Chinese Goverment employees in Apple's data centre | A new UN report on autonomous weapons | The US' legions of cyber-warriors
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
At a data center in Guiyang, which Apple hoped would be completed by next month, and another in the Inner Mongolia region, Apple has largely ceded control to the Chinese government. Chinese state employees physically manage the computers. Apple abandoned the encryption technology it used elsewhere after China would not allow it. And the digital keys that unlock information on those computers are stored in the data centers they’re meant to secure. The New York Times
Autonomous machines can only be autonomous because they collect data about their environment as they move through it, and then act on that data. In training environments, the data that autonomous systems collect is relevant, complete, accurate, and high quality. But, according to a newly released UN report, “conflict environments are harsh, dynamic and adversarial, and there will always be more variability in the real-world data of the battlefield than the limited sample of data on which autonomous systems are built and verified.” Popular Science
The largest undercover force the world has ever known is the one created by the Pentagon over the past decade. These are the cutting-edge cyber fighters and intelligence collectors who assume false personas online, employing "nonattribution" and "misattribution" techniques to hide the who and the where of their online presence while they search for high-value targets and collect what is called "publicly accessible information"—or even engage in campaigns to influence and manipulate social media. Hundreds work in and for the NSA, but over the past five years, every military intelligence and special operations unit has developed some kind of "web" operations cell that both collects intelligence and tends to the operational security of its very activities. Newsweek
ASPI ICPC


The case for a ‘disinformation CERN’
The Strategist
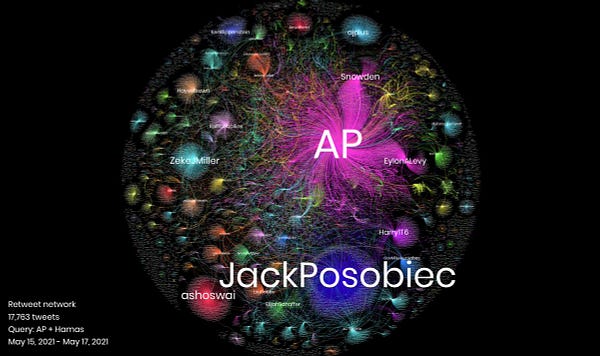
Speaking in a panel discussion how democracies can collaborate on disinformation at ASPI’s grey zone and disinformation masterclass last week, Wanless went on to say that what we really need is ‘a disinformation CERN’—in reference to the international particle physics research outfit, where countries pool their resources to operate the Hadron particle accelerator, study results and share findings. The scale and reach of the disinformation problem is so huge that only research cooperation of this kind can address the global shared threat to information systems. Our democratic societies are doomed to decline if we don’t put forward major effects to arrest the effects of disinformation, said Wanless.
Read Danielle Cave & Jake Wallis’s essay for the Indian think-tank ORF, Defending Democracies from Disinformation and Cyber-Enabled Foreign Interference in the COVID-19 Era






World
Autonomous war machines could make costly mistakes on future battlefields - An exclusive first look at a UN Institute Report on the risks of autonomous weapons.
Popular Science
Autonomous machines can only be autonomous because they collect data about their environment as they move through it, and then act on that data. In training environments, the data that autonomous systems collect is relevant, complete, accurate, and high quality. But, the report notes, “conflict environments are harsh, dynamic and adversarial, and there will always be more variability in the real-world data of the battlefield than the limited sample of data on which autonomous systems are built and verified.”
Australia
SpaceX’s reusable rocket technology will have implications for Australia
The Strategist
@Dr_M_Davis
That may open up new opportunities for the Australian Defence Force’s use of sovereign launch capabilities. It’s possible that 10 years from now the ADF Space Command could manage sovereign-controlled satellites and be able to rely on sovereign launch capability provided by Australian commercial launch providers.


