China uses DNA to map faces with help from the West | China’s military might has now become a top issue for NATO | Labor seeks to amend encryption legislation


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
Growing numbers of scientists and human rights activists say the Chinese government is exploiting the openness of the international scientific community to harness research into the human genome for questionable purposes. Already, China is exploring using facial recognition technology to sort people by ethnicity. It is also researching how to use DNA to tell if a person is a Uighur. The New York Times
NATO Secretary General Jens Stoltenberg told delegates at the “NATO Engages” event in London, a precursor to the “Leaders Meeting” that starts Tuesday evening, that for the first time China was on NATO’s agenda. CNBC
Labor will seek to force the government to change controversial encryption-piercing legislation, introducing amendments to the Senate in line with the findings of a bipartisan parliamentary committee. The Sydney Morning Herald
ASPI ICPC
Beyond today – is TikTok being censored?
BBC
TikTok says it didn’t censor her content, but as Karishma Vaswani tells us, the company is walking a difficult line trying to keep people happy in both China and the rest of the world. We also hear from Vicky Xu, a researcher who uses TikTok to find out more about Xinjiang.

Killer robo-bees show how the sting of disinformation can spread
The Strategist
@elisethoma5
Investigations of influence operations and information warfare methodologies tend to focus heavily on the use of inauthentic social media activity and websites purpose built to propagate misinformation, disinformation and misleading narratives. There are, however, a range of other methodologies that bad actors can exploit. One way in which obviously false content can be spread quickly, widely and easily across ‘junk news’ sites is through a syndicated press release.
World
TikTok curbed reach for people with disabilities
NetzPolitik
Leaked documents reveal how TikTok hid videos of people with disabilities. Queer and fat users were also pushed out of view. The Chinese company says the rules were meant to protect vulnerable users.
TikTok sent US user data to China, lawsuit claims
BBC
Video-sharing app TikTok has been hit with a class action lawsuit in the US that claims it transferred "vast quantities" of user data to China.
Tinder Lets Known Sex Offenders Use The App. It’s Not The Only One.
Buzzfeed
@HillBillFlynn @KeithJCousins @ElizabethPicc
Match Group, which owns most major online dating services, screens for sexual predators on Match — but not on Tinder, OkCupid, or Plenty of Fish. A spokesperson said, “There are definitely registered sex offenders on our free products.”
China’s military might has now become a top issue for NATO
CNBC
@HOLLYELLYATT @DAVYREID73
NATO Secretary General Jens Stoltenberg told delegates at the “NATO Engages” event in London, a precursor to the “Leaders Meeting” that starts Tuesday evening, that for the first time China was on NATO’s agenda. “We have to address the fact that China is coming closer to us, investing heavily in infrastructure. We see them in Africa, we see them in the Arctic, we see them in cyber space and China now has the second-largest defense budget in the world,” he said.
Australia
Government broke their promise': Labor seeks to amend encryption legislation
The Sydney Morning Herald
@fergushunter
Labor will seek to force the government to change controversial encryption-piercing legislation, introducing amendments to the Senate in line with the findings of a bipartisan parliamentary committee. The government rushed the Assistance and Access Bill through Parliament late last year with Labor's support. The opposition has since accused the government of breaking a promise to put in place a series of amendments to the legislation.


