Russian media outlets hacked to display casualties | China-linked hackers exposed in espionage operations | Documents allegedly reveal Ericsson bribes to ISIS
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
Hackers targeted the websites of major Russian media outlets on Monday, including the state-run news agency TASS, to display a message with the current number of Russian army casualties reported by the Ukrainian military, figures that the Russian state has not officially released to the Russian public. VICE
The “most advanced piece of malware” that China-linked hackers have ever been known to use was revealed today. Dubbed Daxin, the stealthy back door was used in espionage operations against governments around the world for a decade before it was caught. MIT Technology Review
Confidential documents have revealed how the telecoms giant Ericsson is alleged to have helped pay bribes to the Islamic State terrorist group in order to continue selling its services after the militants seized control of large parts of Iraq. The Guardian
ASPI ICPC

Ukraine-Russia
Russian State Media Hacked to Show Casualty Numbers for Russian Soldiers in Ukraine War
VICE
Joseph Cox
Hackers targeted the websites of major Russian media outlets on Monday, including the state-run news agency TASS, to display a message with the current number of Russian army casualties reported by the Ukrainian military, figures that the Russian state has not officially released to the Russian public.
‘Exploiting Cadavers ’and ‘Faked IEDs’: Experts Debunk Staged Pre-War ‘Provocation’ in the Donbas
Bellingcat
Nick Waters
With Russia’s invasion of Ukraine ongoing, it’s easy to forget the flurry of dubious provocations and staged events that appear to have been designed to implicate the Ukrainian armed forces and drum up military aggression in the days before the first shots were fired.
Belarusian hackers launch another attack, adding to chaotic hacktivist activity around Ukraine
CyberScoop
AJ Vicens
A group of Belarusian hackers and IT specialists claimed Sunday that they’d attacked the Belarusian Railways in an attempt to “slow down the transfer of occupying forces and give the Ukrainians more time to repel the attack,” according to a Google translation of the message posted to the group’s Telegram channel.
War via TikTok: Russia’s new tool for propaganda machine
AP News
David Klepper
The Russian TikTok video has it all: a cat, puppies and a pulsing background beat. It’s cute, watchable and hardly seems the stuff of state propaganda.
How digital media could help end the conflict in Ukraine
The Strategist
Adam Cullen
In Russia, dashcam footage abounds. In Ukraine, we can already tune in to live CCTV footage from major cities and witness the Russian military crossing Ukrainian borders and making its way through Crimea. But now, with Russia having invaded Ukraine, could real-time video also play a role in ending the conflict?
Archivists Make Sure the Internet Doesn’t Forget Russia’s War on Ukraine
VICE
Karl Bode
From news reports and social media posts to Ukraine University and government websites, archivists are in a mad dash to preserve the country’s online history.



Australia
National security and Russian sanctions restrict Aussie tech dreams
Australian Financial Review
John Davidson
Australian businesses, universities and academics are facing “confronting” changes to national security rules that will limit whom they can collaborate with overseas when they are working on sensitive areas of technology, Australia’s Chief Defence Scientist, Tanya Monro, has warned.
Facebook approved five obviously fake Australian election ads. Can we trust them to police the poll?
Crikey
Cam Wilson
A series of Facebook ads featuring obvious Australian election misinformation and conspiracy theories created by a tech think tank — designed to test Facebook’s filter for misinformation — were approved by the company, raising concerns about how the platform will police attempts to derail Australia’s elections.
Australia's intelligence community dismisses concerns about proposed data-gathering powers
ZDNet
Campbell Kwan
Home Affairs and three of Australia's national intelligence agencies came before a parliamentary body in a united front to give assurances that potential new powers to produce intelligence will only be used in 'niche circumstances'.
China
How China built a one-of-a-kind cyber-espionage behemoth to last
MIT Technology Review
The “most advanced piece of malware” that China-linked hackers have ever been known to use was revealed today. Dubbed Daxin, the stealthy back door was used in espionage operations against governments around the world for a decade before it was caught.
Daxin: Stealthy Backdoor Designed for Attacks Against Hardened Networks
Symantec Enterprise Blogs
New research by the Symantec Threat Hunter team, part of Broadcom Software, has uncovered a highly sophisticated piece of malware being used by China-linked threat actors, exhibiting technical complexity previously unseen by such actors. The malware appears to be used in a long-running espionage campaign against select governments and other critical infrastructure targets.
Why the Chinese Internet Is Cheering Russia’s Invasion
The New York Times
Li Yuan
As the world overwhelmingly condemns the assault on Ukraine, online opinion in China is mostly pro-Russia, pro-war and pro-Putin.
