Russian cyberattack unit ‘masqueraded’ as Iranian hackers, UK says | Facebook finds new disinformation campaigns and braces for 2020 torrent | Islamic State Turns to Teen-Friendly TikTok


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
A Russian cyber espionage unit has hacked Iranian hackers to lead attacks in more than 35 countries, a joint UK and US investigation has revealed. The so-called Turla group, which has been linked with Russian intelligence, allegedly hijacked the tools of Oilrig, a group widely linked to the Iranian government, according to a two-year probe by the UK’s National Cyber Security Centre in collaboration with the US’ National Security Agency. Financial Times
Facebook on Monday said it had found and taken down four state-backed disinformation campaigns, the latest of dozens the company has identified and removed this year. Three of the campaigns originated in Iran, and one in Russia, Facebook said, with state-backed actors disguised as genuine users. Their posts targeted people in North Africa, Latin America and the United States, the company said. New York Times
Islamic State militants have been posting short propaganda videos to TikTok, the social network known for lighthearted content popular with teenagers. The videos—since removed, in line with the app’s policy—featured corpses paraded through streets, Islamic State fighters with guns, and women who call themselves “jihadist and proud.” Many were set to Islamic State songs. Some included TikTok filters, or images, of stars and hearts that stream across the screen in an apparent attempt to resonate with young people. Wall Street Journal
ASPI ICPC
Engineering global consent: the Chinese Communist Party’s data-driven power expansion
ASPI ICPC
@He_Shumei

The Chinese party-state engages in data collection on a massive scale as a means of generating information to enhance state security—and, crucially, the political security of the Chinese Communist Party (CCP)—across multiple domains. The party-state intends to shape, manage and control its global operating environment so that public sentiment is favourable to its own interests. This report explains how the party-state’s tech-enhanced authoritarianism is expanding globally. The effort doesn’t always involve distinctly coercive and overtly invasive technology, such as surveillance cameras. In fact, it often relies on technologies that provide useful services.
Read Dr Samantha Hoffman’s accompanying article in The Strategist: Engineering global consent: the Chinese Communist Party’s data-driven power expansion
China’s tech rise poses security and human rights dilemma for Australian universities
South China Morning Post
John Power
When the University of Technology Sydney launched its joint research centre with Chinese tech giant CETC in 2017, the university promised the partnership would boost Australia’s prowess in emerging technologies such as artificial intelligence, big data and quantum computing. But only halfway into the five-year, US$20 million partnership, the Australia-China Research Innovation Centre in Information and Electronics Technologies is not attracting attention for the “innovative solutions” or positive “societal impacts”..instead, the partnership is at the centre of a growing debate about how Australian universities should balance much-needed international collaboration in promising fields with mounting concerns that such research could undermine the country’s national security and be used in ways that go against national values, including to boost Beijing’s authoritarian policies. Alex Joske, an ASPI researcher who specialises in unwinding ties between Australian institutions and Chinese entities, said that “by agreeing to train and host CETC staff, UTS has committed itself to raising the ability of China’s defence industry”.
Should you be worried about Tik Tok?
ABC
@olgordon
Tik Tok is the first Chinese social media app to crack the western market and some are concerned Beijing will lean on the platform's creators to exert foreign influence. Featuring Fergus Ryan from the Australian Strategic Policy Institute.
NATO Strategic Communications Centre of Excellence’s shared ASPI ICPC’s Mapping China’s Tech Giants:

The World
Russian cyberattack unit ‘masqueraded’ as Iranian hackers, UK says
Financial Times
@helenwarrell @HenryJFoy
A Russian cyber espionage unit has hacked Iranian hackers to lead attacks in more than 35 countries, a joint UK and US investigation has revealed. The so-called Turla group, which has been linked with Russian intelligence, allegedly hijacked the tools of Oilrig, a group widely linked to the Iranian government, according to a two-year probe by the UK’s National Cyber Security Centre in collaboration with the US’ National Security Agency. The NCSC is part of GCHQ, the digital intelligence agency.
