NEW REPORT: Winning Hearts and Likes I Twitter hides Donald Trump tweet I Downing Street plans new 5G club of democracies

Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
The Australian Government is urged to use social media far more strategically to engage international audiences. While the Department of Foreign Affairs and Trade (DFAT) and the Department of Defence both use social media - including accounts managed by diplomatic posts overseas and by units of the Australian Defence Force, both departments can improve how they reach and engage online. ASPI
Twitter has hidden one of Donald Trump’s tweets behind a warning that it “glorifies violence”, further escalating the social media company’s row with the US president. The Guardian
Britain is seeking to forge an alliance of ten democracies to create alternative suppliers of 5G equipment and other technologies to avoid relying on China. The government has approached Washington about a “D10” club of democratic partners, based on the G7 plus Australia, South Korea and India. The Times
ASPI ICPC
Winning Hearts and Likes: How foreign affairs and defence agencies use Facebook
ASPI ICPC
@dspray
While the Department of Foreign Affairs and Trade (DFAT) and the Department of Defence both use social media, including accounts managed by diplomatic posts overseas and by units of the ADF, both departments can improve how they reach and engage online. The Australian Government should use social media far more strategically to engage international audiences—particularly in the diplomatic and defence portfolios. Both DFAT and Defence should review outdated digital strategies, cross-promote more content and demonstrate transparency and accountability by articulating and publishing social media policies.
Read Dr Spry’s accompanying Strategist piece Winning hearts and likes: Foreign affairs, defence and Facebook.
Forced labour and supply chain risk: What companies need to know
Reuters
In March 2020, Australian Strategic Policy Institute published a detailed report documenting the use of Uyghurs forced labour in the Xinjiang region of China (see above for pending U.S. legislation). This report is drawing the attention of lawmakers and customs agencies globally from an enforcement standpoint. Numerous large global companies were named in the document.
Read more about forced labour and supply chain risk in ASPI’s Uyghurs for sale: ‘Re-education’, forced labour and surveillance beyond Xinjiang report.


Revealed: the worrying links between Huawei, our universities and China
The Telegraph
@CitySamuel @kerushton
The Telegraph can disclose today that the controversial Chinese telecoms giant backed 17 scientific papers with UK universities, about cutting-edge “dual-use” technologies – which can have civilian applications but can also be used in military technology. At least 15 of the papers focused on technology that experts claim could be used to communicate with swarms of drones or on highly advanced image recognition software that experts claim could be used for extreme levels of surveillance. All of them involve collaborations between British universities, including at Edinburgh and Exeter, and Chinese universities heavily involved in military research and named as "high risk" by an Australian think tank. Alex Joske, a China expert at the think tank - the Australian Strategic Policy Institute - said: “Chinese military universities are collaborating with western institutions to take advantage of their expertise, resources and training in order to advance China’s military technology.” All of the papers were backed by Huawei in some way – half through direct funding, and nearly all by Huawei researchers working on them. Five of the 18 papers were joint projects with China’s National University of Defence Technology – the in-house university of the People’s Liberation Army.
Read more about the implications of China’s military-civil fusion and research collaborations with western universities in ASPI’s China Defence Universities Tracker report.

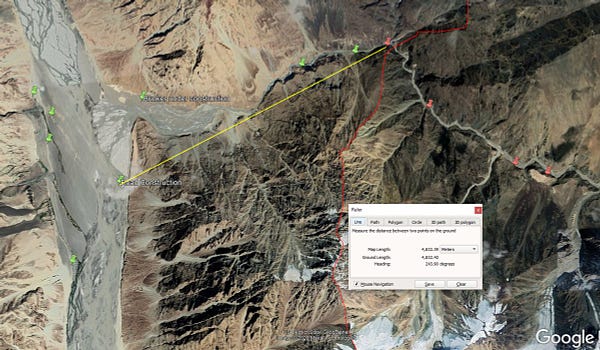
India-China border row will be resolved through diplomacy, says Rajnath Singh
The Hindu
Images dated May 22, put out by an analyst with the Australian Strategic Policy Institute, an independent think tank based in Canberra, show about 80 tents set up by Chinese soldiers along the Galwan river. They also show vehicles and other structures.


