Cyberattack forces shutdown of a top U.S. pipeline | China to punish data exports to overseas courts and law enforcement | UK spies warn local authorities over ‘smart city’ tech risks
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
One of the nation’s largest pipelines, which carries refined gasoline and jet fuel from Texas up the East Coast to New York, was forced to shut down after being hit by ransomware in a vivid demonstration of the vulnerability of energy infrastructure to cyberattacks. The New York Times
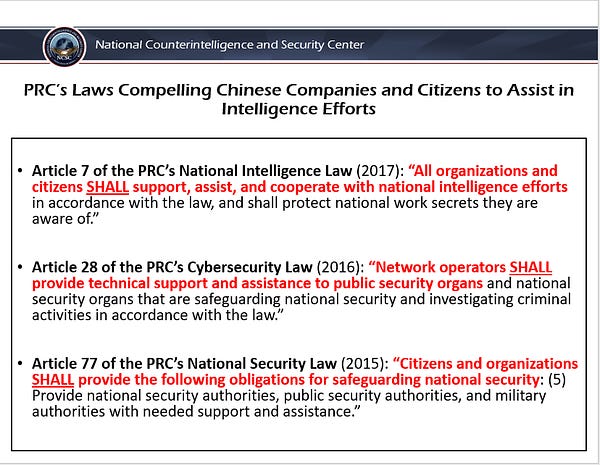
A clause has been added to China’s draft data security law that will punish Chinese companies for handing over domestically stored data to foreign police, courts and investigators without Beijing’s consent, a move that will make it harder for overseas law enforcement agencies to get data out of China. South China Morning Post
Smart city technology designed to streamline public services could prove an “attractive target” for hostile states seeking to disrupt Britain’s infrastructure or steal sensitive data, UK spies have warned. The intervention by the National Cyber Security Centre, a branch of GCHQ, reflects growing fears in the intelligence community that local authorities may inadvertently enter risky contracts which could expose them to cyber attack or compromise individuals’ privacy. A deal that was aborted at the last minute involved Bournemouth council in Dorset, which was preparing a contract with the Chinese ecommerce company Alibaba to provide “smart place” services. Financial Times
World
Defying Chinese surveillance, young Uyghurs abroad speak up online
Reuters
Lin Taylor
Several young Uyghurs living abroad told the Thomson Reuters Foundation they have received threats over the phone and in emails, are relentlessly harassed on social media, and have also been physically spied on.
Australia
Israeli company denies 'security rumours' as Defence removes multi-billion-dollar technology and quarantines Army IT systems
ABC News
@AndrewBGreene
Defence has begun stripping Israeli-developed technology from Army equipment because of fears it could be used to harvest sensitive data from military hardware and systems.

Australians need clarity on war or peace
Australian Financial Review
@Ben_G_Scott
China has proved particularly adept at competing in this grey zone: from economic coercion to aggressive cyber activity to establishing facts on the water in the South China Sea. Australia has played catch-up as we have come to realise the national security implications of domains previously thought to be purely economic, commercial or technological.
He knew my every movement': How technology is making domestic violence so much worse
ABC News
@MaryGearin
Technology-facilitated abuse is overwhelmingly gendered — 96 per cent of perpetrators are male and 93 per cent of victims are female. A recent national survey by women's services network WESNET found the found almost all women experiencing family violence suffered from technology abuse. It's a term that covers everything from abusive texts and social media posts, to tracking of smartphones, to covert monitoring of a victim's movements. And it's getting worse.
Queensland needs tougher laws on data breaches and cyber hacking, says privacy chief
ABC News
Steph Zillman
Companies in Queensland that suffer data breaches may be required to report incidents to the state's privacy commissioner, under laws now being considered by the state government.
China
China to punish data exports to overseas courts as Beijing beefs up defence against US long arm
South China Morning Post
@MashaBorak
A clause has been added to China’s draft data security law that will punish Chinese companies for handing over domestically stored data to foreign police, courts and investigators without Beijing’s consent, a move that will make it harder for overseas law enforcement agencies to get data out of China.
