Deal to access US data for law enforcement at risk over controversial Aust law | Top secret Russian unit seeks to destabilize Europe | HK govt would not rule out internet controls to curb protests


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference
A landmark data access agreement being negotiated between the United States and Australia to aid law enforcement is at risk because of Australian legislation targeting encrypted communications, according to the chairman of a US congressional committee responsible for reviewing the arrangements. The Sydney Morning Herald
A top secret Russian unit seeks to destabilize Europe, says security officials. The purpose of Unit 29155, which has not been previously reported, underscores the degree to which the Russian president, Vladimir V. Putin, is actively fighting the West with his brand of so-called hybrid warfare — a blend of propaganda, hacking attacks and disinformation — as well as open military confrontation. The New York Times
Hong Kong government would not rule out internet controls to curb protests, says a member of the Hong Kong government’s top advisory body. Hong Kong Free Press
ASPI ICPC
Australia's Cyber Strategy, version 2.0
ASPI ICPC
Back in 2016, Australia launched its first national cybersecurity strategy. The strategy covers a four-year period to 2020, and given the changes in the security environment, an update is now clearly warranted. To that end, the government has just launched a discussion paper to kick off the public consultation. The closing date for submissions on the discussion paper is 1 November. To complement the public submission process, ASPI’s International Cyber Policy Centre is initiating a public debate on what should be included in the next cybersecurity strategy. Contributions will be compiled into a report that we will deliver to the Department of Home Affairs to inform the strategy’s development. Follow the debate here.
e-Governance in the Pacific: mapping a way forward
DFAT
@ASPI_ICPC @egovacademy @dfat
Australia's Cyber Cooperation Program is supporting governments in the Pacific to maximise opportunities offered by the digital age. Partnering with the e-Governance Academy of Estonia and the Australian Strategic Policy Institute the project worked with Fiji, Tonga, Samoa, Vanuatu, Papua New Guinea, Solomon Islands, and Kirbati to develop a baseline assessment of existing e-Governance capabilities and required resources to achieve each country's desired digital transformation.

The final project workshop was held in Canberra on 1-3 October 2019 to share key findings and observations of the baseline assessment and to discuss some common issues to all Pacific states. Watch the video here.
China’s surveillance tech is spreading globally, raising concerns about Beijing’s influence
CNBC
@ArjunKharpal
Some of these so-called "smart city" projects, which include surveillance technologies, are underway in Western countries, particularly in Europe, including Germany, Spain and France, according to analysis by the Australian Strategic Policy Institute…“I think that sometimes there is an assumption that ‘oh well when we roll out this technology we aren’t going to use it in a negative way, we are using it to provide services or we are using it in a way that is seen as acceptable, socially acceptable in our society,’” Samantha Hoffman, a fellow at ASPI’s Cyber Centre, told CNBC’s “Beyond the Valley” podcast.
Australia
Deal to access US data for law enforcement at risk over controversial Australian law
The Sydney Morning Herald
@fergushunter
A landmark data access agreement being negotiated between the United States and Australia to aid law enforcement is at risk because of Australian legislation targeting encrypted communications, according to the chairman of a US congressional committee responsible for reviewing the arrangements. US Attorney-General William Barr and Home Affairs Minister Peter Dutton have kicked off negotiations for a deal to improve access to electronic data held by companies in the other country. The "executive agreement" would be struck under the Clarifying Lawful Overseas Use of Data (CLOUD) Act legislated in Washington last year.
US whistleblower dropped from speaking at Melbourne cybersecurity conference
ABC
@arielbogle
A high-profile American whistleblower and a privacy researcher have been unexpectedly dropped from addressing a Government-backed cybersecurity event underway in Melbourne.
Cyber Week launches with focus on cyber safety, security
iTWire
Australian Cyber Week 2019 has launched with a week-long series of events and activities nationally coordinated by AustCyber – the Australian Cyber Security Growth Network - and with a focus on cybercrime and Australia's growing cyber security sector.
China
Hong Kong gov’t would not rule out internet controls to curb protests, says top advisor Ip Kwok-him | Hong Kong Free Press HKFP
Hong Kong Free Press
@krislc
A member of the government’s top advisory body has said the authorities would not rule out internet controls in order to curb the ongoing protests. Chief Executive Carrie Lam, after seeking advice from the Executive Council, invoked powers under the Emergency Regulations Ordinance and enacted an anti-mask law on Saturday. However, the new law sparked fresh demonstrations and unrest over the weekend.
China and Taiwan clash over Wikipedia edits
BBC
Carl Miller
The edit war over Taiwan was only one of a number that had broken out across Wikipedia's vast, multi-lingual expanse of entries. The Hong Kong protests page had seen 65 changes in the space of a day - largely over questions of language. Were they protesters? Or rioters?