Australia
More convicted terrorists due for release over next five years, ASIO warns
Sydney Morning Herald
@Gallo_Ways
Without naming any specific country, ASIO warned foreign spies were operating "at a scale, breadth and ambition that has not previously been seen in Australia". China has previously been blamed by security agencies for large-scale hacking in Australia, while ASIO has investigated a suspected Chinese military intelligence operative in Melbourne who allegedly approached a Liberal Party member about running for parliament..Foreign intelligence services continue to seek access to privileged and classified information. Australia’s research and development of innovative technologies and its military modernisation program are attractive targets for espionage by foreign states seeking to gain an advantage to the detriment of Australia's security and prosperity."

China
What China’s Tighter Control of Hong Kong Means for Tech
The Information
@beijingscribe @waynema
China’s move to curtail Hong Kong’s autonomy threatens Hong Kong’s status as a business hub—and could have major implications for the tech industry, particularly the cryptocurrency sector, cloud services and tech financing. At the extreme, venture capitalists and tech companies could shift their operations and regional headquarters to Singapore, which has already been courting more foreign investment. Even before that happens, the Chinese moves may dampen the flow of venture capital money out of the U.S. to Hong Kong, which is the conduit for U.S. funds to invest in Chinese tech. The new national security rules could also slow the growth of U.S. firms such as Amazon and Google, which have recently started to offer cloud-computing services in Hong Kong.
Twitter applies fact check to China spokesman’s tweets about virus origins
Fortune
@dwallbank
Twitter has applied a fact check tag to at least two posts by China Foreign Ministry Spokesman Zhao Lijian, both of which advanced questions about whether the COVID-19 virus began in the U.S. rather than China.


Do My Tweets Really Threaten China’s National Security?
The New York Times
@JimmyLaiApple
I joined Twitter recently, and started posting messages about the new law last weekend, just after the Chinese Communist Party first mentioned it. Within a day, an article in the official Communist Party mouthpiece Global Times, citing experts, called my tweets “evidence of subversion” under the proposed national security law — this, even before the National People’s Congress formally endorsed the legislation on Thursday.
China rounds up Wuhan’s citizen journalists for ‘provoking quarrels’
Financial Times
@donweinland
In her last report posted to YouTube on May 13, citizen journalist Zhang Zhan stood outside a train station in Wuhan and described conditions in the city where the coronavirus pandemic began.
USA
Inside Twitter’s Decision to Take Action on Trump’s Tweets
Wall Street Journal
@georgia_wells
When Twitter Inc. earlier this month announced a new fact-checking tool, it was billed largely as a measure to combat false information about coronavirus. Two weeks later, the company deployed that tool in one of the biggest actions in its history: squaring off with President Trump.
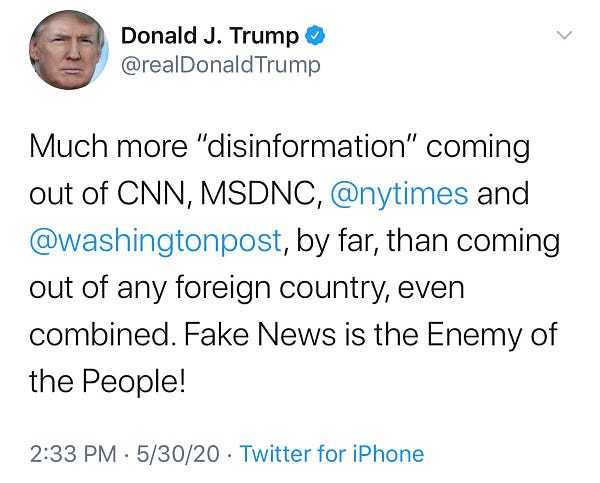
Twitter hides Donald Trump tweet for 'glorifying violence'
The Guardian
@alexhern
Twitter has hidden one of Donald Trump’s tweets behind a warning that it “glorifies violence”, further escalating the social media company’s row with the US president.
Mark Zuckerberg says 'divisive' Trump posts about George Floyd protest will remain on Facebook
The Telegraph
@MargiMurphy
Mark Zuckerberg said that Facebook will not take action on posts published by Donald Trump about the George Floyd protests, including one in which the president warned that, “when the looting starts, the shooting starts”. Zuckerberg says he 'disagrees strongly' with Trump's post but will not remove it from his social network.
Leaked posts show Facebook employees asking the company to remove Trump’s threat of violence
The Verge
@CaseyNewton
Facebook’s decision not to take action against recent posts about mail-in ballots and the Minnesota protests by President Trump is roiling employees, some of whom are calling on executives to reconsider their stance. In response to an internal post explaining the company’s rationale, some employees criticized the company’s neutral posture.
We’re Keeping A Running List Of Hoaxes And Misleading Posts About The Nationwide Police Brutality Protests
BuzzFeed News
@JaneLytv @CraigSilverman
The death of George Floyd, an unarmed black man who died after a Minneapolis police officer who used a knee chokehold on him, has sparked protests all over the country. As they gained traction, so did online hoaxes and disinformation about them. BuzzFeed News is keeping a running list of false and misleading information.

