Close ties allow Russian propaganda to spread swiftly through China | Cyber war talks heat up at UN with Russia at Table | A Facebook bug led to increased views of Harmful content over six months
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
Close ties between Russian and Chinese state media along with strict government control of information have allowed Russian propaganda to spread swiftly throughout China, “nazifying” Ukraine in the eyes of some Chinese citizens and fostering pro-Russian sentiment, a new report has claimed. The Guardian
'Russia has made a mockery of its pretension to lead on cyberissues at the United Nations,' Michele Markoff, U.S. lead on cyber matters at the meeting. She said Russia had attacked Ukrainian banks, government websites and private sector entities as part of its invasion in a way 'designed to affect the civilian population. 'Bloomberg
A group of Facebook engineers identified a “massive ranking failure” that exposed as much as half of all News Feed views to “integrity risks” over the past six months, according to an internal report on the incident. The Verge
ICPC

The cyber–maritime security nexus and priorities for UK–Australia–ASEAN cooperation
The Strategist
Huong Le Thu and Bart Hogeveen
The UK government’s Integrated review of security, defence, development and foreign policy presents the Indo-Pacific as a region of increasing geopolitical and economic importance over the next decade and suggests that competition will play out in ‘regional militarisation, maritime tensions and contest over the rules and norms linked to trade and technology’.
What’s happened to Russia’s much-vaunted battlefield AI?
The Strategist
Huon Curtis
The Russian invasion of Ukraine and the poorer than expected performance of the Russian army have prompted fierce debate among military commentators on why Russia’s much-vaunted military reforms of the past decade—particularly the integration of artificial intelligence technologies that were supposed to enhance Russia’s joint operations capability—seem to have been unsuccessful.


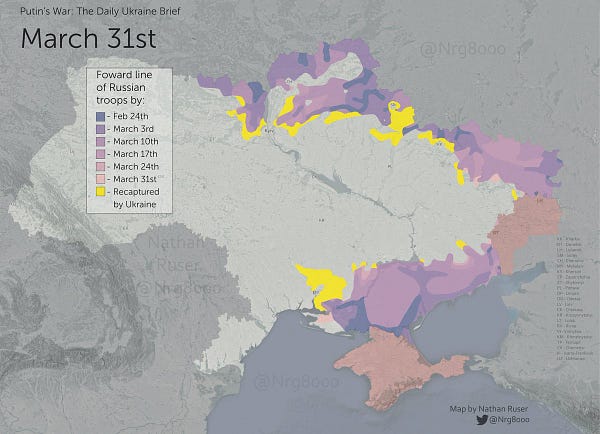
Ukraine - Russia
Cyber war talks heat up at UN with Russia at table
Bloomberg
Katrina Manson
“Russia has made a mockery of its pretension to lead on cyberissues at the United Nations,” Michele Markoff, U.S. lead on cyber matters at the meeting. She said Russia had attacked Ukrainian banks, government websites and private sector entities as part of its invasion in a way “designed to affect the civilian population.”
I can fight with a keyboard': How one Ukrainian IT specialist exposed a notorious Russian ransomware gang
CNN
Sean Lyngaas
Four days into Russia's invasion, the researcher began publishing the biggest leak ever of files and data from Conti, a syndicate of Russian and Eastern Europe cybercriminals wanted by the FBI for conducting attacks on hundreds of US organizations and causing millions of dollars in losses. The thousands of internal documents and communications include evidence that appears to suggest Conti operatives have contacts within the Russian government, including the FSB intelligence service. That supports a longstanding US allegation that Moscow has colluded with cybercriminals for strategic advantage.
A nation of spy-catchers: fear of saboteurs has Ukrainians on edge
The New York Times
Valerie Hopkins
Ukrainians have been shaken by reports of “dyversanti” — saboteurs and diversionary groups working for Russia who mix into the civilian population, sow confusion and mistrust, and possibly even alert the enemy to potential targets. Civilians who were already living in fear are seeing spies everywhere.
