Alibaba asked to shed media assets | The use of spyway to crackdown on the press | A look inside Gab, an alt-right app
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
China’s government has asked Alibaba Group to dispose of its media assets, as officials grow more concerned about the technology giant’s sway over public opinion in the country, according to people familiar with the matter. Wall Street Journal
The Committee the Protect Journalists is monitoring numerous public reports of spyware attacks that undermine press freedom – particularly those involving products sold by private companies to state agencies. Journalists say spyware has the potential to expose their sources, their movements, and other private information that could be used to censor or obstruct them, or imperil them or their sources. Spyware attacks often go hand in hand with other press freedom violations. Committee to Protect Journalists
In late February, somebody hacked Gab, an online safe space for white supremacists and other extremists. The hacker, who self-identifies as “JaXpArO and My Little Anonymous Revival Project,” exfiltrated roughly 65 gigabytes of data, including 4 million Gab accounts, 31,000 groups, and 39 million posts (over 100,000 of which were posted to private groups). The Intercept
ASPI ICPC
Push for law to stop products from forced labour being sold in NZ
stuff.co.nz
ASPI senior analyst Kelsey Munro said it was hard to understand why New Zealand would be reticent to bring in modern slavery legislation. ‘’It’s hard to be pro-slavery,’’ she told Stuff Circuit, for the documentary Deleted. “Legislation is one way of forcing transparency. It enables whole mechanisms of government to move in place to block the imports of goods that seem to be manufactured by forced labour.” Supply chain legislation introduced in other countries puts the onus on companies to examine each step and supplier in their production process and make declarations they are free of forced labour.
Australia
Online safety laws get senate committee green light
iTnews
@justinrhendry
A senate committee has given the government’s controversial online safety laws the green light, with the bill now expected to be debated in federal parliament as early as Tuesday this week.
Northern Territory’s digital infrastructure plans face big challenges
ASPI Strategist
@leadabilitygrp
The Northern Territory government has set ambitious plans for economic and social prosperity. Its catchily named ‘Terabit Territory’ initiative, which aims to position the NT to become a leader in telecommunications across Southeast Asia, is just one example.
China
Beijing Asks Alibaba to Shed Its Media Assets
Wall Street Journal
@jingyanghk
China’s government has asked Alibaba Group to dispose of its media assets, as officials grow more concerned about the technology giant’s sway over public opinion in the country, according to people familiar with the matter.
Ant issues self-disciplinary rules, CEO resigns
SupChina
@luzdingyu
Alibaba affiliate and fintech giant Ant Group wants to appease the authorities with self-regulation, but will this be enough to get the government off its back?
China has brought its repressive surveillance tools to Hong Kong
Nikkei Asia
@dmcdev
Recent events have made plain the Chinese government's intention to transform Hong Kong's digital spaces just as it has the city's offline environment and, last week, its electoral system. In January, Hong Kong authorities used the security law as grounds for blocking a website for the first time, compelling mobile providers to disrupt access to HKChronicles, which compiled information on anti-government protests and personal data on police and their supporters. recent events have made plain the Chinese government's intention to transform Hong Kong's digital spaces just as it has the city's offline environment and, last week, its electoral system.
China emerges as quantum tech leader while Biden vows to catch up
Nikkei Asia
US lags in patents related to next generation communication and cryptography.
USA
Inside Gab, the Online Safe Space for Far-Right Extremists
The Intercept
@micahflee
In late February, somebody hacked Gab, an online safe space for white supremacists and other extremists. The hacker, who self-identifies as “JaXpArO and My Little Anonymous Revival Project,” exfiltrated roughly 65 gigabytes of data, including 4 million Gab accounts, 31,000 groups, and 39 million posts (over 100,000 of which were posted to private groups).
Microsoft could reap more than $150 million in new U.S. cyber spending, upsetting some lawmakers
Reuters
@josephmenn @Bing_Chris @razhael
Microsoft stands to receive nearly a quarter of Covid relief funds destined for U.S. cybersecurity defenders, sources told Reuters, angering some lawmakers who don’t want to increase funding for a company whose software was recently at the heart of two big hacks.
How tech workers feel about China, AI and Big Tech’s tremendous power
Protocol
@birnbaum_e @issielapowsky
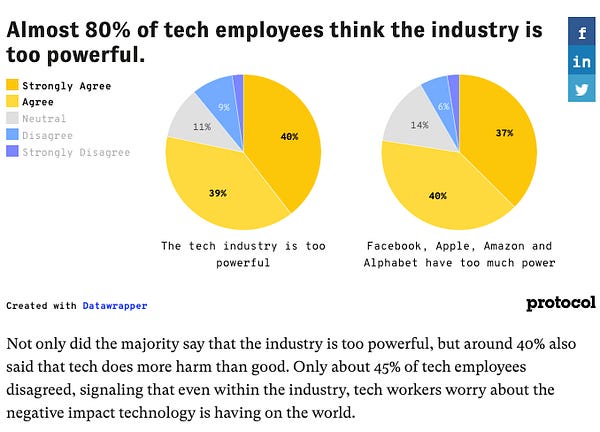
A whopping 78% of the tech employees we surveyed agreed that the tech industry is too powerful, with just 11% disagreeing.