US joins G7 artificial intelligence group to counter China
Defense News
@mattoyeah
The U.S. has joined an international panel for setting ethical guidelines for the use of artificial intelligence, a move previously dismissed by the Trump administration. The White House’s chief technology officer, Michael Kratsios, told The Associated Press on Thursday it is important to establish shared democratic principles as a counter to China’s record of “twisting technology” in ways that threaten civil liberties.

Customs and Border Protection Is Flying a Predator Drone Over Minneapolis
Vice
@jason_koebler @josephfcox @neuwaves
Customs and Border Protection (CBP) is flying a Predator drone, military technology used for surveilling and killing terrorists abroad, over Minneapolis as protesters continue to demonstrate against police brutality, according to publicly available flight data. The drone flown over Minneapolis is an unarmed version of the aircraft.

Semiconductor Industry to Lobby for Billions to Boost U.S. Manufacturing
Wall Street Journal
@bobdavis187 @asafitch @Kate_OKeeffe
The American semiconductor industry is gearing up for a lobbying push to obtain billions of dollars in federal funding for factory building and research to keep the U.S. ahead of China and other countries that heavily subsidize their chip industries.
Southeast Asia
Fortune 500 company NTT discloses security breach
ZDNet
@campuscodi
Nippon Telegraph & Telephone (NTT), the 64th biggest company in the world, according to the Fortune 500 list, has disclosed today a security breach. NTT says hackers gained access to its internal network and stole information on 621 customers from its communications subsidiary, NTT Communications, the largest telecommunications company in Japan, and one of the biggest worldwide.
NZ & Pacific Islands
Fears in Papua New Guinea over reports of China Mobile buying major phone carrier Digicel
The Guardian
The Digicel conglomerate surprised many of its users in PNG by filing bankruptcy proceedings earlier this month in Bermuda and the US, where it owes billions of dollars. But, for the 3.8 million Digicel users in Papua New Guinea there could be vast changes in the near future if the speculation that China Mobile will bid to buy Digicel Pacific’s assets is correct.
South & Central Asia
The Ladakh lesson: India must guard against Chinese tech intrusion
ORF
The recent border standoff between China and India at Ladakh confirms two political realities that must not be ignored. First, India must not allow the intrusion of Chinese firms into its telecommunications network. If societies will be digital, China should not be permitted to encode India’s public sphere. New Delhi must not license Huawei or ZTE to provide equipment for its 5G rollout. And second, India must not allow any Chinese-origin firm into its critical infrastructure in much the same manner that it was kept away from certain industrial projects in the past.
UK
Downing Street plans new 5G club of democracies
The Times
@LOS_Fisher
Britain is seeking to forge an alliance of ten democracies to create alternative suppliers of 5G equipment and other technologies to avoid relying on China. The government has approached Washington about a “D10” club of democratic partners, based on the G7 plus Australia, South Korea and India.
British tech firms could get state help to rival Huawei
The Times
@LOS_Fisher
Boris Johnson is examining options to boost state investment into domestic telecoms companies to help them compete in the 5G technology market, The Times understands. The proposal is part of a wider plan to reduce Britain’s reliance on Huawei for its next-generation mobile network, amid growing security fears over the Chinese firm’s equipment.
Europe
Berlin seeks sanctions against Russian hackers over Bundestag cyberattack
Politico
@vonderburchard @laurenscerulus
