Library of Congress bomb suspect live-streamed on Facebook for hours before being blocked | Beijing passes critical cybersecurity regulations | Flubot text message voicemail scam targets Australians
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
The man suspected of making a bomb threat near the Library of Congress live-streamed his anti-government remarks for hours before Facebook took down his account on Thursday afternoon. POLITICO
China's State Council issued a long-anticipated set of cybersecurity regulations on Tuesday that provide guidance about how regulators will designate "Critical Information Infrastructure" operators and the regulatory scrutiny they will face. Protocol
A new scam known as "Flubot" is sending thousands of text messages to Australians as they wait anxiously for updates on COVID tests and vaccination appointments. ABC News
ASPI ICPC
How do far-right extremists raise money?
ABC Radio National
@frankelly08
The threat of far-right extremism is growing in Australia; ASIO boss Mike Burgess says it's now 40 per cent of the agency's terror-related workload. ASPI has been looking at how these far-right groups raise money online. Guest: Ariel Bogle, Analyst with ASPI's International Cyber Policy Centre
Australia’s far right uses Google ads and cryptocurrency to fund their hate
Crikey
@cameronwilson
What Bogle found is that far-right funding has moved from being structured around groups — i.e. charging membership dues — towards an individual creator model, not unlike that of an Instagram influencer. Individual right-wing extremists solicit donations or earn money through creating engaging and credible content (“[right-wing content creators] may be supported for ostensibly ‘living’ the ideology they propagate”) from their audiences. This arrangement, Bogle argues, can also incentivise people to make right-wing extremist content to earn money rather than making content to support their beliefs. The report documents more than 20 tools used to solicit donations, facilitate transactions, and earn and store money. These range from major platforms like Google and Amazon advertising programs used on far-right websites to niche “alt-tech” platforms which offer alternatives to popular streaming or video platforms. Activities supported by these platforms include livestreamed interviews, selling merchandise featuring right-wing extremist propaganda, or cryptocurrencies that allow money transfers that are difficult or impossible to trace.
Far-right extremists raise money through Buy Me A Coffee, YouTube
Australian Financial Review
@jessicasier
Right-wing extremists are using platforms such as YouTube, PayPal and Buy Me A Coffee to raise money to support their nefarious activities, says the Australian Strategic Policy Institute, which is calling for anti-money laundering laws to apply to more technology businesses. APSI analyst Ariel Bogle wants the federal government to develop a centralised hate crime and statistics database to track and understand the financial activities of extremists operating in Australia. Ms Bogle has been looking at how far-right “influencers” raise money online. She is also calling for regulators to consider whether emerging platforms have obligations under laws such as the Anti-Money Laundering and Counter-Terrorism Financing Act and the Proceeds of Crime Act.
Read our new report Buying and selling extremism.

World
Global organizations urge Apple to drop child safety features
Protocol
@issielapowsky
In a letter to Tim Cook, groups like the ACLU and the Center for Democracy and Technology warned that the update could have dangerous human rights implications.
Opinion | We built a system like Apple’s to flag child sexual abuse material — and concluded the tech was dangerous The Washington Post
Australia
Flubot text message voicemail scam targets nervous Australians waiting for COVID updates
ABC News
@kemiimaguire
A new scam known as "Flubot" is sending thousands of text messages to Australians as they wait anxiously for updates on COVID tests and vaccination appointments.
International travel is (kind of) back. So where's Australia's vaccine passport?
ABC News
In recent weeks, we’ve heard a lot about domestic vaccine passports that would allow vaccinated Australians greater freedoms. From a technical perspective, such passports are relatively simple. Services Australia has already negotiated a deal with Apple and Google to allow iPhone and Android digital wallets that show Australians’ COVID-19 vaccination records from their MyGov accounts. Vaccine passports for international travel, however, are far more complicated.
