Australian law enforcement's new powers to combat cyber-enabled crime | US government teams up with tech giants to tackle cyberattacks | ByteDance lays off hundreds after China’s tutoring crackdown
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
Australian Federal law enforcement agencies will be subjected to fresh oversight in return for new powers to wage offensive cyber operations against online criminal networks. The Australian
The U.S. government is enlisting the help of tech companies, including Amazon.com Inc., Microsoft Corp. and Google, to bolster the country’s critical infrastructure defenses against cyber threats after a string of high-profile attacks. The Wall Street Journal
TikTok-owner ByteDance Ltd. has laid off hundreds of employees as the social giant shuts down a significant part of its online education businesses to comply with Beijing’s new regulatory regime for the after-school tutoring industry. Yahoo
ASPI ICPC


Open-source intelligence challenges state monopolies on information
The Economist
Today’s OSINT community does not suffer from such compartmentalisation, and it has sources on the ground from which it can learn more about structures seen from the sky. In 2017 reports of “counter-extremism” and “political education” camps built by China to detain Uyghur and other Muslim minorities in Xinjiang, a western province, began circulating in local and foreign media outlets. The Australian Strategic Policy Institute (ASPI), a think-tank, gathered this evidence in a single database, supplemented it with photographs shared on Chinese social media and started looking at satellite images for structures which fitted the bill.
Experts warn 2021 census will be a magnet for cyber criminals
Government News
@judy_skatssoon
Senior Analyst with the Australian Strategic Policy Institute and author of an ASPI guide on building government services for peak demand, Tom Uren, says he’d be surprised if the census wasn’t targeted. “It’s very likely that, like last time, the census will be targeted by garden variety denial of service attacks that try to overwhelm it,” he told Government News. “I’d be positively surprised if they weren’t targeted”.
World
The chip shortage is a self-solving problem
The Economist
One firm’s crisis is another’s opportunity. A shortage of semiconductors has helped pump up the valuations of firms such as Nvidia, whose chips power everything from video-gaming to machine learning and data centres. But boom time for sellers means misery for buyers.
Australia
Federal agency cyber powers strengthened
The Australian
Federal law enforcement agencies will be subjected to fresh oversight in return for new powers to wage offensive cyber operations against online criminal networks.
The parliamentary joint committee on intelligence and security said the new powers were needed to combat serious cyber-enabled crime, including human trafficking, illicit drug enterprises, money laundering, child sexual abuse and terrorism.
Under the bill, the Australian Federal Police and the Australian Criminal Intelligence Commission will be able to access data controlled by cyber criminals, disrupt their networks and take over their online accounts, with the support of the Australian Signals Directorate.
PJCIS asks for Australia's 'hacking' Bill to gain judicial oversight and sunset clauses
ZDNet
@ashabeeeee
The parliamentary joint committee on intelligence and security said the new powers were needed to combat serious cyber-enabled crime, including human trafficking, illicit drug enterprises, money laundering, child sexual abuse and terrorism.
Australia to adopt Magnitsky style sanctions law
Reuters
Under the bill, the Australian Federal Police and the Australian Criminal Intelligence Commission will be able to access data controlled by cyber criminals, disrupt their networks and take over their online accounts, with the support of the Australian Signals Directorate.
Countries that commit 'egregious' human rights abuses to face financial sanctions, travel bans from Australia
ABC News
@stephendziedzic
Australia will follow several other Western nations and introduce a tough new sanctions regime to make it easier for the federal government to seize the assets of human rights abusers and those guilty of serious crimes.Foreign officials and corrupt business people targeted under changes to Australia’s sanctions powers
The Guardian
@danielhurstbne
The strategy includes the appointment of a chief data integration officer, and the creation of a new Data Division, as well as commitment to embed data literacy as a “cultural norm” across Defence.
US, UK, and Australia Issue Joint Cybersecurity Advisory on the Top 30 Most Exploited Vulnerabilities in 2020 and 2021
CPO Magazine
Alicia Hope
The US, UK, and Australian cybersecurity agencies and the FBI issued a joint cybersecurity advisory on the top 30 most exploited vulnerabilities in 2020 and 2021.
Defence dept launches first ever data strategy
Innovation Aus
@joseph_brookes
The Department of Defence has launched its first data strategy, promising a more disciplined and deliberate approach to the collection and use of information in decision making and policy advice.