China
China Uses DNA to Map Faces, With Help From the West
The New York Times
@suilee @paulmozur
Growing numbers of scientists and human rights activists say the Chinese government is exploiting the openness of the international scientific community to harness research into the human genome for questionable purposes. Already, China is exploring using facial recognition technology to sort people by ethnicity. It is also researching how to use DNA to tell if a person is a Uighur. Research on the genetics behind the faces of Tumxuk’s men could help bridge the two.
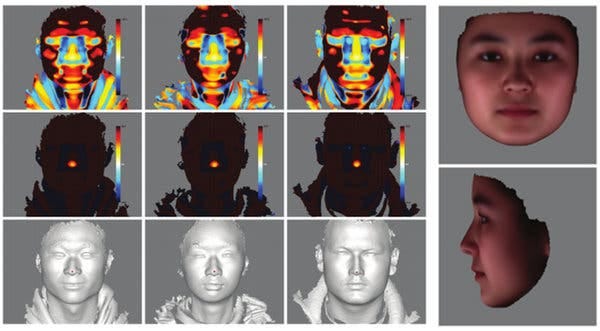
Images from a study in 2013 on 3-D human facial images using data of Uighurs. Source: BMC Bioinformatics
Huawei founder Ren Zhengfei plans to relocate research centre to Canada from U.S.
The Globe and Mail
@nvanderklippe
Huawei plans to shift research to Canada from the United States and manufacture some mobile network equipment outside China, its founder Ren Zhengfei says, as the Chinese tech giant seeks to combat an increasingly hostile White House.
US
Facebook Gives Workers a Chatbot to Appease That Prying Uncle
The New York Times
@sheeraf @MikeIsaac
The “Liam Bot” teaches employees what to say if friends or family ask difficult questions about the company over the holidays.
Southeast Asia
House probe sought on China co-ownership of NGCP
CNN Philippines
It was former Senior Associate Justice Antonio Carpio who earlier raised that China may shut down the country's power grid by "injecting a malware or software" in the system once they get to maintain it.
South Asia
Cyber Security Strategy 2020: India mulls umbrella body like UK’s NCSC to counter cyber threats
ETPrime
Expected early next year, the Cyber Security Strategy 2020 will attempt to fill the security gaps and improve coordination among a dozen different agencies. Sources say this will be achieved by setting up a unified command similar to the UK’s National Cyber Security Centre which advises and supports public and private sectors on defending against cyber threats.
U.S. Tech Giants Bet Big on India. Now It’s Changing the Rules.
The Wall Street Journal
@Newley
New barriers make world’s biggest untapped digital market a slog for Walmart, Facebook; taking cues from China’s protectionism.
UK
With Brits Used to Surveillance, More Companies Try Tracking Faces
The Wall Street Journal
@Parmy
The U.K. has more surveillance cameras per capita than any other country in the West. But it is private companies’ cameras, not the government’s, that are starting to worry activists and regulators.
Europe
Dutch cabinet comes with additional requirements to keep Huawei out of construction 5G
NOS
With the roll-out of the new mobile network 5G, the cabinet will come up with additional requirements to keep the Chinese Huawei out. Huawei is not specifically mentioned in the requirements, but in practice it means that no business may be done with the Chinese company for the construction of the most sensitive parts of the 5G network.
Misc
FBI Asked Sony for Data on User Who Allegedly Used PlayStation Network to Sell Cocaine
Vice
@josephfcox
The search warrant application even asks what games the suspect played and their progress.
Industrial cyber attacks: a humanitarian crisis in the making
ICRC
@cnoanalysis
Industrial control systems manage almost every aspect of daily life, from water supply to electricity or industrial production. The number of cyber attacks on these systems is increasing, as is the number of adversaries now investing in such attacks. For societies across the globe, the situation has potentially dire effects: cities could be cut off from water or electricity and economies could be severely compromised. Decisive actions are needed to increase system defensibility and to manage the behaviors of attackers threatening them.
This new Android malware comes disguised as a chat app
ZDNet
@dannyjpalmer
CallerSpy can monitor calls, messages, take screenshots and records its surroundings, say researchers - who warn that it could be the early stages of a targeted cyber-espionage campaign.
Research
The Application of International Law to State Cyberattacks: Sovereignty and Non-Intervention
Chatham House
@HarrietMoyniha9
Hostile cyber operations by one state against another state are increasingly common. This paper analyzes the application of the sovereignty and non-intervention principles in relation to states’ cyber operations in another state below the threshold of the use of force.



