Rachel Noble to become first woman to lead a major Australian spy agency | New Orleans declares state of emergency following cyber attack | Who spied on Indians–WhatsApp, NSO,or the government?


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference
The Federal Government has appointed the first woman to lead a major Australian spy agency. Rachel Noble will become the next director-general of the Australian Signals Directorate (ASD), which intercepts electronic communications from foreign countries. She is currently the head of the Australian Cyber Security Centre (ACSC). ABC
The City of New Orleans has suffered a cybersecurity attack serious enough for Mayor LaToya Cantrell to declare a state of emergency. Forbes
As the mystery around who hired the NSO Group, the Israeli surveillance company, for allegedly spying on Indian journalists and activists deepens, the government is blaming WhatsApp, which is pointing fingers at NSO. The Pegasus creator maintains it only sells its spywares to governments. ET Prime
ASPI ICPC
Policy, Guns & Money: The APSI Podcast
ASPI
ASPI ICPC’s Mali interviews Oriana Skylar Mastro, Assistant Professor of Security Studies at the Edmund A. Walsh School of Foreign Service at Georgetown University and Resident Scholar at the American Enterprise Institute, about her most recent book ‘The Costs of Conversation: Obstacles to Peace Talks in Wartime (Cornell University Press 2019)’ and her latest project on China’s challenge to U.S primacy. ICPC’s Louisa spoke with Dion Devow, Indigenous engagement specialist working with ICPC and 2018 ACT Australian of the Year, on closing the information technology gap for Indigenous Australians Plus ICPC’s Jake interviewed Vijay Padmanabhan, Google’s Lead for Countering Violent Extremism & Hate Speech.
These Australians say they have proof Turkey is exaggerating its successes in Syria
ABC
@JamesEltonPym
In an unassuming office in Canberra, 22-year-old Nathan Ruser — an open-source intelligence analyst with the Australian Strategic Policy Institute (ASPI) — is scanning the Turkish broadcaster Anadolu Agency's triumphant tank video for identifying landmarks. His eyes light up as he spots a mosque in the background — one of the "most useful" tools for geolocating in the Middle East, he says.. Verifying a single video can take hours. Dead ends are common and sometimes permanent. Even if you prove something, there's no guarantee anyone will listen. Or care. Mr Ruser says it is worth it. The truth matters on its own, he says, but there can be practical outcomes too. Elise Thomas, 28, is another open-source cyber researcher with ASPI who has turned her attention to decoding misinformation campaigns on social media.
The World
China’s African envoys take Twitter tips from Trump in PR offensive
South China Morning Post
Jevans Nyabiage
Chinese diplomats in Africa are robustly defending Beijing’s policies on Twitter as part of a new and sometimes aggressive public relations campaign which is playing out across the globe as the country’s envoys answer President Xi Jinping’s call to “tell China stories well”.
US-China tech war’s new battleground: undersea internet cables
The South China Morning Post
Meaghan Tobin
In the contest between the US and China for dominance over the world’s technology infrastructure, the latest battle is taking place under the Pacific Ocean.
Joint EU-US statement following the EU-US Justice and Home Affairs Ministerial Meeting
European Council
On 11 December 2019, the EU-U.S. Ministerial Meeting on Justice and Home Affairs took place in Washington D.C.. We also acknowledged that the use of warrant-proof encryption by terrorists and other criminals – including those who engage in on-line child sexual exploitation – compromises the ability of law enforcement agencies to protect victims and the public at large. At the same time, encryption is an important technical measure to ensure cybersecurity and the exercise of fundamental rights, including privacy, which requires that any access to encrypted data be via legal procedures that protect privacy and security. Within this framework, we discussed the critical importance of working towards ensuring lawful access for law enforcement authorities to digital evidence, including when encrypted or hosted on servers located in another jurisdiction.
Rivals
BBC iPlayer
We look at social media innovation coming out of China, and how that’s making Silicon Valley nervous. Are the global power-dynamics of the internet changing?
Australia
Rachel Noble to become the first woman to lead a major Australian spy agency
ABC
The Federal Government has appointed the first woman to lead a major Australian spy agency.Rachel Noble will become the next director-general of the Australian Signals Directorate (ASD), which intercepts electronic communications from foreign countries. She is currently the head of the Australian Cyber Security Centre (ACSC).
Read the ASD announcement


