US attributes Microsoft cyber attack to China, supported by allies and partners | Telstra discusses purchase of Digicel Pacific to block bid by China | More details on NSO Group's Pegasus spyware
Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
The Biden administration for the first time on Monday accused the Chinese government of breaching Microsoft email systems used by many of the world’s largest companies, governments and military contractors, as the United States rallied a broad group of allies to condemn Beijing for cyberattacks around the world. The New York Times
Digicel operates relatively old 3G and 4G LTE mobile networks in the South Pacific, and national security officials in Canberra are concerned China could buy its networks to spy on Australia’s closest geographical neighbours, access sensitive data and disrupt activity in Papua New Guinea, Fiji, Tonga, Vanuatu, Samoa, Nauru and Samoa. The Australian Financial Review
The editor of the Financial Times is one of more than 180 editors, investigative reporters and other journalists around the world who were selected as possible candidates for surveillance by government clients of the surveillance firm NSO Group, the Guardian can reveal. The Guardian
ASPI ICPC
Building digital government services for peak demand
The Strategist
@tomatospy
Early in the Covid-19 pandemic, the myGov website was overwhelmed when worried Australians attempted to access the service. In 2016, the online census system was taken offline on census night after problems arising from a small distributed denial-of-service attack (one designed to overwhelm a website with fake traffic). With the 2021 census coming up on 10 August, we decided to examine what lessons could be learned from these failures, especially the problem of coping with unexpected digital demand. This thinking is captured in a short ‘explainer’ report ASPI’s International Cyber Policy Centre has released today. The traditional model of government digital service delivery has tried to predict demand and then build a system that’s the right size to cope with it. Ironically, this seemingly sensible approach is destined to fail. There’s a better way to build such services.
Read our new report ‘Digital government services’.
WhatsApp and the right to encrypt
The Strategist
Anastasia Kapetas
Encrypted messaging has become a very difficult business. Despite their reach, it’s hard to make money from messaging apps. And their key service—encryption—is under constant attack from actors across the political spectrum..Services like WhatsApp, Signal and Telegram are deeply entangled in high-stakes political struggles globally over fundamental rights such privacy and peaceful dissent, legitimate law enforcement imperatives, rising authoritarianism, and the existential threats to democracies from disinformation—all happening in the increasingly vulnerable and dangerous realm of cyberspace. At the same time, encrypted messaging services are enormously popular. At least half the world’s people have at least one encrypted messaging app on their phones. Of these, WhatsApp has by far the greatest reach, used by about 90% of people in most countries.
Govt establishes ransomware taskforce
InnovationAus
The federal government has ordered its intelligence forces to go on the offensive against ransomware gangs, with a new cross-agency taskforce established and a near-tripling of the AFP officers focusing on the issue. A new taskforce, dubbed Operation Orcus, has been established, spanning across agencies including the Australian Cyber Security Centre, the Australian Federal Police, the Australian Criminal Intelligence Commission, Austrac and state and territory police forces. A report by the Australian Strategic Policy Institute released last week said that a “policy vacuum” has made Australia an “attractive market” for hackers, and that ransomware will only get worse unless there are strategic domestic efforts to prevent it.
Military fanboys' shared a video threatening nuclear war. This is why China allowed it
ABC
@Em_Dawn
A video in which the narrator threatens nuclear war with Japan has been shared by an official Chinese government account...When it comes to CCP members sharing information online, President Xi Jinping has urged all levels of the ruling party "to tell China's story", according to Jake Wallis, head of information operations and disinformation at the Australian Strategic Policy Institute.