USA
Pentagon wants to bolster domestic microelectronics base with new innovation network
C4ISRNet
Courtney Albon
The U.S. Department of Defense wants to create a network of regional hubs to mature microelectronics technology and manufacturing processes and strengthen the domestic industrial base.
Hackers to NVIDIA: Remove mining cap or we leak hardware data
Bleeping Computer
Ionut Ilascu
The Lapsus$ data extortion group has released what they claim to be data stolen from the Nvidia GPU designer. The cache is an archive that is almost 20GB large. While the U.S. chipmaker giant has yet to confirm a breach on its network, the threat actor has been active with messages about the alleged hack since February 24.
Truth Social verifies white nationalist Nick Fuentes
AXIOS
Sara Fischer
Truth Social, Donald Trump's new social network, has verified an account for Nick Fuentes, who has been labeled a "white supremacist" in Justice Department filings, according to screenshots of the account shared with Axios.
North Asia
Toyota halts operations at all Japan plants due to cyberattack
Nikkei Asia
Toyota Motor announced Monday that it will halt operations at all of its plants in Japan on Tuesday, as a major supplier was hit by a suspected cyberattack, disrupting the automaker's parts supply management system.
Europe
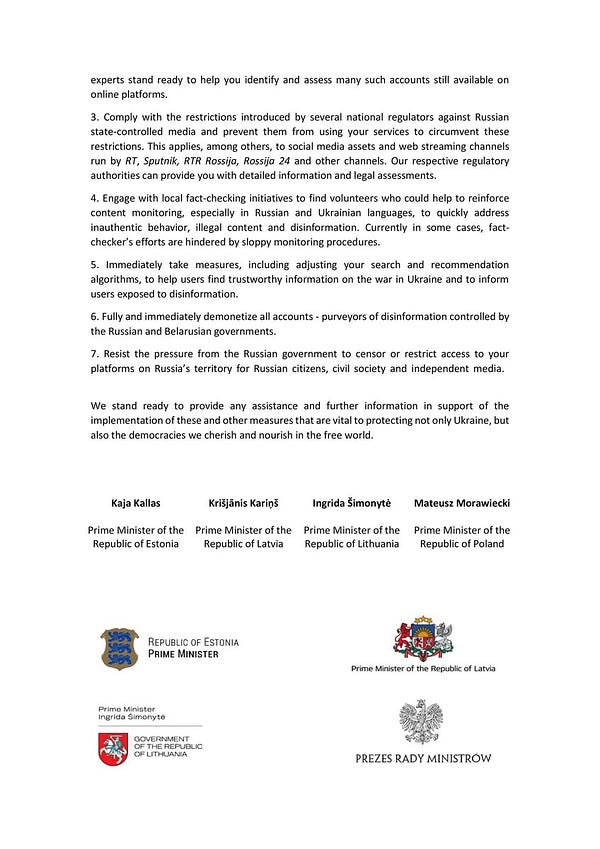
Cyberattack on NATO could trigger collective defence clause - official
Reuters
James Pearson and Jonathan Landay
A cyberattack on a NATO member state could trigger Article 5, its collective defence clause, a NATO official said on Monday, amid concerns that chaos in cyberspace around Russia's invasion of Ukraine could spill over into other territories.
Russia
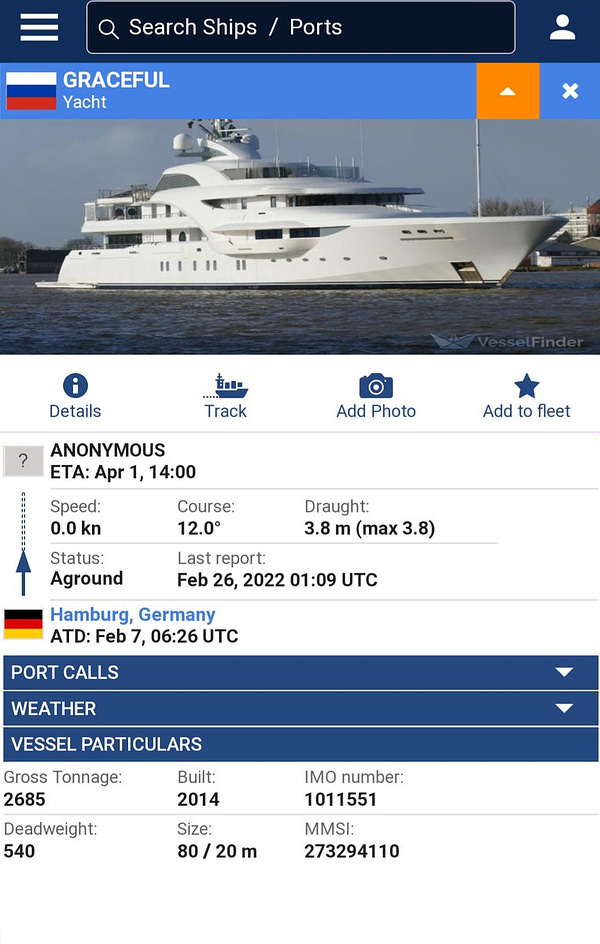
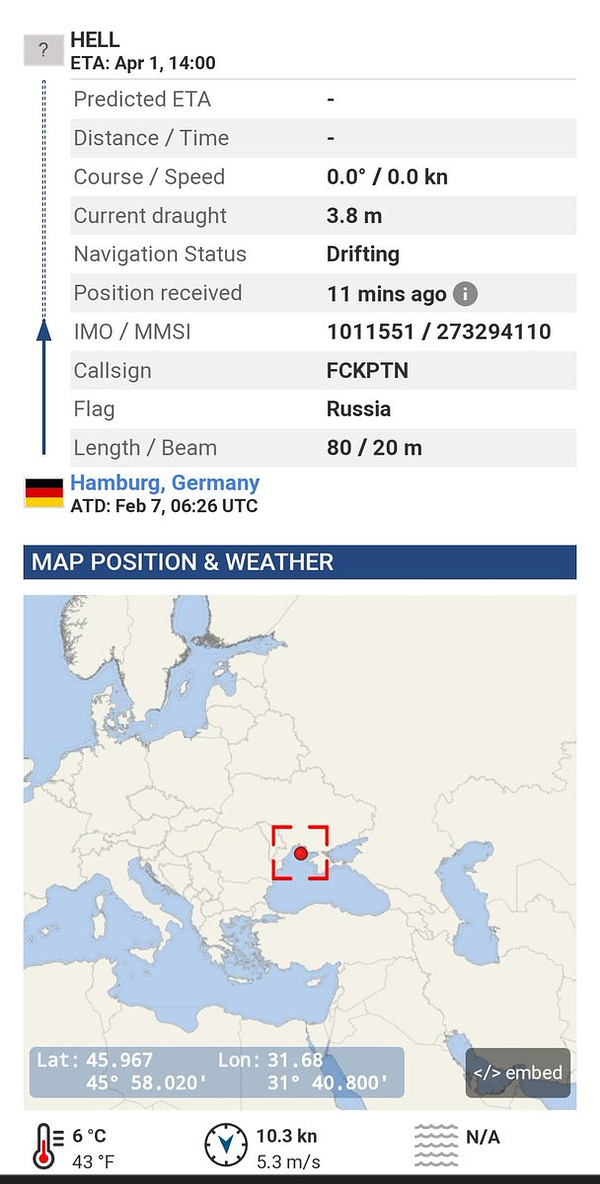
Russian Electric Vehicle Chargers Hacked, Tell Users ‘PUTIN IS A DICKHEAD’
VICE
Aaron Gordon