China
AP Exclusive: China tightens up on info after Xinjiang leaks
AP
The Xinjiang regional government in China’s far west is deleting data, destroying documents, tightening controls on information and has held high-level meetings in response to leaks of classified papers on its mass detention camps for Uighurs and other predominantly Muslim minorities, according to four people in contact with government employees there.
Beijing’s patriotic PC shift spells trouble for foreign tech groups
Financial Times
@yuanfenyang and Patrick Mathurin
The new directive, nicknamed “3-5-2”, aims to increase China’s reliance on homemade technology and could deal a blow to foreign technology groups such as HP, Dell Technologies and Microsoft. “3-5-2” seeks to replace up to 20m pieces of hardware at a rate of 30 per cent in 2020, 50 per cent the following year and the remaining 20 per cent in 2022. The mandate is part of China’s longer-term push for “secure and controllable” technology in government and critical industries as part of its Cyber Security Law, which should boost domestic PC makers such as Lenovo, Huawei and Xiaomi.
Huawei critics in China inspired by Hong Kong protests
Financial Times
@suelinwong @QianerLiu
An online campaign against the alleged mistreatment of an ex-employee at Huawei in mainland China is drawing inspiration from the Hong Kong protests in a development that is likely to concern Beijing. After news of the alleged wrongful detention of a former employee of the telecoms equipment group went viral on social media in China last week, users published more than 20,000 posts drawing parallels between the Huawei situation and Hong Kong, Financial Times analysis showed. While China has a vibrant social media scene, the posts on Huawei represent the first sustained campaign in the country to draw on the Hong Kong protests.
China’s Grindr Strategy
Foreign Policy
@elisabethbraw
The hookup app isn’t the only tech company Chinese companies have tried to acquire. It’s part of a broader strategy of the country buying up cutting-edge Western firms.


US
New Orleans Declares State Of Emergency Following Cyber Attack
Forbes
The City of New Orleans has suffered a cybersecurity attack serious enough for Mayor LaToya Cantrell to declare a state of emergency.
FBI secretly demands a ton of consumer data from credit agencies. Now lawmakers want answers
TechCrunch
@zackwhittaker
Recently released documents revealed the FBI has for years secretly demanded vast amounts of Americans’ consumer and financial information from the largest U.S. credit agencies.
House panel asks Apple, Google if app makers must reveal foreign ties
Engadget
@jonfingas
The US is growing increasingly suspicious of foreign-made apps. House national security subcommittee chairman Rep. Stephen Lynch has sent letters to Apple and Google asking whether or not they require app developers to disclose "potential overseas affiliations" before software shows up in their respective stores. The congressman is worried about claims that apps like TikTok, Grindr and FaceApp may be providing sensitive data to the governments of China and Russia.
Prime Leverage: How Amazon Wields Power in the Technology World
The new York Times
@daiwaka
Software start-ups have a phrase for what Amazon is doing to them: ‘strip-mining’ them of their innovations.
Hacker harasses 8-year-old over bedroom security camera
The Sydney Morning Herald
@_allysonchiu
Several users of the Ring security cameras across the United States have reported that their security systems were also infiltrated by hackers who harassed them through the camera's two-way talk function. (Ring is an Amazon product. Amazon chief executive Jeff Bezos owns The Washington Post.)
US Military Needs Better Data On Itself To Exploit AI
Breaking Defense
Theresa Hitchens
While the US military has “tons of really good information on the adversary” that can be used to teach future AI systems about enemy targets, it actually lacks the necessary data about its own forces, says Col. Enrique Oti, head of the Air Force’s key software innovation hub Kessel Run. Until DoD gets that data on itself, he said, there’s a host of AI applications out of reach.
Facebook Will Call Some Media “State Controlled." Al Jazeera Says That’s “Dangerous.”
Buzz Feed News
Otillia Steadman and Alex Kantrowitz
Government-funded news organizations worried they could be damaged by Facebook’s imminent plan to label content from state-controlled news organizations are furious at a process they say is opaque and irresponsible.
North Asia
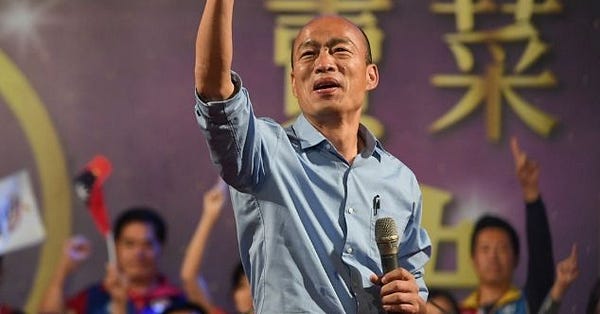
Taiwan Election: The Final Countdown
Stanford Internet Observatory
A few hours after we published this blog post, Facebook took down 118 fan pages, 99 groups, and 51 accounts for coordinated activity and rules violations. The story is developing , but as reported in the press the issue appears to have been behavior coordinated between groups to artificially inflate the popularity of content in certain communities, rather than foreign influence.