‘Are You Like This Doggy?’ U.S. Embassy Asked Chinese Students. It Backfired.
The New York Times
@mikeives
In a social media post about visa applications, the consular section in Beijing posed a question that some critics called racist.
Ant Looks to Revamp a Controversial Business Without Sparking an Outcry
The Wall Street Journal
@QiZHAI @jingyanghk @xieyuxy
Ant Group Co., which has pledged to get all its financial services fully regulated, is exploring ways to revamp a popular and controversial product that nearly 91 million Chinese citizens count on.
Netizen Voices: In Hu Xijin Controversy, Nationalist Netizens Turn On One of Their Own
China Digital Times
John Chan
Last week, a Weibo post by the CCP Central Political and Legal Affairs Commission, China’s top legal enforcement authority, ignited a firestorm of controversy on Chinese social media. The controversy began after the Commission’s account uploaded a post comparing the mass funeral pyres in India amid the country’s worst coronavirus outbreak with China’s recent Tianhe space station rocket launch.
‘Dog Biting Dog’: China’s Online Fight Could Further Empower Beijing
The New York Times
@LiYuan6
Lawsuits are flying and tempers are flaring on the Chinese internet, home to the world’s largest single group of internet users. Beijing made it abundantly clear late last year that it was serious about curbing the power of a handful of companies that dominate online life in China. Now China’s internet companies are kowtowing to Beijing and trying to make their rivals look bad instead of correcting their own anticompetitive behavior.
USA
Cyberattack Forces a Shutdown of a Top U.S. Pipeline
The New York Times
@SangerNYT @ckrausss @nicoleperlroth
One of the nation’s largest pipelines, which carries refined gasoline and jet fuel from Texas up the East Coast to New York, was forced to shut down after being hit by ransomware in a vivid demonstration of the vulnerability of energy infrastructure to cyberattacks.
The Colonial Pipeline Hack Is a New Extreme for Ransomware
Wired
@a_greenberg
For years, the cybersecurity industry has warned that state-sponsored hackers could shut down large swathes of US energy infrastructure in a geopolitically motivated act of cyberwar. But now apparently profit-focused cybercriminal hackers have inflicted a disruption that military and intelligence agency hackers have never dared to, shutting down a pipeline that carries nearly half the fuel consumed on the East Coast of the United States.
Ransomware Infection on Colonial Pipeline Shows Potential for Worse Gas Disruption
Zetter
@KimZetter
Colonial Pipeline says ransomware only infected its business network, not the operations network that controls gas flow. But experts say it had potential to spread to control network and suppliers
Colonial Hackers Stole Data Thursday Ahead of Shutdown
Bloomberg
The hackers who caused Colonial Pipeline to shut down the biggest U.S. gasoline pipeline on Friday began their blitz against the company a day earlier, stealing a large amount of data before locking computers with ransomware and demanding payment, according to people familiar with the matter. The intruders, who are part of a cybercrime gang called DarkSide, took nearly 100 gigabytes of data out of the Alpharetta, Georgia-based company’s network in just two hours on Thursday, two people involved in Colonial’s investigation said.
Why Trump’s new blog could lead to more social media takedowns
Politico
@viaCristiano @NickNiedz
Former President Donald Trump launched a new blog Tuesday to get his message out to users, a task that's been complicated by his bans from Facebook, Twitter and other social media platforms. But the move could actually also lead to more takedowns of his remarks online.. Now, Trump has launched a web page making it easier for users to post his remarks verbatim to both Facebook and Twitter, and it could lead to more run-ins with the social media companies policies.
The risks of Covid 'vaccine passports' are scarier than you might think
MSNBC
@tiffanycli
Without a federal privacy law, most Americans have little recourse if a vaccine passport app violates individual privacy rights.