Electric vehicle charging stations along Russia’s M11 motorway, which stretches from Moscow to Saint Petersburg, are not working because a Ukrainian company that provided parts for the chargers hacked them using a backdoor in the chargers’ control systems, according to a Facebook post by Russian energy company Rosseti.
Conti ransomware gang chats leaked by pro-Ukraine member
The Record by Recorded Future
Catalin Cimpanu
A member of the Conti ransomware group, believed to be Ukrainian of origin, has leaked the gang’s internal chats after the group’s leaders posted an aggressive pro-Russian message on their official site, on Friday, in the aftermath of Russia’s invasion of Ukraine.
Russia: With War, Censorship Reaches New Heights
Human Rights Watch
Russian authorities have threatened to fine or block 10 Russian independent media outlets if they do not delete publications about the war in Ukraine, Human Rights Watch said today. The authorities have interfered with access to Facebook and Twitter and have blocked access to another media website.
Russian Hybrid War Report: Russia retaliates against anti-war celebrities as social platforms crack down on Russian media
Atlantic Council
As Russia expands its assault on Ukraine, the Atlantic Council’s Digital Forensic Research Lab (DFRLab) is keeping a close eye on Russia’s movements across the military, cyber, and information domains. With more than five years of experience monitoring the situation in Ukraine, as well as Russia’s use of propaganda and disinformation to undermine the United States, NATO, and the European Union, DFRLab’s global team presents the latest installment of the Russian Hybrid War Report.


Middle-East
Revealed: leaked files show how Ericsson allegedly helped bribe Islamic State
The Guardian
Rob Evans and Michael Safi
Confidential documents have revealed how the telecoms giant Ericsson is alleged to have helped pay bribes to the Islamic State terrorist group in order to continue selling its services after the militants seized control of large parts of Iraq.