Anomali Threat Research Team Discovers Cyber Campaign Conducted by Mustang Panda, a Known China Backed APT
West
Anomali, a leader in intelligence-driven cybersecurity, today published research conducted by the Anomali Threat Research Team. It reveals an ongoing campaign carried out by Mustang Panda, an APT known to be backed by China. The team first revealed these findings on Wednesday, Oct. 2, during Anomali Detect 19, the company’s annual user conference, in a session titled: “Mustang Panda Riding Across Country Lines.”
Regulation of the internet in China: An explainer
Asia Dialogue
@lotus_ruan
This article provides an overview of how China manages social media via a broad range of regulations and advanced filtering technologies. Despite these legal and scientific advances, however, the evidence shows that China’s sophisticated information control system, which relies heavily on private companies, is neither monolithic nor consistently applied
Book reviews: Document Number Nine
London Review of Books
John Lanchester
Book review of The Great Firewall of China: How to Build and Control an Alternative Version of the Internet by James Griffiths and We Have Been Harmonised: Life in China’s Surveillance State by Kai Strittmatter.
US
Senate Intel releases 2nd volume of report on 2016 Russian interference
Axios
@zacharybasu
The Senate Intelligence Committee released Tuesday the second volume of its report on Russian interference in the 2016 presidential election, which focuses on the social media disinformation campaign led by the Kremlin-backed Internet Research Agency.
U.S. announces visa restrictions on Chinese officials for Uighur abuses
Axios
@zacharybasu
The State Department on Tuesday announced that it would impose visa restrictions on Chinese government officials who are believed to be responsible for, or complicit in, the mass detention and surveillance of Uighurs and other Muslim minority groups in Xinjiang province.
As U.S. Takes Aim at Chinese Tech Firms, Trump Signals a Strategy Shift
The New York Times
@paulmozur @ewong
In blacklisting surveillance companies, the United States is the first major government to punish China for its crackdown on Muslims.
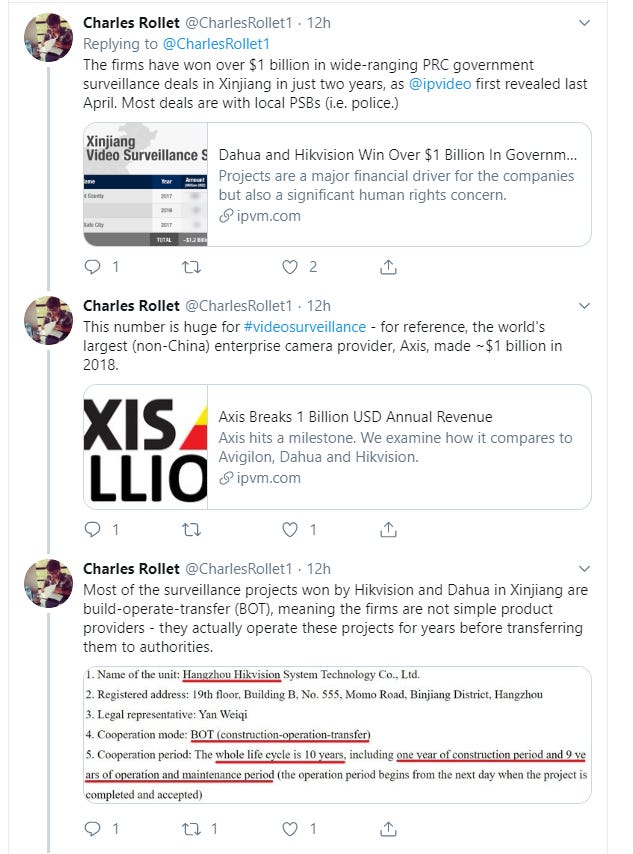
Twitter thread on Hikvision and Dahua's extensive involvement in Xinjiang, which resulted in US government sanctions.
China's vise grip on corporate America
Axios
@erica_pandey
The NBA’s swift apology to Chinese fans for a single tweet in support of Hong Kong protestors is part of a troubling trend: The Communist Party in Beijing is setting boundaries for what Americans more than 7,000 miles away are willing to say on sensitive issues.
Inside New York City’s Partnership With Israeli iPhone Hacking Company Cellebrite
Medium
Michael Hayes
Documents reveal the Manhattan DA subscribes to a program that lets authorities break into iPhones in-house.
Twitter admits email address and phone number given for security purposes was used for targeted ads
Reclaim The Net
Today, Twitter admitted to a privacy blunder where the phone number and email address of some of its users that are provided for security purposes were used for targeted advertising purposes.