The Lithium Gold Rush: Inside the Race to Power Electric Vehicles
The New York Times
@ivanlpenn @EricLiptonNYT
Atop a long-dormant volcano in northern Nevada, workers are preparing to start blasting and digging out a giant pit that will serve as the first new large-scale lithium mine in the United States in more than a decade — a new domestic supply of an essential ingredient in electric car batteries and renewable energy.
US spy agencies review software suppliers' ties to Russia following SolarWinds hack
CyberScoop
@snlyngaas
U.S. intelligence agencies have begun a review of supply chain risks emanating from Russia in light of the far-reaching hacking campaign that exploited software made by SolarWinds and other vendors, a top Justice Department official said.
Florida man tried to track his robbery victim by attaching an iPhone to his car, police say
The Washington Post
The highly unusual method Derrick Maurice Herlong is said to have used to surveil his alleged victim is bound to raise some concerns for the privacy-conscious.
After update, only 4 percent of iOS users in U.S. let apps track them
Mashable
@realkrauswife
Apple released iOS 14.5 to the public at the end of April, which included the ability to stop apps from tracking your activity for ad targeting purposes. New data shows just how popular the feature is.
Honeywell gets hit with $13M fine for defense export violations
Defense News
@reporterjoe
The U.S. State Department announced it reached a $13 million settlement with American defense firm Honeywell over allegations it exported technical drawings of parts for the F-35 fighters and other weapons platforms to China and other foreign countries.
The FBI is breaking into corporate computers to remove malicious code – smart cyber defense or government overreach?
The Conversation
@CyberPeaceProf
The FBI has the authority right now to access privately owned computers without their owners’ knowledge or consent, and to delete software. It’s part of a government effort to contain the continuing attacks on corporate networks running Microsoft Exchange software, and it’s an unprecedented intrusion that’s raising legal questions about just how far the government can go.

North-East Asia
Japanese companies ditch Chinese drones over security concerns
Nikkei Asia
Leading Japanese infrastructure companies will end their use of Chinese-made drones, joining in the government's efforts to curb the potential security risks.
UK
UK spies warn local authorities over ‘smart city’ tech risks
Financial Times
Smart city technology designed to streamline public services could prove an “attractive target” for hostile states seeking to disrupt Britain’s infrastructure or steal sensitive data, UK spies have warned. The intervention by the National Cyber Security Centre, a branch of GCHQ, reflects growing fears in the intelligence community that local authorities may inadvertently enter risky contracts which could expose them to cyber attack or compromise individuals’ privacy. A deal that was aborted at the last minute involved Bournemouth council in Dorset, which was preparing a contract with the Chinese ecommerce company Alibaba to provide “smart place” services, the Financial Times has discovered.
University plays down links to China rocket firm
The Times (UK)
The principal of Strathclyde University has played down a potentially embarrassing tie-up with a Chinese rocket manufacturer that is now linked to the persecution of Uighur Muslims. Professor Sir Jim MacDonald admitted that the university had collaborated with the China Academy of Launch Vehicle Technology, whose parent company makes drones that have since been used in the persecution of minorities.
How Beijing bought up Britain
The Times (UK)
@JamieNimmo63 @RobertEJWatts
The Cameron era kick-started a wave of Chinese investment in the UK that has risen in recent years, despite increasing concern in Boris Johnson’s government over human rights abuses and spying.
Europe
Why Germany’s investment in Open RAN will not solve its 5G problem
European Council on Foreign Relations
@Beryl Thomas
On the path to Germany’s 5G network rollout, Berlin has made a misguided investment in Open RAN, an unproven telecoms industry concept that promises much but has so far produced little.
Read more on ensuring a 5G ecosystem of trusted vendors and technology from ASPI ICPC here.