Big Tech
Updates on Our Security Work in Ukraine
Meta
Nathaniel Gleicher and David Agranovich
In the last 48 hours, we uncovered a relatively small network of about 40 accounts, Pages and Groups on Facebook and Instagram. They were operated from Russia and Ukraine and targeted people in Ukraine across multiple social media platforms and through their own websites.
Facebook, Twitter remove disinformation accounts targeting Ukrainians
NBC News
Ben Collins and Jo Ling Kent
Facebook and Twitter removed two anti-Ukrainian “covert influence operations” over the weekend, one tied to Russia and another with connections to Belarus, the companies said.
Microsoft says it informed the Ukrainian government about cyberattacks
CNBC
Jordan Novet
Microsoft said Monday it’s been informing Ukraine about cyberattacks on civilian and military targets, though the software maker didn’t attribute the attacks to any specific actors.
Digital technology and the war in Ukraine
Microsoft
Brad Smith
We are fielding a growing number of inquiries about these aspects and our work, and therefore we are putting in one place a short summary about them in this blog. This includes four areas: protecting Ukraine from cyberattacks; protection from state-sponsored disinformation campaigns; support for humanitarian assistance; and the protection of our employees.
Google temporarily disables Google Maps live traffic data in Ukraine
Reuters
Elizabeth Culliford
Alphabet Inc’s Google confirmed on Sunday it has temporarily disabled for Ukraine some Google Maps tools which provide live information about traffic conditions and how busy different places are.
Crypto Donations to Ukraine Jump to $20M
CoinDesk
Sam Reynolds
The Ukraine government’s call for donations to resist the Russian invasion and provide aid to those affected has been embraced by the crypto community with nearly $20 million raised in ether and bitcoin.




Events and Podcasts
The Sydney Dialogue: Who Works? The Crisis of Automation in the Indo-Pacific
The Sydney Dialogue
In this panel discussion, speakers will discuss where the effects of automation pose the greatest challenges for the region and how we can ensure career pathways for those displaced to mitigate the risk of civil unrest and ensure that critical skills gaps do not open up and restrict growth in the long term.
The Future of Women in China: #MeToo, Censorship, and Gender Inequality
Congressional-Executive Commission on China
Recent high-profile reporting on Peng Shuai’s public sexual abuse allegations and the discovery of a mother of eight chained by the neck outside her home, as well as the Chinese government’s shocking efforts to suppress these stories, epitomizes broad trends for the status of women in China.
Obama to keynote misinformation event
AXIOS
Mike Allen
Former President Obama will give the keynote on April 21 at a forum on disinformation at the Cyber Policy Center at Stanford University’s Freeman Spogli Institute for International Studies.
Jobs
ICPC Senior Analyst or Analyst - China
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has a unique opportunity for exceptional and experienced China-focused senior analysts or analysts to join its centre. This role will focus on original research and analysis centred around the (growing) range of topics which our ICPC China team work on. Our China team produces some of the most impactful and well-read policy-relevant research in the world, with our experts often being called upon by politicians, governments, corporates and civil society actors to provide briefings and advice. Analysts usually have at least 5 years, often 7-10 years’ of work experience. Senior analysts usually have a minimum of 15 years relevant work experience and, in addition to research, they take on a leadership role in the centre and tend to be involved in staff and project management, fundraising and stakeholder engagement.
ICPC Data Analyst
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has an outstanding opportunity for talented Data Analysts to join its growing centre. ASPI’s ICPC undertakes complex research on some of the most challenging issues at the intersection of technology and public policy. How do we develop international norms to deter information operations and coercive diplomacy, how should we build international cooperation on the development of emerging critical technologies, what is the right balance between regulation and innovation? We deliver empirical research that is policy-relevant and we’re looking for people who can help us analyse data at scale.
The Sydney Dialogue - Senior Events Coordinator
ASPI ICPC
The Australian Strategic Policy Institute (ASPI) is currently recruiting for an experienced events professional to coordinate the planning and logistics of the second iteration of ASPI’s Sydney Dialogue - the world’s premier summit on emerging, critical and cyber technologies.
The Sydney Dialogue - Director
ASPI ICPC
The Australian Strategic Policy Institute (ASPI) is currently recruiting for a Director to lead the second iteration of ASPI’s Sydney Dialogue - the world’s premier summit on emerging, critical and cyber technologies.
Important disclaimer: This digest is a daily collation of material designed to provide authoritative information and commentary in relation to the subject matters covered. The views expressed in this material are those of the authors only. To provide feedback please contact: icpc@aspi.org.au




