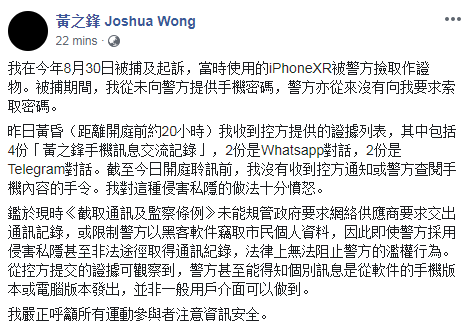
NYT exposé on smartphone location tracking / Chinese hacking group resumes global attacks / Israeli spyware allegedly used to target Pakistani officials' phones


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
This is our final Cyber Digest for 2019. Thanks for reading! We will be back with the latest cyber news on 8 January 2020.
The NYT has obtained a file containing more than 50 billion location pings from the phones of more than 12 million Americans as they moved through several major cities, including Washington, New York, San Francisco and Los Angeles. The New York Times
A Chinese government-linked hacking group that was thought to be dormant has been quietly targeting companies and government agencies for the last two years, harvesting data after stealing passwords and circumventing two-factor authentication intended to prevent such attacks, according to researchers. Bloomberg
The mobile phones of at least two dozen Pakistani government officials were allegedly targeted earlier this year with technology owned by the Israeli spyware company NSO Group, the Guardian has learned. The Guardian
The World
Google goes offline after fibre cables cut
BBC News
Severed fibre optic cables disrupted internet access in parts of eastern Europe, Iran and Turkey on Thursday. The issue, which lasted for about two hours, was caused by multiple fibre cables being physically cut at the same time, a highly unusual thing to happen.
Year in Review: Content Moderation on Social Media Platforms in 2019
Council on Foreign Relations
The spread of disinformation, misinformation, hate speech, and violent and extremist content on social media platforms in 2019 prompted heated debate over how tech companies and governments should approach content moderation. These issues will continue to play out in 2020, with important social and political consequences.
Australia
Canberra forecast 5,400 small business cyber health checks, but only 35 happened
ZD Net
@dobes
Despite the federal government expecting over 5,000 cyber health checks of Australian small businesses, only 35 have happened so far.
Huawei wins Brisbane railway signals contract
The Australian
@bennpackham
Brisbane’s Cross River Rail Authority has contracted Huawei to deliver its new digital signalling system, entrusting the safety of passengers to the Chinese company considered a “high-risk vendor” by the federal government.
China
Chinese Hacking Group, Quiet for Years, Resumes Global Attacks
Bloomberg
@rj_gallagher
A Chinese government-linked hacking group that was thought to be dormant has been quietly targeting companies and government agencies for the last two years, harvesting data after stealing passwords and circumventing two-factor authentication intended to prevent such attacks, according to researchers. Fox-IT, a security company based in the Netherlands, said in a report published Thursday that the group’s attacks have extended to 10 countries, including the U.S., the U.K., France, Germany and Italy. The Chinese hackers carried out a global espionage campaign that targeted industries including aviation, construction, finance, health care, insurance, gambling and energy, the firm said.

USA
Twelve Million Phones, One Dataset, Zero Privacy
NYT
One Nation, Tracked: an investigation into the smartphone tracking industry. The data reviewed by Times Opinion didn’t come from a telecom or giant tech company, nor did it come from a governmental surveillance operation. It originated from a location data company, one of dozens quietly collecting precise movements using software slipped onto mobile phone apps. You’ve probably never heard of most of the companies — and yet to anyone who has access to this data, your life is an open book.

A Data Leak Exposed The Personal Information Of Over 3,000 Ring Users
BuzzFeed News
@carolineha_
“This gives a potential attacker access to view cameras in somebody’s home — that’s a real serious potential invasion of privacy right there.”
The Pentagon's AI Chief Prepares for Battle
WIRED
@EliasGroll
Lt. Gen. Jack Shanahan doesn't want killer robots—but he does want artificial intelligence to occupy a central role in warfighting.
Does the Defense Department’s New Approach to Industrial Base Cybersecurity Create More Problems Than It Solves?
CSIS
@morgan_dwyer1
Malicious cyber actors increasingly target the defense industrial base for both economic and security gains. For example, in 2018, the Chinese government hacked a U.S. defense contractor and stole 614 gigabytes of sensitive material from the Navy’s Sea Dragon program. The Department of Defense (DOD) has since acknowledged that industrial base cybersecurity is insufficient and has suggested a new approach—the Cybersecurity Maturity Model Certification (CMMC)—to address future cyber threats. However, in its present instantiation, CMMC may create more problems than it solves.
Facebook separates security tool from friend suggestions, citing privacy overhaul
Reuters
@katielpaul
Facebook Inc will no longer feed user phone numbers provided to it for two-factor authentication into its “people you may know” feature, as part of a wide-ranging overhaul of its privacy practices, the company told Reuters.
Facebook will bar posts, ads that spread disinformation about the U.S. Census The Washington Post
Federal study confirms racial bias of many facial-recognition systems, casts doubt on their expanding use
The Washington Post
Facial-recognition systems misidentified people of color more often than white people, a landmark federal study released Thursday shows, casting new doubts on a rapidly expanding investigative technique widely used by law enforcement across the United States.
South & Central Asia
Why India is the world leader of internet shutdowns
BBC
@shadabnazmi
As protests over a controversial citizenship law rage across India, authorities resorted to shutting down the internet in cities where demonstrators flooded the streets. It was one more episode of a shutdown in a country which has seen the highest number of internet blocks in the world so far this year.
Middle East
Israeli spyware allegedly used to target Pakistani officials' phones
The Guardian
@skirchy
The mobile phones of at least two dozen Pakistani government officials were allegedly targeted earlier this year with technology owned by the Israeli spyware company NSO Group, the Guardian has learned.
Misc
Researchers bypass airport and payment facial recognition systems using masks
Endgadget
@georginatorbet
To perform the test, artificial intelligence company Kneron commissioned high-quality 3D masks that mimicked the face of another person, and tested whether someone could wear one to fool facial recognition systems. Researchers were able to make purchases from another person's account via the AliPay and WeChat payment systems.