China
Beijing passes critical cybersecurity regulations
Protocol
@shenlulushen
China's State Council issued a long-anticipated set of cybersecurity regulations on Tuesday that provide guidance about how regulators will designate "Critical Information Infrastructure" operators and the regulatory scrutiny they will face. The Critical Information Infrastructure Security and Protection Regulations are vastly different from what's found in the first draft, published in 2017. Together, the rules will subject tech companies that fall under the CII category to stricter cybersecurity requirements.
China's Xi emphasizes 'common prosperity' at finance economy meeting
CNBC
@chengevelyn
Chinese President Xi Jinping emphasized at a finance and economic meeting Tuesday the need to support moderate wealth for all — or the idea of “common prosperity,” which analysts have said is behind the latest regulatory crackdown on tech companies.
Tencent earmarks US$7.7 billion for ‘common prosperity’ to answer Xi Jinping’s call for equality South China Morning Post
China's regulator demands SOEs to enhance scientific innovation
Global Times
China's state-owned assets regulator told centrally-administered state-owned enterprises (SOEs) to invest more in scientific innovation and plans to build new central SOEs groups at due time to boost the development of strategic emerging industries... In particular, the SOEs should integrate into innovation in basic research and applied basic research, make breakthrough on core technologies for industrial machine tools, high-end chips, new materials, and new-energy vehicles
Tencent warns investors China’s tech regulation will intensify
Financial Times
@edwardwhitenz
Tencent has warned investors that more regulatory changes will impact China’s technology sector. The company issued the warning as it reported a jump in second-quarter profits, bucking expectations that the social media, gaming and fintech group would be damaged by the regulatory storm battering much of the technology industry in China.
China rebukes 43 apps including Tencent's WeChat for breaking data transfer rules Reuters
What China really fears about its big tech companies Australian Financial Review
Read our new report Reining in China’s Technology Giants.
China’s propaganda firehose is going after the BBC
WIRED UK
@mattburgess1
Chinese trolls and fake news websites have been attacking the BBC in a bid to undermine its credibility, new research published today claims. The online influence operation, which is being linked to the Chinese Communist Party (CCP), is seemingly a response to the BBC’s reporting on human rights abuses against Uyghur Muslims and state-backed misinformation campaigns.
Read our data-driven investigation from earlier this year - Trigger warning: The CCP’s coordinated information effort to discredit the BBC.
How the delisting of Chinese firms on American exchanges might play out
The Economist
The Holding Foreign Companies Accountable Act, requires companies traded on American exchanges to submit to audits or face delisting within three years. The precise rules are still being drawn up, but will probably eventually involve a great shedding of shares.
Why Alibaba’s sexual assault scandal is no #MeToo moment - Rest of World
Rest Of World
@dong_mengyu
Alibaba's corporate culture is far from the only obstacle to creating a more equitable workplace for women in China.
How Award-Winning Journalist Uses Technology to Detail Abuses in Xinjiang
Voice of America
[Journalist Megha Rajagopalan's] efforts, which included analyzing satellite imagery to search for evidence of mass prison and internment camps, earned Rajagopalan and her team -- architect Alison Killing and digital security trainer Christo Buschek--a Pulitzer Prize this year.
USA
Library of Congress bomb suspect livestreamed on Facebook for hours before being blocked
POLITICO
@birnbaum_e
The man suspected of making a bomb threat near the Library of Congress livestreamed his anti-government remarks for hours before Facebook took down his account on Thursday afternoon.
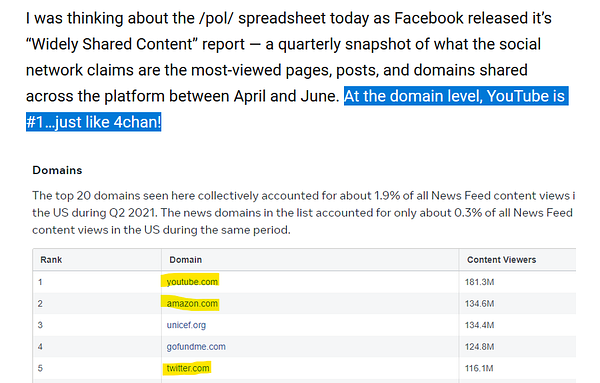
Only Facebook knows the extent of its misinformation problem. And it’s not sharing, even with the White House.
