New German rules leave 5G telecoms door open to Huawei | Building China's Comac C919 airplane involved a lot of hacking | Encryption laws a CLOUD deal risk
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
Germany has finalised rules for the build-out of 5G mobile networks that, in a snub to the United States, will not exclude China’s Huawei Technologies. Reuters
A report published today shines a light on one of China's most ambitious hacking operations known to date, one that involved Ministry of State Security officers, the country's underground hacking scene, legitimate security researchers, and insiders at companies all over the world. The aim of this hacking operation was to acquire intellectual property to narrow China's technological gap in the aviation industry, and especially to help Comac, a Chinese state-owned aerospace manufacturer, build its own airliner, the C919 airplane, to compete with industry rivals like Airbus and Boeing. ZDNet
Australia’s recently passed encryption laws may undermine the federal government’s hopes of securing a data-sharing deal with the United States, a US House Committee has confirmed. InnovationAus
ASPI ICPC
Engineering global consent: the Chinese Communist Party’s data-driven power expansion
ASPI ICPC
@He_Shumei

The Chinese party-state engages in data collection on a massive scale as a means of generating information to enhance state security—and, crucially, the political security of the Chinese Communist Party (CCP)—across multiple domains. The party-state intends to shape, manage and control its global operating environment so that public sentiment is favourable to its own interests. This report explains how the party-state’s tech-enhanced authoritarianism is expanding globally. The effort doesn’t always involve distinctly coercive and overtly invasive technology, such as surveillance cameras. In fact, it often relies on technologies that provide useful services.
Read Dr Samantha Hoffman’s accompanying article in The Strategist: Engineering global consent: the Chinese Communist Party’s data-driven power expansion
China harvesting data on global scale, Australian report warns
South China Morning Post
@_szheng
An Australian think tank has warned that a global data minThe Australian Strategic Policy Institute (ASPI) released a report on Monday by its Chinese security and politics analyst Samantha Hoffman, which said China had established a “massive and global data collection ecosystem” which could be used to reshape global governance.ing exercise by a Chinese company in partnership with overseas tech firms and universities could be used by Beijing to shape international discourse, promote its social credit system and support China’s military intelligence.
Australia, China tech ties face tough new scrutiny
Asia Times
GTCOM has signed a memorandum of understanding with the University of New South Wales (UNSW) to test applications. The university said in a statement that GTCOM has “no influence on any of UNSW’s programs”, but Australian Strategic Policy Institute analyst Samantha Hoffman told the ABC its function was to support Communist Party security interests.
2019-2020 Global Research Initiative Fellows
Dangerous Speech Project
@jakewallis_asp
ASPI International Cyber Policy Center Senior Analyst Jake Wallis has been named an inaugural 2019-2020 Global Research Initiative fellow.
The World
Without encryption, we will lose all privacy. This is our new battleground
The Guardian
@Snowden
The US, UK and Australia are taking on Facebook in a bid to undermine the only method that protects our personal information.
Malware That Spits Cash Out of ATMs Has Spread Across the World
Vice
@josephfcox
A joint investigation between Motherboard and the German broadcaster Bayerischer Rundfunk (BR) has uncovered new details about a spate of so-called “jackpotting” attacks.
Australia
Encryption laws a CLOUD deal risk
InnovationAus
Australia’s recently passed encryption laws may undermine the federal government’s hopes of securing a data-sharing deal with the United States, a US House Committee has confirmed.
Australian uni delegation to enter new alliance with Chinese unis
The Sydney Morning Herald
@fergushunter
A high-level delegation of Australian university leaders will land in Beijing on Wednesday for a visit aimed at deepening research and education ties with China, as the sector seeks to combat concerns about its growing reliance on the major Asian power.
China
HUGE FAN OF YOUR WORK: How TURBINE PANDA and China's Top Spies Enabled Beijing to Cut Corners on the C919 Passenger Jet
Crowdstrike
In this blog, we take a look at how Beijing used a mixture of cyber actors sourced from China’s underground hacking scene, Ministry of State Security (MSS/国安部) officers, company insiders, and state directives to fill key technology and intelligence gaps in a bid to bolster dual-use turbine engines which could be used for both energy generation and to enable its narrow-body twinjet airliner, the C919, to compete against western aerospace firms.
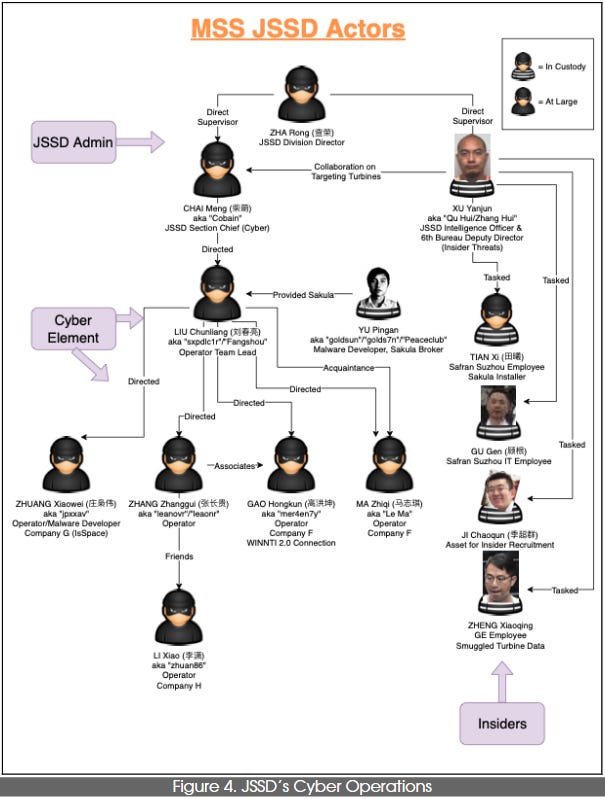
Individuals connected to the Jiangsu State Security Bureau’s espionage operations. Source: Crowdstrike.