Southeast Asia
4 kinds of fake news in PHL, including state-sponsored trolling —NATO Stratcom study
GMA News Online
A study published by the North Atlantic Treaty Organization (NATO) detailed four models of disinformation in the Philippines, including a state-sponsored model that leads to the "silencing, self-censorship, and chilling effects among dissenters, and the public." The study, published by NATO Strategic Communications Center of Excellence, found four models of "fake news" factories.


The Pacific


South Asia
Who is spying on Indians? WhatsApp, Pegasus spyware maker, the government are caught in a blame game
ET Prime
@SandhyaETprime
As the mystery around who hired the NSO Group, the Israeli surveillance company, for allegedly spying on Indian journalists and activists deepens, the government is blaming WhatsApp, which is pointing fingers at NSO. The Pegasus creator maintains it only sells its spywares to governments.
What is non-personal data and why India is trying to regulate it
Quartz
Sreenidhi Srinivasan
Should enterprises share data that is anonymised and masked?
UK
Five lessons from the 'social media' election
BBC
@amolrajanon Twitter
There is still a vast amount we simply don't know about how the election campaign played out digitally. This includes how much was spent by the main parties on targeted Facebook ads in the final few days; how much was spent advertising on other platforms; and whether foreign actors were behind any of the most controversial activity.
How the Tories won the online election: pick a line, ignore the facts and repeat
The Guardian
Alex Hern
We didn’t need Russian bots to spread misinformation: real people retweeting false claims did enough damage.
Europe
China Threatens Retaliation Should Germany Ban Huawei 5G
Bloomberg
@Tony Czuczka @Steven Arons
China’s ambassador to Germany threatened Berlin with retaliation if it excludes Huawei Technologies Co. as a supplier of 5G wireless equipment, citing the millions of vehicles German carmakers sell in China. “If Germany were to take a decision that leads to Huawei’s exclusion from the German market, there will be consequences,” Ambassador Wu Ken said Saturday at a Handelsblatt event. “The Chinese government will not stand idly by.”

Lingering Infektion: Latvian operation mimicked Secondary Infektion tactics
Medium
@DFRLab
The DFRLab has uncovered an influence operation using forged documents and a network of fake online accounts to undermine the credibility of the Latvian government. Similar to an operation identified by the lab in June, the effort carries the hallmarks of Russian intelligence services, though no link between the two operations was apparent.
Norway's Telenor picks Ericsson for 5G, abandoning Huawei
Reuters
Victoria Klesty and Terje Solsvik
Telenor has picked Sweden’s Ericsson as the key technology provider for its fifth-generation (5G) telecoms network in Norway, it said on Friday, gradually removing China’s Huawei [HWT.UL] after a decade of collaboration over 4G.
Cabinet warned of rising threat to Ireland from foreign spies
The Irish Times
@Martin Wall
Spying by overseas intelligence services in Ireland is a growing threat to national security as well as to foreign direct investment and overall economic development, the Government has been warned. A new defence policy review, given to Ministers this week, says threats from both espionage and cyber attacks are increasing since the White Paper on Defence was published in 2015.
Canada
How these Toronto sleuths are exposing the world’s digital spies while risking their own lives
The Star
@scontenta
Since Ron Deibert founded the University of Toronto lab in 2001, his team of cybersecurity watchdogs have reverse-engineered their way to the forefront of a battle against digital espionage — a growing, unregulated industry of private corporations selling spying software to authoritarian regimes. “It’s an epidemic,” Deibert says. “What we’re seeing is a proliferation globally of this technology being used — implicated in murder, implicated in all sorts of blackmail — and helping to empower some of the world’s most corrupt rulers and autocrats.
Middle East
Iran 'foils second cyber-attack in a week'
BBC
Iran has foiled a second cyber-attack in less than a week, the country's telecommunications minister says. Mohammad Javad Azari-Jahromi announced on Twitter that the cyber-attack had targeted Iranian electronic government systems.
Research
A Storm of Tweets: Social Media Manipulation During the Gulf Crisis
Review of Middle East Studies
@AndrewMLeber @abulkhaezuran
Social media platforms like Facebook and Twitter were heralded circa 2009–2011 as ‘liberation technology’ that would facilitate mass mobilization against Middle Eastern authoritarians. In this article, however, we present evidence from the ongoing Gulf Crisis (2017-present) that regimes can now exploit Twitter as an outlet for political propaganda.
Emotion recognition technology should be banned, says an AI research institute
MIT Technology Review
There’s little scientific basis to emotion recognition technology, so it should be banned from use in decisions that affect people’s lives, says research institute AI Now in its annual report.