Washington Post
@lizzadwoskin @Cat_Zakrzewski @tylerpager
In tense meetings between Facebook executives and White House officials tasked with fighting the pandemic in recent months, Biden’s team begged the social network giant for something only Facebook possessed: its data. Facebook’s vast data trove could be crucial to understanding how medical misinformation has spread rampantly on the company’s platforms — and more importantly, to overcoming the skepticism about vaccines that had arisen from it, according to three administration officials who spoke on the condition of anonymity to discuss sensitive matters.

FTC files renewed antitrust complaint against Facebook
CNBC
The Federal Trade Commission filed a new antitrust complaint against Facebook on Thursday, continuing its fight in federal court after a judge threw out its initial claims.
FTC says Facebook has been a monopoly ‘since at least 2011’ in amended antitrust complaint The Verge
FTC Alleges Facebook Resorted to Illegal Buy-or-Bury Scheme to Crush Competition After String of Failed Attempts to Innovate Federal Trade Commission
Trump, QAnon and an impending judgment day: Behind the Facebook-fueled rise of The Epoch Times
NBC News
@BrandyZadrozny @oneunderscore__
Started almost two decades ago with a stated mission to “provide information to Chinese communities to help immigrants assimilate into American society,” The Epoch Times now wields one of the biggest social media followings of any news outlet.
‘This is warfare:’ Trump allies Flynn, Bannon pushed conspiracies at ritzy party backed by Chinese exile
CNBC
@schwartzbCNBC
It was supposed to be a celebration for a movement that opposes the Chinese Communist Party. Instead, the swanky private party, held in June at the top of One World Trade Center, served as a platform for several of former President Donald Trump's allies, including former advisor Steve Bannon and personal attorney Rudy Giuliani, to spew anti-government rhetoric and conspiracy theories about the 2020 election..It was streamed on YouTube, which has 30,000 views so far. Neither the YouTube video nor the invitation to the event have been reported on… The conspiracy theories and speakers heard at the event fit a pattern for the Guo-backed organizations. The nonprofits are cited in a report by Graphika, which describes a "network [that] acts as a prolific producer and amplifier of mis- and disinformation, including claims of voter fraud in the U.S., false information about Covid-19, and QAnon narratives."
Rubio wants Biden to block TikTok after Chinese govt stake in subsidiary of parent company
Reuters
@davidshepardson
Republican Senator Marco Rubio urged President Joe Biden on Tuesday to block short-form video app TikTok in the United States after China took an ownership stake in a key subsidiary of ByteDance, the Beijing-based parent company of TikTok.
The FBI’s Delta Protocol warns startups of Chinese spying
Protocol
@bizcarson
It's not the Hollywood image of espionage, but the risk to tech companies is real. Employees are being coerced by foreign autocracies into stealing information or handing over login credentials.
How AI-powered tech landed man in jail with scant evidence
AP News
@garanceburke @mendozamartha @JulietLinderman @mtarm
A Chicago grandfather was charged with murdering a man he gave a ride to on a night of protests over police brutality. Prosecutors said a secret algorithm, tied to a network of surveillance microphones, was key evidence to lock him up.
South-East Asia
Indonesia’s AI Promise in Perspective
Center for Security and Emerging Technology
Kayla Goode & Heeu Millie Kim
The United States and China are keeping an eye on Indonesia’s artificial intelligence potential given the country’s innovation-driven national strategy and flourishing AI industry.
South and Central Asia
Today’s Taliban uses sophisticated social media practices that rarely violate the rules
Washington Post
@craigtimberg @viaCristiano
In accounts swelling across Facebook, Twitter and Instagram — and in group chats on apps such as WhatsApp and Telegram — the messaging from Taliban supporters typically challenges the West’s dominant image of the group as intolerant, vicious and bent on revenge, while staying within the evolving boundaries of taste and content that tech companies use to police user behavior. The tactics overall show such a high degree of skill that analysts believe at least one public relations firm is advising the Taliban on how to push key themes, amplify messages across platforms and create potentially viral images and video snippets — much like corporate and political campaigns do across the world.