Facebook Finds New Disinformation Campaigns and Braces for 2020 Torrent
New York Times
@MikeIsaac
Facebook on Monday said it had found and taken down four state-backed disinformation campaigns, the latest of dozens the company has identified and removed this year. Three of the campaigns originated in Iran, and one in Russia, Facebook said, with state-backed actors disguised as genuine users. Their posts targeted people in North Africa, Latin America and the United States, the company said.
Read the announcement from Facebook here.
Read about how Facebook aims to Protect the 2020 US Elections here.
Read Facebook’s new policy update on responding to inauthentic behaviour.
Ahead of the 2020 elections in the US, Facebook are launching a new program, called Facebook Protect, to further secure candidates, campaign staff, and others who may be frequent targets of hackers and foreign adversaries. Read the details.
Graphicka analysed the Russian operation: The IRACopyPasta Campaign
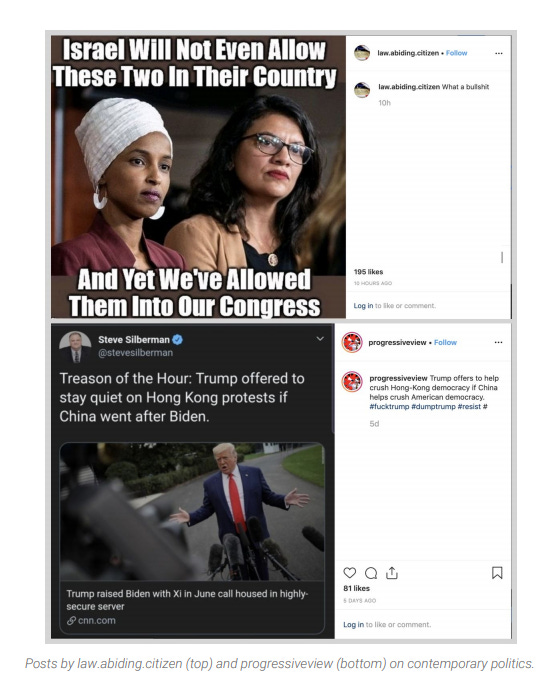
A screenshot from the Graphika report showing the practice of targeting both sides on divisive issues, a tactic characteristic of the campaigns initially conducted by the IRA to target American audiences in 2014-2018.
Australia
This simple game shows why metadata laws won't protect whistleblowers
The Guardian
@NickEvershed
Australia has passed data retention laws that force telecommunications companies to retain some types of phone and web metadata. This data can be requested by government agencies and has been used to investigate leaks of government information to journalists. It now takes a warrant to access a journalist’s metadata to identify a source, but this offers limited protection. Government agencies can still seek data from suspected sources without a warrant. This game shows how a whistleblower can still be identified.
China
Apple CEO Tim Cook joins influential Beijing university board as company’s China woes continue
South China Morning Post
@FrankTangTweets
Apple CEO Tim Cook has been appointed chairman of the advisory board at Tsinghua University School of Economics and Management in Beijing, a role that could provide access to top Chinese leaders at a time the iPhone manufacturer is facing mounting challenges in the world’s second largest economy.
China’s Surveillance State Has Tens of Millions of New Targets
Foreign Policy
@emiledirks Sarah Cook
So-called key individuals, from drug addicts to religious believers, are singled out in police databases.
US
Mark Zuckerberg Has Quietly Recommended Campaign Hires to Pete Buttigieg
Bloomberg
@tylerpager Kurt Wagner
Facebook Inc. chief executive officer Mark Zuckerberg has privately recommended several potential hires to Pete Buttigieg’s presidential campaign, a rare example of direct political involvement from one of tech’s most powerful executives.
Open database leaked 179GB in customer, US government, and military records
ZD Net
@SecurityCharlie
An open database exposing records containing the sensitive data of hotel customers as well as US military personnel and officials has been disclosed by researchers. On Monday, vpnMentor's cybersecurity team, led by Noam Rotem and Ran Locar, said the database belonged to Autoclerk, a service owned by Best Western Hotels and Resorts group.
Private Photos of Indicted Donor Depict Ties to Trump, Giuliani
WSJ
Dating back to 2015, the private Instagram account of Lev Parnas, a Ukrainian-American indicted for illegal campaign donations, appears to show VIP access to President Trump and a close relationship with Rudy Giuliani.