World
U.S. Accuses China of Hacking Microsoft
The New York Times
@KannoYoungs @SangerNYT
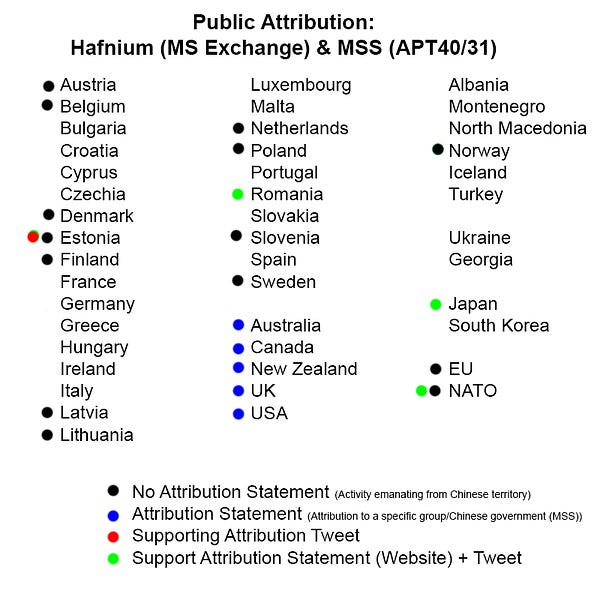
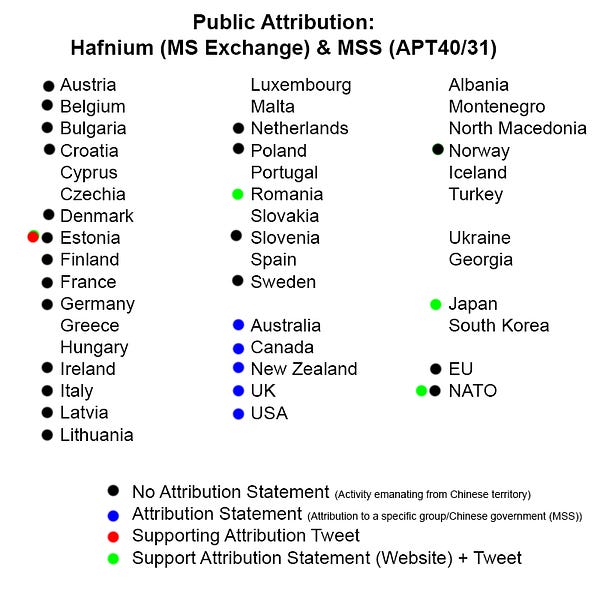
The Biden administration organized a broad group of allies to condemn Beijing for cyberattacks around the world, but stopped short of taking concrete punitive steps. The coalition of nations, which included the European Union and, for the first time, all NATO members, stopped short of punishing China, highlighting the challenges of confronting a nation with deep economic ties around the world.
The United States, Joined by Allies and Partners, Attributes Malicious Cyber Activity and Irresponsible State Behavior to the People’s Republic of China
The White House
The United States has long been concerned about the People’s Republic of China’s (PRC) irresponsible and destabilizing behavior in cyberspace. Today, the United States and our allies and partners are exposing further details of the PRC’s pattern of malicious cyber activity and taking further action to counter it, as it poses a major threat to U.S. and allies’ economic and national security. An unprecedented group of allies and partners – including the European Union, the United Kingdom, and NATO – are joining the United States in exposing and criticizing the PRC’s malicious cyber activities.
UK and allies hold Chinese state responsible for a pervasive pattern of hacking
UK Government
The UK is joining likeminded partners to confirm that Chinese state-backed actors were responsible for gaining access to computer networks around the world via Microsoft Exchange servers.
Australia joins international partners in attribution of malicious cyber activity to China
Australian Government
Today, the Australian Government joins international partners in expressing serious concerns about malicious cyber activities by China's Ministry of State Security. In consultation with our partners, the Australian Government has determined that China's Ministry of State Security exploited vulnerabilities in the Microsoft Exchange software to affect thousands of computers and networks worldwide, including in Australia. These actions have undermined international stability and security by opening the door to a range of other actors, including cybercriminals, who continue to exploit this vulnerability for illicit gain.China: Declaration by the High Representative on behalf of the European Union urging Chinese authorities to take action against malicious cyber activities undertaken from its territory
Council of the European Union
Today, the EU and its member states, together with partners, expose malicious cyber activities that significantly affected our economy, security, democracy and society at large. The EU and its member states assess these malicious cyber activities to have been undertaken from the territory of China.Statement by the North Atlantic Council in solidarity with those affected by recent malicious cyber activities including the Microsoft Exchange Server compromise.
NATO
We observe with increasing concern that cyber threats to the security of the Alliance are complex, destructive, coercive, and becoming ever more frequent. This has been recently illustrated by ransomware incidents and other malicious cyber activity, targeting our critical infrastructure and democratic institutions, as well as exploiting weaknesses in hardware and software supply chains.New Zealand condemns malicious cyber activity by Chinese state-sponsored actors
New Zealand Government
New Zealand has established links between Chinese state-sponsored actors known as Advanced Persistent Threat 40 (APT40) and malicious cyber activity in New Zealand.
Tactics, Techniques, and Procedures of Indicted APT40 Actors Associated with China’s MSS Hainan State Security Department
US Cybersecurity & Infrastructure Security Agency
APT40—aka BRONZE MOHAWK, FEVERDREAM, G0065, Gadolinium, GreenCrash, Hellsing, Kryptonite Panda, Leviathan, MUDCARP, Periscope, Temp.Periscope, and Temp.Jumper—is located in Haikou, Hainan Province, People’s Republic of China (PRC), and has been active since at least 2009. APT40 has targeted governmental organizations, companies, and universities in a wide range of industries—including biomedical, robotics, and maritime research—across the United States, Canada, Europe, the Middle East, and the South China Sea area, as well as industries included in China’s Belt and Road Initiative.