Building China's Comac C919 airplane involved a lot of hacking, report says
ZDNet
@campuscodi
A report published today shines a light on one of China's most ambitious hacking operations known to date, one that involved Ministry of State Security officers, the country's underground hacking scene, legitimate security researchers, and insiders at companies all over the world. The aim of this hacking operation was to acquire intellectual property to narrow China's technological gap in the aviation industry, and especially to help Comac, a Chinese state-owned aerospace manufacturer, build its own airliner, the C919 airplane, to compete with industry rivals like Airbus and Boeing.
China’s New Cybersecurity Program: NO Place to Hide
China Law Blog
The core of the plan is for China’s Ministry of Security to fully access the massive amounts of raw data transmitted across Chinese networks and housed on servers in China. Since raw data has little value, the key to the Ministry’s success will be in processing that data. Seeing that this is the key issue, the Ministry has appointed Wang Yingwei to be its new head of the Cybersecurity Bureau..This system will apply to foreign owned companies in China on the same basis as to all Chinese persons, entities or individuals. No information contained on any server located within China will be exempted from this full coverage program.
“We feel like cyber-refugees”: The decline of the last online sanctuary for China’s liberals
Quartz
@Jane_Li911
It’s not easy to be a liberal on China’s internet, but for years alternative thinkers found a refuge on a platform dedicated to film and book reviews that appeared to pass under the radar because of its relatively small size. Now its users fear its days are numbered.
USA
Diminished by controversy and fears, Facebook's Libra staggers on
The Sydney Morning Herald
Facebook’s digital currency project, the Libra Association, was formally launched on Monday but the bid to create a new privately-owned global payments system with its own currency hasn’t exactly got off to the best of starts.
You’re in a Police Lineup, Right Now
The New York Times
@ClareAngelyn
Face-recognition technology is the new norm. You may think, “I’ve got nothing to hide,” but we all should be concerned.
Cyber Command’s bug bounty program uncovers more than 30 vulnerabilities
Cyberscoop
@shanvav
Ethical hackers have found nine “high severity” vulnerabilities and one “critical” vulnerability across Department of Defense proxies, virtual private networks, and virtual desktops through the “Hack the Proxy,” bug bounty program, the DOD’s Defense Digital Service and HackerOne announced Monday.
Fake videos could be the next big problem in the 2020 elections
CNBC
@Gracemzhao
Fake news was a big problem for the 2016 election. “Deepfake” videos could be an even bigger problem in 2020.
North Asian
North Korea is using front companies to steal cryptocurrency
Cyberscoop
@shanvav
North Korean government-backed hackers are targeting cryptocurrency exchanges to try to steal financial resources as Pyongyang searches for ways to fund its regime, two researchers discovered within the past week.
New Zealand
Christchurch attack: New Zealand tries new tactic to disrupt online extremism
The Guardian
@EleanorAingeRoy
Jacinda Ardern says government will double its investigative operation and track down content in a similar manner to child abuse material.
South Asia
China's Huawei says open to 'no backdoor' agreement with India
Reuters
@sankalp_sp
China’s Huawei Technologies is ready to enter into a “no backdoor” agreement with India to allay security concerns, the telecom group’s local head said on Monday, as the giant South Asian country prepares to launch next generation 5G networks.
UK
One in three councils using algorithms to make welfare decisions
The Guardian
@sloumarsh
One in three councils are using computer algorithms to help make decisions about benefit claims and other welfare issues, despite evidence emerging that some of the systems are unreliable.
Europe
New German rules leave 5G telecoms door open to Huawei
Reuters
@Andreas__Rinke @Busvine
Germany has finalised rules for the build-out of 5G mobile networks that, in a snub to the United States, will not exclude China’s Huawei Technologies.
German 5G Rules Avoid Huawei Ban; US Warns on Intel Sharing
Voice of America
"If there's technology that's untrusted deployed in their networks, then we have to reassess how we share information with countries like Germany," Strayer told in a telephone media briefing, though he added he hadn't yet reviewed the German rules, which are open for consultation and could become law by the end of the year.
The Netherlands Releases a Tour de Force on International Law in Cyberspace: Analysis
Just Security
@Schmitt_ILaw
In a July 2019 letter to parliament, the Dutch Minister of Foreign Affairs set out the Government’s views on “the application in cyberspace of relevant elements of existing international law.” That letter has now been made public. It is an extremely granular statement, not only in terms of scope, but also with respect to the legal basis for the positions taken.
Events
Cyber Security Hypothetical – Panel
UNSW
We invite you to join us on 22 October, in challenging paradigms and provoking discussion around this important topic that impacts and targets us all. Cyber Security Hypothetical will be led and moderated by Mr Steve Wilson and panellists will include MAJGEN Marcus Thompson, Professor Michael Frater, Mr Alastair MacGibbon, Ms Kate Carruthers and Mr Justin Warren.
The rise of information warfare: in-conversation with Peter W. Singer
ASPI ICPC
This event for 29 October is SOLD OUT but you can watch a livestream on the ASPI facebook page - ASPI's International Cyber Policy Centre invites you to an in-conversation with Peter W. Singer and Danielle Cave to consider the rise of information warfare. Peter Warren Singer is strategist and senior fellow at New America. He has been named by the Smithsonian as one of the nation’s 100 leading innovators, by Defense News as one of the 100 most influential people in defense issues, by Foreign Policy to their Top 100 Global Thinkers List, and as an official “Mad Scientist” for the U.S. Army’s Training and Doctrine Command. A drinks and canapes reception will conclude the event. This event is kindly supported by Microsoft.