Russia
Putin Finds Ally in China’s TikTok in Crackdown on Critics
Bloomberg
TikTok, owned by China-based ByteDance Ltd., is among the global social media companies coming under increasing pressure to remove anti-government posts in Russia as President Vladimir Putin cracks down on dissent. It has even won praise from Russian officials who say it’s more willing than some other companies to remove content. The Kremlin approached Chinese authorities about anti-government content on TikTok earlier this year, according to an official familiar with Russia’s social media policy who asked not to be identified because the information is not public. The amount of critical content has declined as TikTok uses bans to weed out undesirable posts, the person said.
The Americas
NuraLogix’s work on public surveillance tools raises concerns about cooperating with firms tied to Chinese government
The Globe and Mail
David Green
For the past six years, Toronto-based NuraLogix has been working on technology that translates blood flow patterns on a person’s face into insights about their health and psychology. Based on a 30-second video, the company’s app uses artificial intelligence to track changes in the translucency of facial skin, enabling health professionals to remotely monitor high blood pressure and cardiovascular disease..But in 2018, despite the advice of the U.S. security officials, the company agreed to co-operate with Hangzhou-based Joyware Electronics to develop emotional recognition technology for use in public security settings such as railway stations and airports. Joyware sells facial recognition-enabled public security services, including the “Sharp Eyes” system that has been used to persecute Uyghur Muslims in Xinjiang, where Canada’s Parliament has declared a genocide is ongoing.
Middle East
Conspiracy is hard': Inside the Trump administration's secret plan to kill Qassem Soleimani
Yahoo! News
Jack Murphy & Zach Dorfman
Capturing Soleimani’s voice on audio was a relatively rare occurrence, and would have been considered an intelligence coup — particularly if he was discussing planned attacks, said former CIA officials. The CIA and the NSA have gone to extraordinary lengths to compromise the electronic devices and communications of Iranian leadership and their associates, say former intelligence officials — spending what some officials estimated is “hundreds of millions” of dollars over the years on associated programs.
Misc
The Chip Shortage Keeps Getting Worse. Why Can’t We Just Make More?
Bloomberg
@ianmking @ad_leung @pogkas
Shortages of semiconductors are battering automakers and tech giants, raising alarm bells from Washington to Brussels to Beijing. The crunch has raised a fundamental question for policymakers, customers and investors: Why can’t we just make more chips?
To Make These Chips More Powerful, IBM Is Growing Them Taller
Wired
Computer chips might be in short supply at the moment, but chipmakers will continue wringing more power out of them for a while yet it seems. Researchers at IBM have demonstrated a way to squeeze more transistors onto a chip, a feat of nanoscopic miniaturization that could significantly improve the speed and efficiency of future electronic devices.
Events
ASPI Webinar: In-Conversation with Julie Inman Grant, eSafety Commissioner
ASPI
ASPI's International Cyber Policy Centre is delighted to invite you to the webinar ‘In-Conversation with Julie Inman Grant, eSafety Commissioner’. With legislation proposed to increase the broad powers of the eSafety Commissioner to tackle adult cyber abuse and image-based abuse, the eSafety Commissioner Julie Inman Grant joins ASPI ICPC Senior Analyst, Tom Uren to provide an overview of the eSafety Commissioner’s role and functions and what these new powers may mean. The Commissioner will deliver remarks and context about eSafety’s approach to supporting Australian citizens online and the different technology challenges and trends that are emerging. These include policy and societal issues such as deepfakes, decentralisation, the safety risks of immersive technologies, and end-to-end encryption. This will be followed by a moderated Q&A with the online audience.
Research
Network effects: Europe’s digital sovereignty in the Mediterranean
European Council on Foriegn Relations
@philoteo @Federico Solfrini @arturo_varvelli
The EU has the ambition and potential to become a sovereign digital power, but it lacks an all-encompassing strategy for the sector, in which individual governments are still the key players
Jobs
International Cyber Policy Centre – Strategic engagement, program & research coordinator
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has an outstanding early career role for a talented and proactive individual to support senior centre staff on strategic engagement, program and research coordination.