The last days of Mariupol’s internet
Forbes
Engineers who kept Ukraine’s port city online have gone missing or died in the carnage inflicted by Russia’s siege. Hope remains that Ukrainian cities knocked off the internet map will come back online fast once the shelling ends.
Some Russian oligarchs are using U.K. data privacy law to sue
The Washington Post
Reed Albergotti
Russian oligarchs and other powerful individuals are turning to an unusual method to protect their online images: data privacy laws. Those laws, which were intended to prevent ads from tracking consumers too closely around the Internet, are now being used in the United Kingdom to sue anyone holding undesirable information on their devices. That could include a journalist‘s notes from an interview typed into a computer or a private investigator’s compromising photos stored on a phone.
Australia
Leading role in the space race from the Adelaide CBD
The Australian
James Dunn
It seems fitting that the thriving Australian space industry is home-ported in Adelaide; after all, South Australia kicked off Australia’s involvement with space, with the establishment of the Woomera Rocket Testing range in the state’s north, in 1947.
China
Close ties allow Russian propaganda to spread swiftly through China, report claims
The Guardian
Helen Davidson
Close ties between Russian and Chinese state media along with strict government control of information have allowed Russian propaganda to spread swiftly throughout China, “nazifying” Ukraine in the eyes of some Chinese citizens and fostering pro-Russian sentiment, a new report has claimed.
Huawei faces dilemma over Russia links that risk further US sanctions
Financial Times
Ryan McMorrow, Anna Gross, Polina Ivanova and Kathrin Hille
The last time western sanctions hit Russia after it annexed Crimea, President Vladimir Putin turned to Huawei to rebuild and upgrade the territory’s communication infrastructure. Now the controversial Chinese technology company is positioned to aid the Putin regime on a much larger scale, despite the threat of Washington hitting it with more sanctions.
China tells big tech to reveal some customers' income
The Register
Laura Dobberstein
China's massive live-streaming industry is the next target of China's tech regulation blitz, with three governmental agencies announcing a requirement for operators to register in an attempt to eliminate tax evasion.
USA
FBI warns of phishing attacks targeting US election officials
Security Week
Ionut Arghire
The Federal Bureau of Investigation (FBI) this week warned US election officials of potential invoice-themed phishing attacks meant to steal their login credentials.
The U.S. imposes sanctions on Russian technology companies and evasion networks.
The New York Times
Alan Rappeport
The Treasury Department is also imposing sanctions on several technology companies that produce computer hardware, software and microelectronics that are used by Russia’s defense sector. Among them is Joint Stock Company Mikron, Russia’s largest chip-maker.
Viasat cyberattack blamed on Russian wiper malware
TechCrunch
Carly Page
The recent cyberattack on U.S. satellite communications provider Viasat, an incident that triggered satellite service outages across central and eastern Europe, was likely the result of destructive wiper malware, according to newly published security research.
VIASAT incident: from speculation to technical details.
Reversemode
Ruben Santamarta
34 days after the incident, yesterday Viasat published a statement providing some technical details about the attack that affected tens of thousands of its SATCOM terminals. Also yesterday, I eventually had access to two Surfbeam2 modems: one was targeted during the attack and the other was in a working condition.
North Asia
North Korean ICBM launch may have been fake. It’s still important.
The New York Times
Choe Sang-Hun
South Korea says Kim Jong-un disguised an older missile as a new one to exaggerate his country’s weapons achievements when he badly needs political leverage.
NZ & Pacific Islands
Digital transformation is accelerating SIDS' development
United Nations Development Programme
SIDS are a 'special case in development' (to use the language of the SAMOA Pathway) due to their innate potential, and proven ambition, in driving digital transformation within and beyond their shorelines. They are leading the implementation of digital in the context of the Pathway, the Sustainable Development Goals, the Paris Agreement, and in pursuit of national and other global priorities. Digital is already a key driver of SIDS development, foundational to tackling climate change and other challenges - but it's not just about surviving.