Massive Facebook study on users’ doubt in vaccines finds a small group appears to play a big role in pushing the skepticism
Washington Post
@lizzadwoskin
Facebook is conducting a vast behind-the-scenes study of doubts expressed by U.S. users about vaccines. The internal study finds a QAnon connection and that content that doesn’t break the rules may be causing ‘substantial’ harm.
Foxconn’s U.S. Future Means Taking on Musk in Wisconsin
Bloomberg
@tculpan
Both the company and the local government need to face reality and accept that the path forward means starting again from scratch.
Bitcoin ATMs are coming to a gas station near you
Reuters
@MoiseNoise @annairrera
A new feature has appeared at smoke shops in Montana, gas stations in the Carolinas and delis in far-flung corners of New York City: a brightly-lit bitcoin ATM, where customers can buy or sell digital currency, and sometimes extract hard cash.
Incident Response Training
CISA
The Identify, Mitigate, and Recover (IMR) incident response curriculum provides a range of training offerings for beginner, intermediate, and advanced cyber professionals encompassing basic cybersecurity awareness and best practices for organizations, live red/blue team network defense demonstrations emulating real-time incident response scenarios, and hands- on cyber range training courses for incident response practitioners.
New Zealand and Pacific Islands


Europe
Why Europe’s ‘digital decade’ matters
ASPI Strategist
@vestager @JosepBorrellF
With policy targets for 2030 focusing on the four cardinal issues of skills, infrastructure and capacities, public services, and the digitalisation of business, the European Union aims to be at the forefront of today’s digital revolution.


Misc
Amazon Is Pushing Readers Down A "Rabbit Hole" Of Conspiracy Theories About The Coronavirus
Buzzfeed News
@CraigSilverman @JaneLytv
Conspiracy theorist David Icke’s lies about COVID-19 caused Facebook, Twitter, YouTube, and Spotify to ban him. But on Amazon, Icke, who believes in the existence of lizard people, is recommended reading.
Amazon Expands Effort to ‘Gamify’ Warehouse Work
The Information
@parismartineau @MarkDiStef
More and more Amazon warehouse workers around the U.S. are able to spend their shifts earning such rewards by competing in games that they control by quickly completing the repetitive tasks necessary to fulfill Amazon customer orders. The games are part of an Amazon program, called FC Games.
A Hacker Got All My Texts for $16
VICE News
@josephfcox
A gaping flaw in SMS lets hackers take over phone numbers in minutes by simply paying a company to reroute text messages.
Social media has upped its accessibility game. But deaf creators say it has a long way to go.
Wahington Post
@rachelerman
Captioning on social media can be hit or miss, making the experience sometimes alienating for deaf users.
Who Is Making Sure the A.I. Machines Aren't Racist?
The New York Times
@cademetz
When Google forced out two well-known artificial intelligence experts, a long-simmering research controversy burst into the open.
Mother 'used deepfake to frame cheerleading rivals'
BBC News
A mother allegedly used explicit deepfake photos and videos to try to get her teenage daughter's cheerleading rivals kicked off the team.
Events
ASPI Webinar: Are you ready for the new critical infrastructure law?
ASPI ICPC
With amendments to the Critical Infrastructure Act currently before parliament, impacted industry sectors are racing to get ready. ASPI's International Cyber Policy Centre is delighted to invite you to a panel discussion on 18 March at 4pm where representatives from Home Affairs, the cybersecurity sector and industry will discuss the impact of the changes and answer your questions. Register here.


Research
Spyware and Press Freedom
Committee to Protect Journalists
CPJ is monitoring numerous public reports of spyware attacks that undermine press freedom – particularly those involving products sold by private companies to state agencies. Journalists say spyware has the potential to expose their sources, their movements, and other private information that could be used to censor or obstruct them, or imperil them or their sources. Spyware attacks often go hand in hand with other press freedom violations.
Jobs
Adviser on new digitial technologies of warfare
International Red Cross and Red Crescent Movement
Acting as an in-house reference, the Adviser provides scientific and policy expertise to support the ICRC’s effects-based approach to weapons and IHL.



