattled Huawei executive Meng Wanzhou will likely take a decade to resolve and may change the way the Canada Border Services Agency does business.
In Ortis case, the RCMP’s fight against cyber crime takes a big hit
The Globe and Mail
The arrest of Cameron Ortis, a senior official with the RCMP, for alleged breaches of Canada’s secrecy laws, has fuelled all kinds of speculation about the damage he might have caused to national security. The question has been framed in spy-speak ways around what secrets this “mole” might have revealed, and to whom?
Misc
I've spoken to some of the world's worst trolls. Here's what can help keep your kids safe online
ABC
@GingerGorman
Reddit also has a history of hosting creepy content, including child porn, hate speech and sexualised pictures of unconsenting women. Over the years it has also allowed terrible bullying and trolling on its website (I could keep going, but I've been given a word limit.)
Dear network operators, please use the existing tools to fix security
ZDNet
@stilgherrian
The internet's security and stability would be significantly improved if network operators implemented protocols that were already written into technical standards and if vendors provided better tools for fixing security.
Events
The Digital Revolution in the Pacific
ASPI ICPC
ASPI’s International Cyber Policy Centre warmly invites you to attend a panel discussion to consider how governments and businesses in the Pacific Islands are reaping the benefits and tackling the challenges stemming from increased internet and mobile connectivity.
The rise of information warfare: in-conversation with Peter W. Singer
ASPI ICPC
ASPI's International Cyber Policy Centre invites you to an in-conversation with Peter W. Singer and Danielle Cave to consider the rise of information warfare. Peter Warren Singer is strategist and senior fellow at New America. He has been named by the Smithsonian as one of the nation’s 100 leading innovators, by Defense News as one of the 100 most influential people in defense issues, by Foreign Policy to their Top 100 Global Thinkers List, and as an official “Mad Scientist” for the U.S. Army’s Training and Doctrine Command. A drinks and canapes reception will conclude the event. This event is kindly supported by Microsoft.
Jobs
Research Fellow In Cyber Security (Threats And Risks)
Charles Sturt University
High profile role to help develop Australian capability in cyber security
Focus on law, criminology and policy
Unique opportunity to engage with cyber security researchers The Role Fixed Term (up to 2 years), Full Time AU$96,178 to AU$114,117 pa (plus 17% superannuation) Wagga Wagga
Thank you for reading the Daily Cyber Digest. If you have any feedback, please let us know via email at icpc@aspi.org.au Know someone who may enjoy getting this? They can sign up here.