UK
Director GCHQ's speech on global security amid war in Ukraine
GCHQ
Jeremy Fleming
We have to find new ways to collaborate and cooperate with partners. For those of us in National Security, that’s about ensuring the health of existing relationships. It’s about securing our alliances, like the Five Eyes, NATO and in this region, ASEAN. And it’s about working with businesses in new and truly collaborative ways. And to do this we need to make sure that our counteroffer – to states who haven’t yet decided which way they should jump – is persuasive and coherent. Too often it’s not.
Africa
Insecurity: Police acquire technological devices to combat crimes
Premium Times
Nasir Ayitogo
The Nigerian Police Force has acquired additional high-powered Unmanned Aerial Vehicles (UAVs), popular known as drones, to improve surveillance operations across the country.
Big Tech
A Facebook bug led to increased views of harmful content over six months
The Verge
Kevin Collier
A group of Facebook engineers identified a “massive ranking failure” that exposed as much as half of all News Feed views to “integrity risks” over the past six months, according to an internal report on the incident obtained by The Verge.
Crypto-Bridge hacks reach over $1 billion in little over a year
Bloomberg
Olga Kharif
The $600 million hack this month of a crypto “bridge” supporting Axie Infinity’s play-to-earn video game highlights the increasingly problematic nature of the arcane software used within the world of digital assets, blockchains and the metaverse.
Ben McKenzie would like a word with the Crypto Bros
The New York Times
David Yaffe-Bellany
The crypto market seemed tailor-made for fraud, Mr. McKenzie said. He was convinced the skyrocketing valuations of popular coins were fueled by reckless speculation, rather than any practical application of the technology. “It doesn’t do what currencies do,” he said. “It’s not a reliable store of value, unit of account or medium of exchange.”
Am I being tracked? Anti-stalking tech from Apple, Tile falls short.
The Washington Post
Geoffrey A. Fowler
A year later, Apple along with similar tracker-tag makers Tile and Samsung have introduced a host of product updates to deter stalking and help victims learn if they’re being followed. But what I discovered from my stroller test was a patchwork of apps that work better for engineers than for domestic abuse survivors.
Twitter user sentenced to 150 hours of community service in UK for posting ‘offensive’ tweet
The Verge
James Vincent
A Twitter user from the UK named Joseph Kelly has been sentenced to 150 hours of community service for posting a “grossly offensive” tweet about Captain Sir Tom Moore, a British Army officer who raised money for the NHS during the pandemic.
Google unrolls search features to tackle misinformation
The Register
Brandon Vigliarolo
Further embracing its unspoken role as arbiter of truth, Google has unrolled some new search result features to help users "sort out what information is credible and what isn't." In particular, the search giant is introducing two new attributes: Information literacy tips for breaking topics, and a new Highly Cited label for news stories that have been widely used as sources for other news stories.
Events and Podcasts
Jobs
The Sydney Dialogue - Director
ASPI ICPC
The Australian Strategic Policy Institute (ASPI) is currently recruiting for a Director to lead the second iteration of ASPI’s Sydney Dialogue - the world’s premier summit on emerging, critical and cyber technologies.
The Sydney Dialogue - Senior Events Coordinator
ASPI ICPC
The Australian Strategic Policy Institute (ASPI) is currently recruiting for an experienced events professional to coordinate the planning and logistics of the second iteration of ASPI’s Sydney Dialogue - the world’s premier summit on emerging, critical and cyber technologies.
ICPC Senior Analyst or Analyst - China
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has a unique opportunity for exceptional and experienced China-focused senior analysts or analysts to join its centre. This role will focus on original research and analysis centred around the (growing) range of topics which our ICPC China team work on. Our China team produces some of the most impactful and well-read policy-relevant research in the world, with our experts often being called upon by politicians, governments, corporates and civil society actors to provide briefings and advice.
Important disclaimer: This digest is a daily collation of material designed to provide authoritative information and commentary in relation to the subject matters covered. The views expressed in this material are those of the authors only. To provide feedback please contact: icpc@aspi.org.au