US Senators Urge $1 Billion Plan to Loosen China’s Grip on 5G | Russians Hacked Ukrainian Gas Company at Center of Impeachment | Malcolm Turnbull intervenes in UK's Huawei debate


Follow us on Twitter. The Daily Cyber Digest focuses on the topics we work on, including cyber, critical technologies & strategic issues like foreign interference.
A bipartisan group of U.S. senators, alarmed by the rise of Chinese electronics supplier Huawei Technologies Inc., wants Washington to subsidize firms that could counter China’s 5G advances. WSJ
Russian military hackers have been boring into the Ukrainian gas company at the center of the impeachment trial, according to security experts. The hacking attempts against Burisma, the Ukrainian gas company on whose board Hunter Biden served, began in early November, as talk of the Bidens, Ukraine and impeachment was dominating the news in the United States. NYT
Former Australian prime minister Malcolm Turnbull has warned Boris Johnson that allowing Chinese company Huawei to build Britain's 5G network would compromise the ability of the Five Eyes countries to collect and share intelligence. Mr Turnbull responded to the UK Prime Minister's challenge issued earlier that critics of Huawei should offer alternatives. SMH
ASPI ICPC
ASPI’s International Cyber Policy Centre is delighted to announce that the centre has joined the Carnegie Endowment for International Peace’s new Partnership for Countering Influence Operations. As a founding partner in this new initiative, the centre will collaborate closely with governments, the tech industry, media, academia and civil society to help Carnegie’s Partnership for Countering Influence Operations advance more effective whole-of-society, evidence-based strategies to counter influence operations. Dr Jake Wallis – who started at the Centre in 2019 and is part of a growing team working in this space – will represent the Centre in this new partnership initiative. Other partners in this new Carnegie-led initiative include the Hewlett Foundation, Stanford University, Microsoft, Mozilla, Facebook, Twitter and SaferNet.
Recent publications this team has published include work on PRC-linked information operations in Hong Kong and doxxing the pro-democracy movement in Hong Kong; a joint BBC-ASPI investigation into information operations in West Papua; Hacking democracies & cyber-enabled attacks on elections; disinformation methodologies and junk news sites; Chinese and Russian information warfare techniques; ‘political warfare’ and preparing for the right kind of conflict; Content, ideas and cyber – the sleeper in our national security defences.
How to make the internet safe for democracy
ASPI Strategist
We are in the midst of a major rethinking of that inherited body of law in light of the changes wrought by digital technology. Economists and legal scholars are beginning to recognise that consumers are hurt by things like lost privacy and forgone innovation, as Facebook and Google sell users’ data and buy start-ups that might challenge them. But the political harms are critical issues as well, and ought to be considered in antitrust enforcement. Social media have been weaponised to undermine democracy by deliberately accelerating the flow of bad information, conspiracy theories and slander. Only the internet platforms have the capacity to filter this garbage out of the system. But the government cannot delegate to a single private company (largely controlled by a single individual) the task of deciding what is acceptable political speech.
Bushfires, bots and the spread of disinformation
ASPI Strategist
@elisethoma5
As fire continues to wreak havoc across large parts of the country, online Australia is battling another crisis: the waves of misinformation and disinformation spreading across social media. Much of the media reporting on this has referred to ‘bots and trolls’, citing a study by Queensland University of Technology researchers which found that about a third of the Twitter accounts tweeting about a particular bushfire-related hashtag showed signs of inauthentic activity.

World
Here’s how to regulate artificial intelligence properly
The Washington Post
@R_D
From Brussels to Beijing, the Élysée to the Oval Office, leaders around the world are calling for bold regulations to govern artificial intelligence (AI).
A New UN Cybercrime Treaty? The Way Forward for Supporters of an Open, Free, and Secure Internet
CFR
The cybercrime threat continues to grow and governments are largely failing to bring perpetrators to justice. More cooperation among states is needed. With the Russian resolution passing, supporters of an open, free, and secure internet should dedicate greater efforts to win over the undecided countries. Failing to do so is a win for cybercriminals and the governments that support them.