Germany’s foreign ministry on Thursday summoned the Russian ambassador over a 2015 cyberattack on the German parliament, saying that Berlin would press for sanctions against those responsible for the hack. The move came about two weeks after Chancellor Angela Merkel told parliamentarians that she had “hard evidence” that Russia was responsible for an “outrageous” cyberattack on the Bundestag in the spring of 2015, which reportedly caused the theft of more than 16 gigabytes of data, including confidential emails from lawmakers.
Middle East
Israel-Iran attacks: “Cyber winter is coming”
Financial Times
@MehulAtLarge
In early April, municipal workers at a water pumping station in central Israel noticed a warning from their computer systems. A piece of Iranian-written code had travelled around the world, passing through servers in the US and Europe to hide its origins, and finally to the commercially manufactured software controllers that operated the water pumps, according to four Israeli officials and a western intelligence official briefed on the findings.
Misc
Exclusive: Zoom plans to roll out strong encryption for paying customers
Reuters
Video conferencing provider Zoom plans to strengthen encryption of video calls hosted by paying clients and institutions such as schools, but not by users of its free consumer accounts, a company official said on Friday.
Microsoft sacks journalists to replace them with robots
The Guardian
@jimwaterson
Dozens of journalists have been sacked after Microsoft decided to replace them with artificial intelligence software. Staff who maintain the news homepages on Microsoft’s MSN website and its Edge browser—used by millions of Britons every day—have been told that they will be no longer be required because robots can now do their jobs.
Facebook to Verify the ID of Suspiciously Popular Accounts
PCMag
@mthwgeek
Facebook is set to introduce another way of ensuring the information we consume on the social network isn't misleading. If a 'pattern of inauthentic behavior' is detected for an account with a large audience in the US, Facebook will trigger a verification process.
This Bot Hunts Software Bugs for the Pentagon
WIRED
@tsimonite
Last month, the Pentagon awarded ForAllSecure a $45 million contract to widen use of Mayhem across the US military. The department has plenty of bugs to find. A 2018 government report found that nearly all weapons systems the Department of Defense tested between 2012 and 2017 had serious software vulnerabilities.
Google Chrome is getting a new feature that blocks misleading and intrusive website notifications
Business Insider Australia
@LisaEadicicco
Google is cracking down on websites that abuse notification privileges in Chrome. The search giant said it will automatically block misleading and abusive notifications in Chrome and issue a warning to users when a website may be attempting to trick them into allowing alerts. The update will be coming in an upcoming version of Chrome that will be released in July.
UN Security Council meeting highlights the cyber peace and security challenges wrought by the COVID-19 pandemic
Reaching Critical Will
@a_pytlak
The United Nations Security Council (UNSC) held its second ever Arria-formula meeting to discuss “cyber stability, conflict prevention, and capacity building” on Friday, 22 May. Taking place under the presidency of Estonia, the nearly five-hour long, entirely online session demonstrated that this is a topic of increasing priority and importance for many UN member states and also showed how UN-based discussions on this topic have evolved since the Council’s first meeting on the subject in 2016.
Grants
Fact-Checking Development Grant Program - Poynter
Poynter
The International Fact-Checking Network (IFCN) is dedicated to furthering innovation and establishing best practices in the field. Thanks to support from YouTube via the Google News Initiative, the IFCN has $1 million in grant funding available for established fact-checking units that are pursuing projects around video production, tools development, audience building, and new formats testing. Fact-checking units can apply for up to $50,000 each.
Events