FBI’s Use of Surveillance Database Violated Americans’ Privacy Rights, Court Found
The Wall Street Journal
@dnvolz @ByronTau
Some of the FBI’s electronic surveillance activities violated the constitutional privacy rights of Americans swept up in a controversial foreign intelligence program, a surveillance court has ruled.
North Asia
Japan to expand export controls to prevent leak of cutting-edge AI, biotech
The Japan News
The government plans to strengthen export controls to prevent advanced technologies from getting into the hands of foreign countries, it has been learned. The government will review the implementation of the Foreign Exchange and Foreign Trade Law as early as fiscal 2020 to make artificial intelligence (AI), biotechnology and other technologies subject to export controls, according to informed sources.
Southeast Asia
Pollution app pulled in Vietnam after 'coordinated campaign' of abuse
France24
A leading air quality monitoring app was removed from Vietnam's Apple and Google stores after it said it was attacked in a "coordinated campaign" for posting pollution data from the country's smog-choked capital. AirVisual's Facebook page was also taken down in Vietnam after a deluge of messages from users accusing the site of publishing unreliable data in a bid to sell its products.
South Asia
India restricts universities from tie-ups with Chinese institutions, days before Modi expected to meet Xi
South China Morning Post
@Vasu_Sridharan
India has introduced restrictions on universities seeking tie-ups with Chinese academic institutions in a move to increase scrutiny of collaborative projects involving Beijing. The news comes just days before Indian Prime Minister Narendra Modi and Chinese President Xi Jinping are expected to meet for a bilateral summit in India.
Europe
Austria’s employment agency rolls out discriminatory algorithm, sees no problem
Algorithm Watch
Von Nicolas Kayser-Bril
AMS, Austria’s employment agency, is about to roll out a sorting algorithm that gives lower scores to women and to the disabled. It is very likely illegal under current anti-discrimination law.
Russia
Top Secret Russian Unit Seeks to Destabilize Europe, Security Officials Say
The New York Times
@mschwirtz
The purpose of Unit 29155, which has not been previously reported, underscores the degree to which the Russian president, Vladimir V. Putin, is actively fighting the West with his brand of so-called hybrid warfare — a blend of propaganda, hacking attacks and disinformation — as well as open military confrontation.
The Untold Story of NotPetya, the Most Devastating Cyberattack in History
Wired
@a_greenberg
Crippled ports. Paralyzed corporations. Frozen government agencies. How a single piece of code crashed the world.
Misc
How Telegram Became White Nationalists' Go-To Messaging Platform
Vice
@misstessowen
More than two-thirds of 150 far-right channels were created in 2019, an exclusive analysis by VICE News found.
Most Deepfakes Are Used for Creating Non-Consensual Porn, Not Fake News
Vice
@josephfcox
While media, politicians, and technologists panic over the risk of deepfakes impacting elections, a new study has found that the vast, vast majority of deepfakes are pornographic in nature. On top of that, to the surprise of absolutely no one, all of the pornographic deepfakes analyzed in the study exclusively targeted women.
Tesla's Smart Summon problems seen liability of app 'driver' for now
Financial Review
@SuzanneBarlyn
Tesla owners summoning their driverless cars in parking lots are likely liable for crashes, lawyers said after a series of internet videos showed problems with cars running new software.
How a 'quantum apocalypse' could cripple governments and break the internet
The Independent
@ADCuthbertson
A new era of unfathomably fast computers is just a few years away, with quantum computers set to transform the way we communicate, cure disease, and even solve problems previously thought impossible. But some computing experts fear functional quantum computers could also effectively break the internet as we know it.
Events
Cyber Security Hypothetical – Panel
UNSW
We invite you to join us on 22 October, in challenging paradigms and provoking discussion around this important topic that impacts and targets us all. Cyber Security Hypothetical will be led and moderated by Mr Steve Wilson and panellists will include MAJGEN Marcus Thompson, Professor Michael Frater, Mr Alastair MacGibbon, Ms Kate Carruthers and Mr Justin Warren.
The rise of information warfare: in-conversation with Peter W. Singer
ASPI ICPC
This event for 29 October it SOLD OUT but you can watch a live stream on ASPI’s Facebook page.
ASPI's International Cyber Policy Centre invites you to an in-conversation with Peter W. Singer and Danielle Cave to consider the rise of information warfare. Peter Warren Singer is strategist and senior fellow at New America. He has been named by the Smithsonian as one of the nation’s 100 leading innovators, by Defense News as one of the 100 most influential people in defense issues, by Foreign Policy to their Top 100 Global Thinkers List, and as an official “Mad Scientist” for the U.S. Army’s Training and Doctrine Command. A drinks and canapes reception will conclude the event. This event is kindly supported by Microsoft.