This Sure Looks Like Mitt Romney’s Secret Twitter Account (Update: It Is)
Slate
@ashleyfeinberg
Earlier today, the Atlantic’s McKay Coppins published a lengthy profile on Mitt Romney, apparently part of Romney’s effort to set himself up as the noble Republican foil to an out-of-control president. These sorts of pieces, which are more about narrative setting than anything else, typically don’t contain a lot of new information, but this had one notable exception. About midway through, the usually guarded senator revealed that, just like fellow lone-voice-of reason-haver James Comey, he was the owner of a secret Twitter account.
Facebook looks to improve child protection over fears encryption will raise risks
Financial Times
@madhumita29
Facebook has revealed a two-year project to work out how to prevent minors from being groomed and exploited on its platforms after it introduces encryption, as politicians in the US, UK and Australia warned that the move threatens the safety of children.
Microsoft banks on new silicon chips built by Intel, others to fend off firmware attacks
Cyber scoop
@jeffstone500
Microsoft is pushing an initiative meant to protect its computers’ most sensitive data amid recent revelations that nation-state hackers are beginning to exploit the fragmented nature of the company’s supply chain.
Facebook Wants to Know the Apps You Download and Delete
Adweek
@swodinsky
Whether you’re deleting an app that’s buggy, draining your battery or taking up too much precious phone space, Facebook wants to know.
Middle East
Islamic State Turns to Teen-Friendly TikTok, Adorning Posts With Pink Hearts
The Wall Sreet Journal
@georgia_wells
Islamic State militants have been posting short propaganda videos to TikTok, the social network known for lighthearted content popular with teenagers. The videos—since removed, in line with the app’s policy—featured corpses paraded through streets, Islamic State fighters with guns, and women who call themselves “jihadist and proud.” Many were set to Islamic State songs. Some included TikTok filters, or images, of stars and hearts that stream across the screen in an apparent attempt to resonate with young people.
The clock’s ticking for regulators on TikTok, Fergus Ryan on ASPI’s The Strategist
Misc
At an Outback Steakhouse Franchise, Surveillance Blooms
Wired
@lmatsakis
As casual dining chains have declined in popularity, many have experimented with surveillance technology designed to maximize employee efficiency and performance. Earlier this week, one Outback Steakhouse franchise announced it would begin testing such a tool, a computer vision program called Presto Vision, at a single outpost in the Portland, Oregon area. Your Bloomin' Onion now comes with a side of Big Brother.
Military artificial intelligence can be easily and dangerously fooled
MIT Technology Review
@willknight
AI warfare is beginning to dominate military strategy in the US and China, but is the technology ready?
Events
Cyber Security Hypothetical – Panel
UNSW
We invite you to join us on 22 October, in challenging paradigms and provoking discussion around this important topic that impacts and targets us all. Cyber Security Hypothetical will be led and moderated by Mr Steve Wilson and panellists will include MAJGEN Marcus Thompson, Professor Michael Frater, Mr Alastair MacGibbon, Ms Kate Carruthers and Mr Justin Warren.
The rise of information warfare: in-conversation with Peter W. Singer
ASPI ICPC
This event for 29 October is SOLD OUT but you can watch a livestream on the ASPI facebook page - ASPI's International Cyber Policy Centre invites you to an in-conversation with Peter W. Singer and Danielle Cave to consider the rise of information warfare. Peter Warren Singer is strategist and senior fellow at New America. He has been named by the Smithsonian as one of the nation’s 100 leading innovators, by Defense News as one of the 100 most influential people in defense issues, by Foreign Policy to their Top 100 Global Thinkers List, and as an official “Mad Scientist” for the U.S. Army’s Training and Doctrine Command. A drinks and canapes reception will conclude the event. This event is kindly supported by Microsoft.
Jobs
UNIDIR Cyber Researcher – Security and Technology Programme
United Nationa Institute For Disarmament Research
We're looking for a Cyber Researcher to work on new research and other activities to contribute to the strategic goal of achieving greater cyber stability, including supporting the further development of our Cyber Policy Portal!