Australia
(Australian Prime Minister Scott Morrison’s Message to the Raisina Dialogue 2020)
China
In technology, where China leads, the rest of the world follows
Nikkei Review
@hennysender
Of course, the most notorious use of surveillance technology in China is in the Xinjiang region, where the central government has created a network of cameras, checkpoints and deep digital databases to spy on and control millions of Uighurs and other Muslim ethnic minorities. We are now seeing a similar tight grip through technology in India. After his overwhelming mandate in the May general elections, Prime Minister Narendra Modi has become far more authoritarian.
Megvii takes big step towards $500m Hong Kong listing
FT
Megvii, the $4bn Chinese facial recognition company under US sanctions, has cleared a big hurdle on its way to a Hong Kong stock market debut, putting its $500m initial public offering back on track. The stock exchange’s 27-member listing committee has cleared Megvii to publish a new prospectus, according to people involved in the process. The bourse said in November that the company had to provide more information about the effect of US sanctions on its operations. The decision does not constitute formal approval to list, said the people, but it revives a process that was threatened after the US commerce department put Megvii on a blacklist last year on the grounds of alleged human rights abuses in China’s Xinjiang province.
USA
Silicon Valley and National Security
US Department of State
I want to talk to you about one specific topic today, the challenges and opportunities that the United States has with China. We need to think bigger, perhaps, and better as well. Because I am convinced that we can cooperate with China, as this administration has shown with what I hope will be in the next several hours the signing of a phase one trade deal. That’s a fantastic thing, I believe, for the United States. We’d welcome more of it. But we also have to honestly confront tough questions about the national security consequences of doing business in a country controlled by the Chinese Communist Party. That especially goes for companies that develop some of our most sensitive technology, as many do here in this region.
Senators Urge $1 Billion Plan to Loosen China’s Grip on 5G
WSJ
@drewfitzgerald
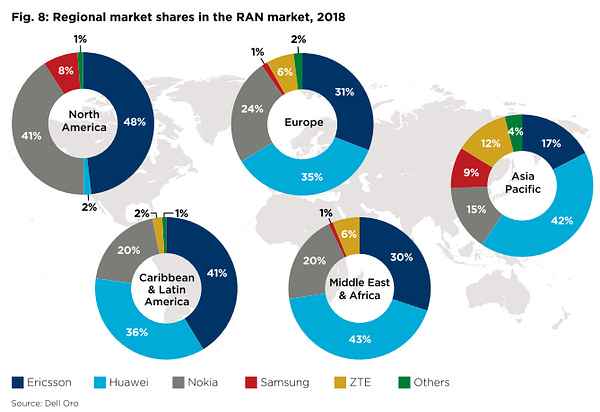
A bipartisan group of U.S. senators, alarmed by the rise of Chinese electronics supplier Huawei Technologies Inc., wants Washington to subsidize firms that could counter China’s 5G advances. The proposed Utilizing Strategic Allied Telecommunications Act would steer at least $750 million toward companies developing fifth-generation, or 5G, wireless technology and would create a separate $500 million fund for companies that deploy “trusted and secure” equipment around the world. Sens. Richard Burr (R-N.C.) and Mark Warner, (D-Va.), who leads the Senate’s intelligence committee, introduced the bill.
Sen. Warner presses state department to address cyber activity by Iran
ABC
U.S. Sen. Mark R. Warner voiced deep concerns with the ability of the U.S. Department of State to address the cyber activity by Iran Tuesday, Jan. 14.
As Justice Department Pressures Apple, Investigators Say iPhone Easier to Crack
WSJ
The escalation of a long-running encryption conflict between the Justice Department and Apple Inc. has puzzled security experts who say that new hacking tools have made it possible to gain access to many of the company’s devices in criminal investigations.