China
ByteDance Lays Off Hundreds After China’s Tutoring Crackdown
Yahoo
@pingroma
TikTok-owner ByteDance Ltd. has laid off hundreds of employees as the social giant shuts down a significant part of its online education businesses to comply with Beijing’s new regulatory regime for the after-school tutoring industry.
An Olympic Censorship Slip
China Media Project
Joyce Chan
Users of livestreaming services topped 600 million in China in 2020, and live streamers have become a powerful force driving the growth of e-commerce in the country. But live streaming has also prompted concern from internet regulators, who see immense potential for a range of abuses in the fast-growing medium – from the marketing of low-quality and counterfeit goods and concerns over standards of basic decency, to violations of political discipline.
Delta Variant Prompts Beijing to Cancel Large August Events
The Wall Street Journal
@joshchin
Health authorities in Beijing announced the city would cancel all large-scale exhibitions and events for the remainder of August, according to state media, the latest sign of economic disruption due to the fast-spreading Delta variant.
Chinese Government Invested in the Same Tech Companies It’s Now Attacking
The Information
@beijingscribe @JuroOsawa
The United States Cybersecurity and Infrastructure Security Agency (CISA), the Australian Cyber Security Centre (ACSC), the UK’s National Cyber Security Centre (NCSC), and the U.S. Federal Bureau of Investigation (FBI) co-authored the joint cybersecurity advisory AA21-209A.
USA
U.S. Taps Amazon, Google, Microsoft, Others to Help Fight Ransomware, Cyber Threats
The Wall Street Journal
@bobmcmillan
The U.S. government is enlisting the help of tech companies, including Amazon.com Inc., Microsoft Corp. and Google, to bolster the country’s critical infrastructure defenses against cyber threats after a string of high-profile attacks.
US government teams up with tech giants to tackle the next big cyberattack
Teach Radar
@TECHTOPOLIS
The initiative, called the Joint Cyber Defense Collaborative (JCDC), will see the Cybersecurity and Infrastructure Security Agency (CISA) work alongside leading technology providers, cybersecurity firms and telecoms to create and execute new cyber defense operations plans.
A US official explains why the White House decided not to ban ransomware payments
CyberScoop
@TonyaJoRiley
The Biden administration backed away from the idea of banning ransomware payments after meetings with the private sector and cybersecurity experts, a top cybersecurity official said Wednesday. “Initially, I thought that was a good approach,” Anne Neuberger, deputy national security advisor for cyber and emerging technology, said at an Aspen Security Forum event. “We know that ransom payments are driving this ecosystem.” Experts, including former government officials serving on a non-profit ransomware task force, helped shift that view, following high-profile hacks against Colonial Pipeline, the food production company JBS and Kaseya, a Florida-based IT firm. Payments from the Colonial Pipeline and JBS attacks totaled more than $15 million, a number that likely represents a fraction of the funds sent to extortionists
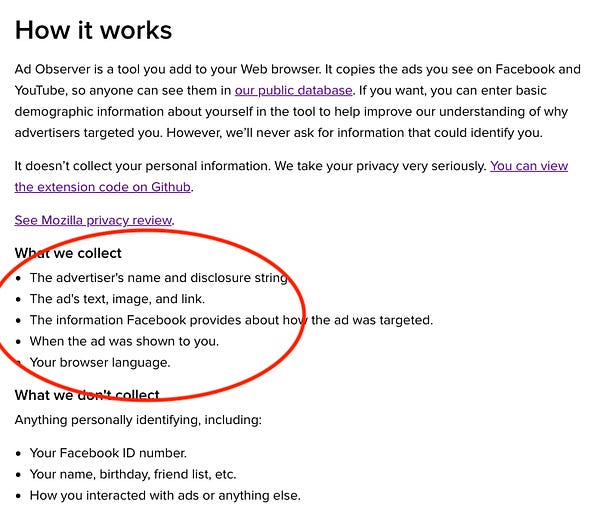
Facebook is an ad tech company. That’s how we should regulate it.
Tech Policy Press
@MarechalPhD
Those of us who are concerned about democracy, civil and human rights, and corporate accountability in the tech sector should take this as evidence that the NYU Cybersecurity for Democracy group is on the right track. We need more scrutiny of the online advertising sector. In fact, we need to reframe the “social media governance” conversation as one about regulating ad tech. Facebook, Twitter, YouTube, TikTok and the rest exist for one purpose: to generate ad revenue. Everything else is a means for producing ad inventory.
Report: Apple to announce client-side photo hashing system to detect child abuse images in users’ photos libraries
9 To 5 Mac
@bzamayo
Apple is reportedly set to announce new photo identification features that will use hashing algorithms to match the content of photos in users’ photo libraries with known child abuse materials, such as child pornography.
Apple plans to scan US iPhones for child abuse imagery
The Financial Times
Security researchers raise alarm over potential surveillance of personal devices.
Apple Walks a Privacy Tightrope to Spot Child Abuse in iCloud
WIRED
@a_greenberg
For years, tech companies have struggled between two impulses: the need to encrypt users' data to protect their privacy and the need to detect the worst sorts of abuse on their platforms. Now Apple is debuting a new cryptographic system that seeks to thread that needle, detecting child abuse imagery stored on iCloud without—in theory–introducing new forms of privacy invasion. In doing so, it's also driven a wedge between privacy and cryptography experts who see its work as an innovative new solution and those who see it as a dangerous capitulation to government surveillance.
Scammer Service Will Ban Anyone From Instagram for $60
VICE News
@josephfcox
Scammers are abusing Instagram's protections against suicide, self-harm, and impersonation to purposefully target and ban Instagram accounts at will, with some people even advertising professionalized ban-as-a-service offerings so anyone can harass or censor others, according to screenshots, interviews, and other material reviewed by Motherboard.
From Comcast to crypto: Here’s who wins and loses in the Senate infrastructure bill
Protocol
@issielapowsky
The $1 trillion bill includes $550 billion in new spending, of which tens of billions of dollars will go toward broadband expansion, low-income internet subsidies, electric vehicle investments, charging stations, cybersecurity and more. The outpouring of federal funding gives anyone from telecom giants to device manufacturers a lot to like.
There's been a rise in stalkerware. And the tech abuse problem goes beyond smartphones
ZDNet
@SecurityCharlie
No matter how stalkerware is marketed, it is part of a wider problem: the use of technology in coercive control.
North-East Asia
TSMC's latest 5nm production is at max capacity. Here's why that's bad news
Tech Radar
@ThisDotJohn
Fighting for attention from TSMC is going to be an increasingly expensive proposition until fabrication capacity ramps up across the industry, something that can't happen until new plants come online and that takes years. Needless to say, this isn't a problem that looks like it'll be solved any time soon.
South-East Asia
Top spreader of COVID-19 disinformation has an office in Manila
Rappler
@gelogonzales86
Jen Easterly, head of the Cybersecurity and Infrastructure Security Agency, said the aim is to improve information sharing between government and the private sector.
Europe
Swiss Ph.D student’s dismissal spotlights China’s influence
Neue Zürcher Zeitung
@larissa_rhyn @KBuechenb Christoph Fischer
A Swiss Ph.D. student tweeted critically about China. Afterward, his professor at the University of St. Gallen wanted nothing more to do with him, worried that her own ability to get a visa would be at risk.
Russia