How Social Media Helped ‘Taliban 2.0’ Take Control of Afghanistan
VICE
@gav_butler
The modern, tech-savvy Taliban aren’t the same as they were 20 years ago. Now they’re using the internet to control the narrative—and assert their dominance.Western far-right groups claim Taliban victory as their own POLITICO


I-T dept searches ZTE India's five premises, including CEO residence
ETTelecom
The Central Board of Direct Taxes (CBDT) said in a statement Tuesday that searches were conducted on Monday at five locations including the corporate office, residence of foreign director, residence of company secretary, accounts person and the cash handler of a foreign subsidiary company in India.
UK
Online fraud now Isle of Man's most common crime
BBC News
Online fraud is now the most common crime on the Isle of Man following a rise in scams during the coronavirus pandemic, police have revealed.
Europe
Serbia’s smart city has become a political flashpoint
WIRED UK
@brigancontraria
Belgrade has been kitted out with Chinese security cameras. Activists and Europe are both worried.
Russia
This $500 Million Russian Cyber Mogul Planned To Take His Company Public—Then America Accused It Of Hacking For Putin’s Spies
Forbes
@iblametom
The tycoon whose Positive Technologies was recently hit with U.S. sanctions insists he just wants to help protect all companies from hackers. U.S. security officials don’t buy it.
Misc
What If the Best Defense Is a Good Defense (Instead of Offense Rebranded as Active Defense)? – Offensive Cyber Working Group
Offensive Cyber Working Group
@josephinecwolff
In cybersecurity, the difference between offense and defense is at once extremely straightforward and incredibly difficult to pin down. It is straightforward because defending your own networks and data and attacking someone else’s look completely different: the former involves implementing security controls and detection systems within the confines of your own computer systems, while the latter involves exploiting vulnerabilities in someone else’s systems. So it really should not be difficult to designate any particular activity in cyberspace by an individual country as offense or defense—except that, increasingly, countries seem to view the best cyber defense as, well, offense.
Read our work on offensive cyber: Australia's Offensive Cyber Capability & Defining offensive cyber capabilities
Gaming and Extremism: The Extreme Right on Discord
ISD
This briefing is part of ISD’s Gaming and Extremism Series exploring the role online gaming plays in the strategy of far-right extremists in the UK and globally. This is part of a broader programme on the ‘Future of Extremism’ being delivered by ISD in the second half of 2021, charting the transformational shifts in the extremist threat landscape two decades on from 9/11, and the policy strategies required to counter the next generation of extremist threats. It provides a snapshot overview of the extreme right’s use of Discord.
This $600 Million Crypto Heist Is the Most Bizarre Hack in Recent Memory
VICE
@lorenzofb
After stealing around $600 million in cryptocurrency, and returning most of it, a hacked cryptocurrency platform rewarded the hacker with half a million dollars.
Events


Jobs
ICPC Senior Analyst or Analyst - China
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has a unique opportunity for exceptional and experienced China-focused senior analysts or analysts to join its centre. This role will focus on original research and analysis centred around the (growing) range of topics which our ICPC China team work on. Our China team produces some of the most impactful and well-read policy-relevant research in the world, with our experts often being called upon by politicians, governments, corporates and civil society actors to provide briefings and advice. Analysts usually have at least 5 years, often 7-10 years’ of work experience. Senior analysts usually have a minimum of 15 years relevant work experience and, in addition to research, they take on a leadership role in the centre and tend to be involved in staff and project management, fundraising and stakeholder engagement.
China Analyst
Trivium China
Are you a China nerd? Do you love reading Chinese policy documents? Do you really love explaining those documents to a broad audience of businesspeople, investors, government officials, and academics?