NSA found a dangerous Microsoft software flaw and alerted the firm — rather than weaponizing it
The Washington Post
The National Security Agency recently discovered a major flaw in Microsoft’s Windows operating system — one that could potentially expose computer users to significant breaches, surveillance or disruption — and alerted the firm of the problem rather than turn it into a hacking weapon, officials announced Tuesday.
Windows Vulnerabilities That Require Immediate Attention
This afternoon, NSA issued Emergency Directive 20-02, which instructs most Federal civilian Executive Branch agencies to apply the security updates Microsoft released in today’s Patch Tuesday.
UK
An unsecured database exposed thousands of British passports
Wired
@njkobie
An open Amazon Web Services S3 database held passport scans, tax documents, job applications and other sensitive personal details. It has now been taken offline by Amazon.
It would be an issue: Malcolm Turnbull intervenes in UK's Huawei debate
SMH
@latikambourke
Former Australian prime minister Malcolm Turnbull has warned Boris Johnson that allowing Chinese company Huawei to build Britain's 5G network would compromise the ability of the Five Eyes countries to collect and share intelligence. Mr Turnbull responded to the UK Prime Minister's challenge issued earlier that critics of Huawei should offer alternatives. Johnson's National Security Council (NSC) is due to make a decision within a fortnight, nearly 12 months after the original determination was due.
Europe
Europe urged to use industrial data trove to steal march on rivals
FT
EU officials think innovation will be increased if data can be transferred more freely & public data is re-used as much as possible. Discussions have not been settled but a formal announcement on the strategy is expected in early March.
Russia
Russians Hacked Ukrainian Gas Company at Center of Impeachment
NYT
@nicoleperlroth @AllMattNYT
With President Trump facing an impeachment trial over his efforts to pressure Ukraine to investigate former Vice President Joseph R. Biden Jr. and his son Hunter Biden, Russian military hackers have been boring into the Ukrainian gas company at the centre of the affair, according to security experts. The hacking attempts against Burisma, the Ukrainian gas company on whose board Hunter Biden served, began in early November, as talk of the Bidens, Ukraine and impeachment was dominating the news in the United States. It is not yet clear what the hackers found, or precisely what they were searching for. But the experts say the timing and scale of the attacks suggest that the Russians could be searching for potentially embarrassing material on the Bidens — the same kind of information that Mr Trump wanted from Ukraine when he pressed for an investigation of the Bidens and Burisma, setting off a chain of events that led to his impeachment.
Middle East
Cut Undersea Cable Plunges Yemen Into Days-Long Internet Outage
Wired
@lilyhnewman
Last week, the internet went dark for Yemen and its 28 million citizens. It's still not fully back today. In fact, the entire Red Sea region has dealt with slow to nonexistent connectivity since the severing of a single submarine cable on Thursday.
Stop NSO Group exporting spyware to human rights abusers
Amnesty International
Israel must revoke the export license of NSO Group whose spyware products have been used in malicious attacks on human rights activists around the world, Amnesty International said ahead of the latest court case to embroil the tech firm.
Misc
Out of Control
Forbruker Radet
How consumers are exploited by the adtech industry - and what we are doing to make it stop. In this report, we demonstrate how every time we use our phones, a large number of shadowy entities that are virtually unknown to consumers are receiving personal data about our interests, habits, and behaviour.
Grindr and OkCupid Spread Personal Details, Study Says
NYT
Norwegian research raises questions about whether certain ways of sharing information violate data privacy laws in Europe and the United States.
Events
U.S.-Taiwan Tech Challenge
Disinfo cloud
The U.S.-Taiwan Tech Challenge invites technologists from across East Asia Pacific to submit an application to present their solution against adversarial disinformation and propaganda to an audience of government, civil society, and private sector stakeholders. Eight organizations will be chosen to demo their technology. Up to three organizations will be selected as winners of the Challenge and will receive funding. Applications for Day 1 are due by January 21, 2020.