The Americas
Why the internet in Cuba has become a US political hot potato
The Guardian
Ed Augustin Daniel Montero
After Havana shut down online access for 72 hours, the battle is on to keep the country connected.
Misc
LockBit ransomware recruiting insiders to breach corporate networks
Bleeping Computer
@LawrenceAbrams
The LockBit 2.0 ransomware gang is actively recruiting corporate insiders to help them breach and encrypt networks. In return, the insider is promised million-dollar payouts.
Online Abuse - AI Research Study
Professional Footballers' Association
Despite social media platforms pledging better moderation, Signify's machine-learning AI systems found more than three-quarters of the 359 accounts sending explicitly racist abuse to players were still on the platform. As of July 2021, the vast majority of these accounts remain unsanctioned.
Location-Data Broker X-Mode to Be Bought by Digital Envoy
The Wall Street Journal
@ByronTau @patiencehaggin
The location-data broker X-Mode Social Inc., which was kicked off the Apple and Google platforms last year over its national-security work with the U.S. government, is being acquired, the company told The Wall Street Journal.


If machines can be inventors, could AI soon monopolise technology?
The Conversation
@LAWS12068_AJG
In patent law, designed to protect the intellectual property of inventors, officials are used to thinking of inventors as humans, taking an “inventive step” – a new way of doing something — not obvious to a person skilled in the same art. But last week — in a judicial world first — Australia’s Federal Court ruled an artificial intelligence (AI) system can be named as an inventor.

Jobs
ICPC Deputy Director – 12 month parental leave cover
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) is currently recruiting for a one-year parental leave cover for its Deputy Director position. This is an exceptional opportunity for a talented and experienced individual to contribute to the work of Australia's leading think-tank on cyber, information, technology and other national security issues in a unique leadership role.
ICPC Senior Analyst & Program Manager
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) potentially has an outstanding opportunity for a proactive, efficient and talented senior analyst & program manager to join its centre. We are looking for a senior individual with a minimum of 10-15 years of demonstrated relevant work experience who possesses excellent project management, stakeholder engagement and staff management skills. They must also possess strong knowledge - either as a generalist or a specialist - of some of the topics ICPC works across, and feel comfortable engaging with politicians, senior policymakers, business representatives and preferably also the media.
ICPC Senior Analyst or Analyst - China
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has a unique opportunity for exceptional and experienced China-focused senior analysts or analysts to join its centre. This role will focus on original research and analysis centred around the (growing) range of topics which our ICPC China team work on. Our China team produces some of the most impactful and well-read policy-relevant research in the world, with our experts often being called upon by politicians, governments, corporates and civil society actors to provide briefings and advice. Analysts usually have at least 5 years, often 7-10 years’ of work experience. Senior analysts usually have a minimum of 15 years relevant work experience and, in addition to research, they take on a leadership role in the centre and tend to be involved in staff and project management, fundraising and stakeholder engagement.
Christchurch Call Advisory Network Coordinator
Christchurch Call
This exciting inaugural position for the Network will help us ensure that civil society has the tools needed to actively participate in and influence the work of the Christchurch Call. This position will work with the Network to build organization structures from the ground up and engage with current Network members. Someone interested in technology policy and/or multistakeholder governance, and is excited about building something new and facilitating cutting-edge discussions will excel in this role.