FT editor among 180 journalists identified by clients of spyware firm
The Guardian
@davidtpegg @paullewis @safimichael @ninalakhani
The editor of the Financial Times is one of more than 180 editors, investigative reporters and other journalists around the world who were selected as possible candidates for surveillance by government clients of the surveillance firm NSO Group, the Guardian can reveal.
Amazon Shuts Down NSO Group Infrastructure
VICE
@josephfcox
Amazon Web Services (AWS) has shut down infrastructure and accounts linked to Israeli surveillance vendor NSO Group, Amazon said in a statement. The move comes as a group of media outlets and activist organizations published new research into NSO's malware and phone numbers potentially selected for targeting by NSO's government clients.
Pegasus Spyware: Does Apple Have ‘Major’ iMessage Security Problems?
Forbes
@iblametom
iPhone spyware made by $1 billion surveillance company NSO has exposed “major” issues in Apple iMessage security, according to a security expert who has spent years researching the Israeli business’ hacks.
The Rise and Fall of NSO Group
Forbidden Stories
@AudreyTravere
Ever since the brazen assassination of Saudi journalist and dissident in Turkey five months earlier, the Israeli spyware company had been thrust into an uncomfortable spotlight. NSO Group had dealt with scandals before, but this time the accusations were of a different magnitude. The company had been accused by a friend of the murdered journalist of having sold its spyware tool to Saudi Arabia, which then used it to intercept messages between the two dissidents in the weeks and months leading up to Khashoggi’s assassination.
Australia
Telstra in Digicel talks that could block China in Pacific
The Australian Financial Review
@LucasBairdAus @Johnkehoe23
Telstra has confirmed it is in discussions to buy Digicel Pacific in partnership with the federal government, in a potential deal understood to be worth almost $2 billion and which would seek to block a possible bid by China to acquire the mobile network assets, after The Australian Financial Review revealed the approach last week.
Telstra caught in China row
The Australian Financial Review
@LucasBairdAus @Johnkehoe23 @andrewtillett
Telstra shareholders and analysts are alarmed the telco giant could be used as a Morrison government foreign policy tool to outbid China in buying the Digicel Pacific phone network in neighbouring island countries, via a $2 billion taxpayer-backed consortium.
Race on for Australian rare earth supplies as fears grow over China's market 'monopoly'
ABC
@dk_mercer
Critical minerals needed to drive modern economies and tackle climate change could be cut off to Australia and its allies as tensions with China escalate further, experts say.
China
Spokesperson of the Chinese Mission to the EU Speaks on a Question Concerning the Statements from the EU and NATO on the So-called Chinese Malicious Cyber Activities
Mission of the People's Republic of China to the European Union
We have taken note of the statements. China is a firm defender of cybersecurity and always opposes and cracks down on cyber attacks launched within China or using Chinese cyber facilities in accordance with the law. The allegations in the statements by the EU and NATO are not based on facts and evidence, but speculation and groundless accusations. We express our strong disapproval of and firm opposition to such statements.
Farewell to a Community of Common Destiny?
The Wire China
@vshih2
Beijing's regulatory crackdown on tech companies threatens to break up the transnational community that allowed China's homegrown tech sector to thrive.


What China Expects From Businesses: Total Surrender
The New York Times
@LiYuan6
Unlike regulators in Europe and the U.S., Beijing is using the guise of antitrust to bring powerful tech companies into line with its priorities.
Read our new report ‘Reigning in China's Technology Giants’.
How China Transformed Into a Prime Cyber Threat to the U.S.
The New York Times
@nicoleperlroth
Over the past decade, China reorganized its hacking operations, turning into a sophisticated and mature adversary.
USA
Congress Takes Aim at China’s Recruitment of Talent in U.S.
Bloomberg
@DanielPFlatley @JanetLorin
Congress is aiming to hobble China’s ability to recruit scientists and academics in the U.S. as part of broader moves in Washington to confront the Asian nation’s growing clout. A recently passed House bill to bolster American research and development would bar scientists and academics from participating in U.S.-funded research projects if they are also receiving support from Beijing.
Four Chinese Nationals Working with the Ministry of State Security Charged with Global Computer Intrusion Campaign Targeting Intellectual Property and Confidential Business Information, Including Infectious Disease Research
US Department of Justice
A federal grand jury in San Diego, California, returned an indictment in May charging four nationals and residents of the People’s Republic of China with a campaign to hack into the computer systems of dozens of victim companies, universities and government entities in the United States and abroad between 2011 and 2018.