China
Censorship, Surveillance and Profits: A Hard Bargain for Apple in China
The New York Times
@jacknicas @zhonggg @daiwaka
At a data center in Guiyang, which Apple hoped would be completed by next month, and another in the Inner Mongolia region, Apple has largely ceded control to the Chinese government. Chinese state employees physically manage the computers. Apple abandoned the encryption technology it used elsewhere after China would not allow it. And the digital keys that unlock information on those computers are stored in the data centers they’re meant to secure.
USA
Inside the military's secret army, the largest undercover force ever
Newsweek
@warkin
The largest undercover force the world has ever known is the one created by the Pentagon over the past decade. These are the cutting-edge cyber fighters and intelligence collectors who assume false personas online, employing "nonattribution" and "misattribution" techniques to hide the who and the where of their online presence while they search for high-value targets and collect what is called "publicly accessible information"—or even engage in campaigns to influence and manipulate social media. Hundreds work in and for the NSA, but over the past five years, every military intelligence and special operations unit has developed some kind of "web" operations cell that both collects intelligence and tends to the operational security of its very activities.
Pentagon Plans to Monitor Social Media of Military Personnel for Extremist Content
The Intercept
@kenklippenstein
The military has previously balked at surveilling service members for extremist political views due to First Amendment protections.
Social app Parler is cracking down on hate speech — but only on iPhones
Washington Post
When social media network Parler came back to life on Apple’s App Store Monday, it was designed to be a less offensive version than what users are able to see elsewhere. Posts that are labeled “hate” by Parler’s new artificial intelligence moderation system won’t be visible on iPhones or iPads. There’s a different standard for people who look at Parler on other smartphones or on the Web: They will be able to see posts marked as “hate,” which includes racial slurs, by clicking through to see them.
Biden Proposes Billions for Cybersecurity After Wave of Attacks
Bloomberg
@jeneps @KartikayM
President Joe Biden’s infrastructure proposal includes billions of dollars tied to improving cybersecurity, an area of intensified interest after the ransomware attack on the Colonial Pipeline Co. sent U.S. gasoline prices soaring last week. But the exact amount that will be spent on improving cyber defenses remains to be seen.
North-East Asia
Taiwan Aims to Keep Chip Production Humming as Covid Spreads
Bloomberg
@debbywuintaipei
Taiwan’s government pledged to try to keep the world supplied with chips even as Covid-19 cases escalate, while anticipating a limited impact from its worst outbreak so far.
Europe


Middle East

Misc
You should be worried about how much info WhatsApp shares with Facebook
The Guardian
@burcuno
Facebook is pushing a mysterious and aggressive ‘privacy update’ on WhatsApp users.
Facebook wants ‘other companies’ to use the Oversight Board, too
Engadget
@karissabe
Facebook created the Oversight Board to help solve its most difficult content moderation decisions. But though the body is often referred to as “Facebook’s Supreme Court,” Facebook executives have suggested that some of their peers could one day benefit from the board’s services, too.
Events
Regulation, realpolitik and ransomware: Examining Australia's cyber policy landscape
CyberCX - Cyber Dialogue
CyberCX is pleased to be hosting the next instalment of our Cyber Dialogue webcast series, featuring Shadow Assistant Minister for Cyber Security Tim Watts MP in conversation with Alastair MacGibbon.
The Next Phase in Cyber Warfare
The Red-line Podcast
With each major technological leap forward in warfare the rules of war also change. Today's challenge is Cyber Warfare, which has completely thrown out the conventional concept of the first strike. With tens of thousands of attacks occurring each day from all of the major players, we look at the landscape of cyber warfare and ask whether any nation can truly be prepared to defend itself.

Research
The Coming AI Hackers
Belfer Center for Science and International Affairs
@schneierblog
One, AI systems will be used to hack us. And two, AI systems will themselves become hackers: finding vulnerabilities in all sorts of social, economic, and political systems, and then exploiting them at an unprecedented speed, scale, and scope. It’s not just a difference in degree; it’s a difference in kind. We risk a future of AI systems hacking other AI systems, with humans being little more than collateral damage.
Jobs
International Cyber Policy Centre – Strategic engagement, program & research coordinator
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has an outstanding early career role for a talented and proactive individual to support senior centre staff on strategic engagement, program and research coordination.