The Biden/Facebook Fight Is Part Of The Problem
Galaxy Brain
@cwarzel
This back and forth between Facebook and the White House — conducted through the press — is a good example of an unproductive, false binary of a conversation on a complex topic that deserves far more nuance. Ironically, the argument is a great example of social media-influenced and flattened discourse that is poisoning us all.
Company That Aims to Solve the 'Crisis of Toxicity Online' Makes Money From the Daily Caller and Ben Shapiro
Gizmodo
@swodinsky
Covid conspiracists, climate change deniers, and Ben Shapiro are just a few of the figures you'll find using OpenWeb's tech .
Cyber Games Offer Competitive Challenges
Security Boulevard
Nathan Eddy
With high-profile public and private institutions in the U.S. facing a growing threat from cybercriminals and cyberattacks, there is a growing push to prepare the next generation of potential IT security pros to meet the challenges.
North Asia
‘Historical Distortions’ Test South Korea’s Commitment to Free Speech
The New York Times
@choesanghun
Conspiracy theories about the country’s turbulent past have spread online. Now the government is pushing criminal penalties to crack down on misinformation.
New Zealand & The Pacific
State to reduce duty, VAT on digital equipment
The Fiji Times
Felix Chaudhary
Government will reduce duties and VAT on digital equipment to help people work and study safely from home as much as possible. Attorney-General Aiyaz Sayed-Khaiyum said this during the 2021-2022 National Budget address in Parliament last night. He said the reductions would be on digital equipment needed for conferencing, collaboration and distance learning, which would be imported at a rate of free fiscal, free import excise and 9 per cent VAT.
South and Central Asia
Key Modi rival Rahul Gandhi among potential Indian targets of NSO client
The Guardian
The Indian prime minister Narendra Modi’s most prominent political rival, the opposition figure Rahul Gandhi, was twice selected as a potential surveillance target in leaked phone number data, making him one of dozens of Indian politicians, journalists, activists and government critics whose numbers were identified as possible targets for the Israeli company’s government clients.
UK
Britain to build space base to monitor satellite threats from Russia and China
The Independent
A new space base will be built in Britain to monitor the “irresponsible and reckless” threats made to satellites by Russia and China, the head of the Royal Air Force has said.
Europe
Technology Adoption: Are we too late to the party?
Small Wars Journal
@JanHavranek2 @DanielBagge1
NATO and the West are experiencing a reversed kind of revolution in military affairs with new technologies bearing far-reaching implications beyond the conduct of war.
Events
Indigenous Cyber and Digital Skills Conference
ASPI’s IndigiCyber, Defence and Space Program
This half-day conference will canvas a range of curriculum and engagement initiatives in cyber-security and STEM as well as government and industry responses to both support those already in work, and to attract diverse candidates. What can defence, and defence-related sectors, do to support the next generation of technology champions? 23 Jun 2021 9:00 am - 1:00 pm
ASPI Webinar: In-Conversation with Marietje Schaake
ASPI ICPC
SPI's International Cyber Policy Centre is delighted to invite you to an in-conversation with Marietje Schaake, President of the Cyber Peace Institute, the International Policy Director at Stanford's Cyber Policy Center and International Policy Fellow at Stanford’s Institute for Human-Centered Artificial Intelligence. Join Fergus Hanson for an online ‘fireside chat’ with Marietje focusing on technology, democracy and the question of accountability. They will discuss how democracies can cooperate amidst rising authoritarianism and the privatised governance of technologies. They will also consider the rule of law and how it relates to the oversight of existing and emerging technologies. 27 July 2021 5:00 pm - 6:00 pm

Jobs
ICPC Senior Analyst or Analyst - Information operations & disinformation
ASPI ICPC
ASPI’s International Cyber Policy Centre has an outstanding opportunity for a talented and proactive senior analyst or analyst to join its centre. The successful candidate will work with a small, high-performing team to produce original research and analysis centred around policy responses to information operations and disinformation by state and non-state actors. They will also work with senior staff in the centre to engage globally with governments, social media and Internet companies.
ICPC Senior Analyst or Analyst - China
ASPI ICPC
ASPI’s International Cyber Policy Centre (ICPC) has a unique opportunity for exceptional and experienced China-focused senior analysts or analysts to join its centre. This role will focus on original research and analysis centred around the (growing) range of topics which our ICPC China team work on. Our China team produces some of the most impactful and well-read policy-relevant research in the world, with our experts often being called upon by politicians, governments, corporates and civil society actors to provide briefings and advice. Analysts usually have at least 5 years, often 7-10 years’ of work experience. Senior analysts usually have a minimum of 15 years relevant work experience and, in addition to research, they take on a leadership role in the centre and tend to be involved in staff and project management, fundraising and stakeholder engagement.